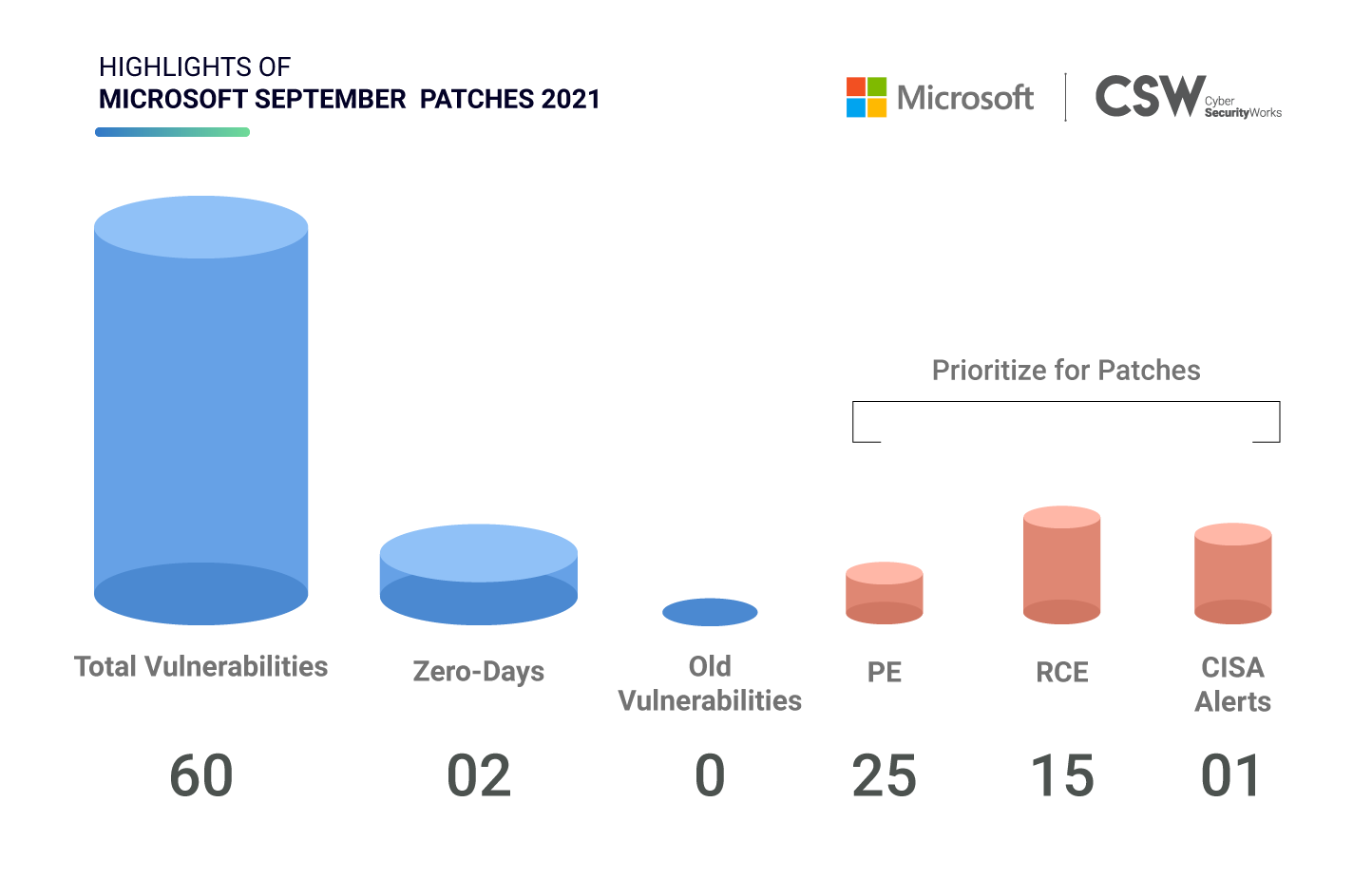
Microsoft patched 60 unique security vulnerabilities in September 2021, which includes two zero-day exploits. We analyzed these weaknesses and spotlighted the most important vulnerabilities that ought to be fixed on priority.
Microsoft Patches: Overview
This September, Microsoft patched 60 vulnerabilities discovered in 2021.
-
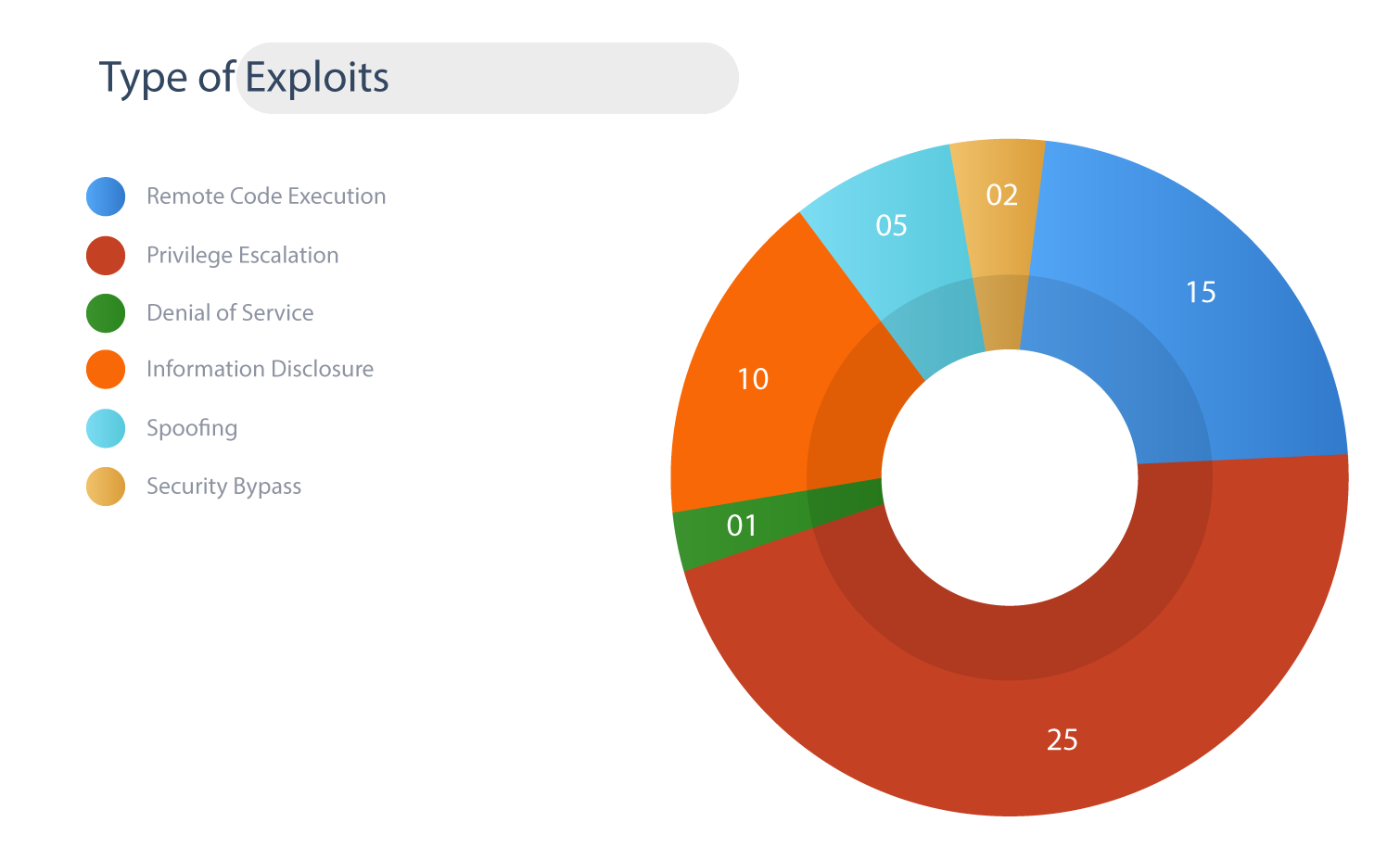
15 CVEs are classified as Remote Code Execution bugs
-
25 CVEs with Privilege Escalation capabilities
-
10 CVEs are linked to Information Disclosure
-
1 CVEs have Denial of Service ability
-
5 CVEs has Spoofing possibilities
-
2 CVEs are Security Bypass bugs
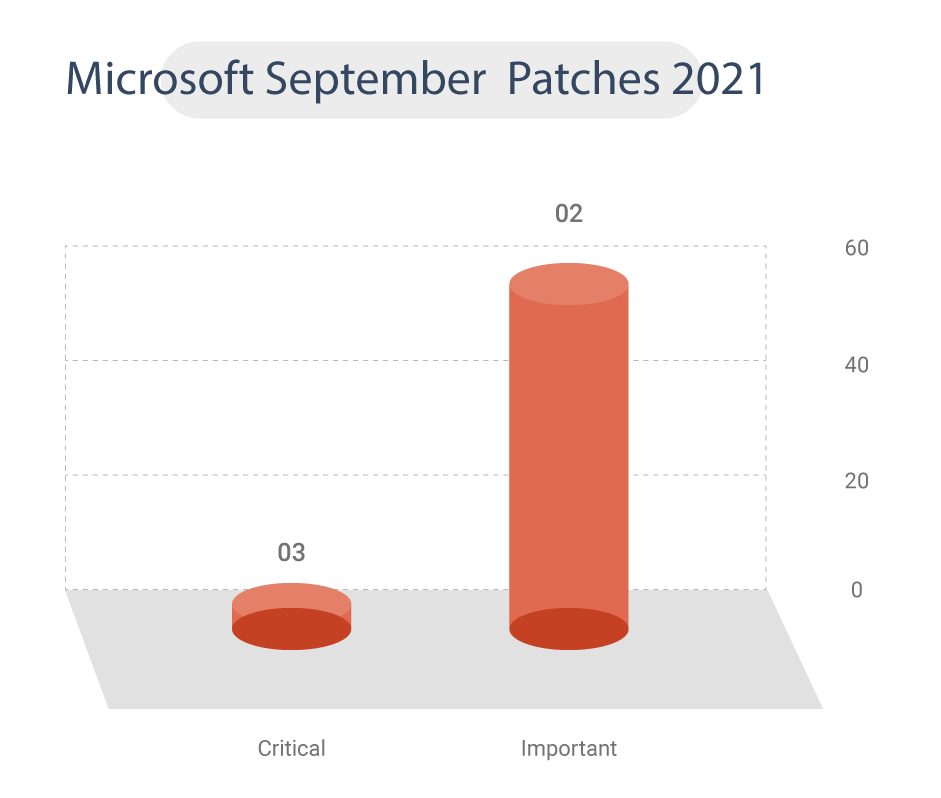
Zero-days
On September 14, Microsoft had published a new zero-day (CVE-2021-40444) with remote code execution vulnerability in Windows MSHTML that threat actors are actively exploiting using phishing attacks. These attacks spread malicious Word documents leveraging the CVE-2021-40444 vulnerability, that downloaded and executed a malicious DLL file on the victim’s device.
This critical zero-day vulnerability, also known as Trident, had received a security update as a part of the September patch release and was assigned a CVSS v3 score of 8.8 (high). According to Microsoft, the effect of this vulnerability would be greater if the attacker had administrator access.
Meanwhile, several PoC have been released in GitHub repositories for this flaw and CISA has also issued an alert to patch this vulnerability.
PrintNightmare Fixed Again: The sixth chapter of the PrintNightmare (CVE-2021-36968) series has come to an end this month with a fix. This CVE has a CVSS v3 score of 7.8 (high) and allows attackers to gain elevation of privilege that impacts Windows 7 and Server 2008 / Server 2008 R2. The availability of functional exploit codes and public disclosures puts further urgency on this month’s Windows OS updates.
RCE/PE
In this month’s round of patches, there are 15 CVEs classified as Remote Code Execution, and 25 CVEs have Privilege Escalation capabilities. These include three critical vulnerabilities (CVE-2021-26435, CVE-2021-38647, CVE-2021-36965), which are classified as RCE bugs.
Four Microsoft zero-day vulnerabilities (CVE-2021-38647, CVE-2021-38648, CVE-2021-38645 and CVE-2021-38649) in the Azure cloud platform’s Open Management Infrastructure (OMI) – collectively dubbed as “OMIGOD”- affects thousands of Azure customers and millions of endpoints, according to Wiz. These flaws carry a CVSS v3 score range of 7.1 to 9.8.
Product Analysis
The products impacted in the September patch bundle include Azure Open Management Infrastructure, Azure Sphere, Office Excel, PowerPoint, Word, and Access; the kernel, Visual Studio, Microsoft Windows DNS, and BitLocker, among other software. Of these, Windows Server receives the highest number of fixes this month.
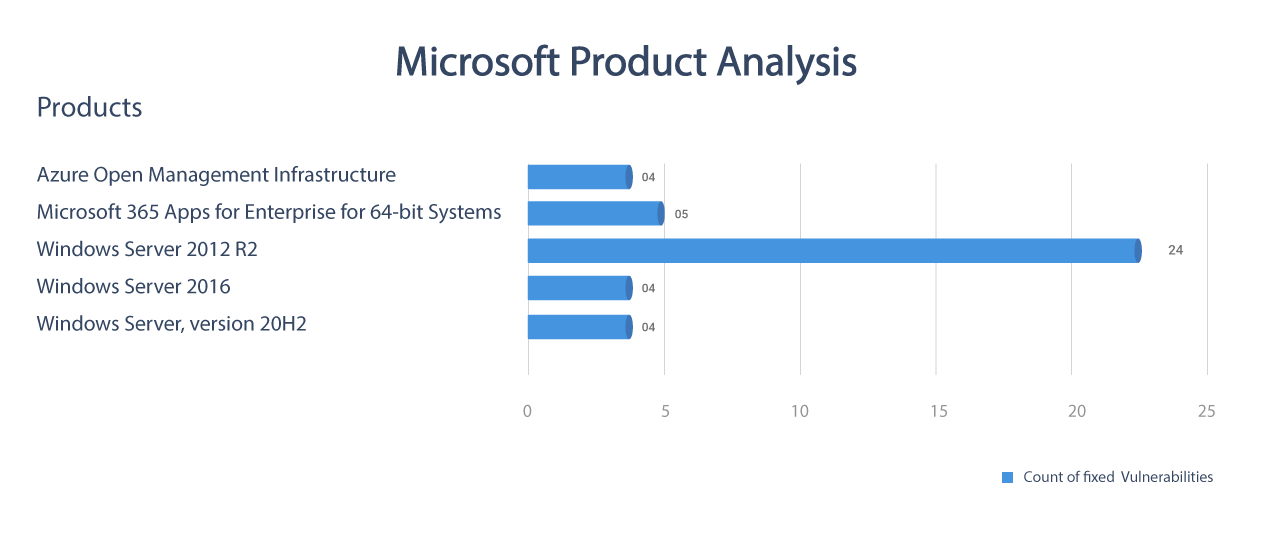
Table: Microsoft September Patches 2021
We urge Microsoft users to continue to prioritize the security updates to these flaws and recommend them to update their environment as soon as possible to ensure all endpoints are secured.
Concerned about a cyber-attack?
Want to know more about Vulnerability Management as a Service.









