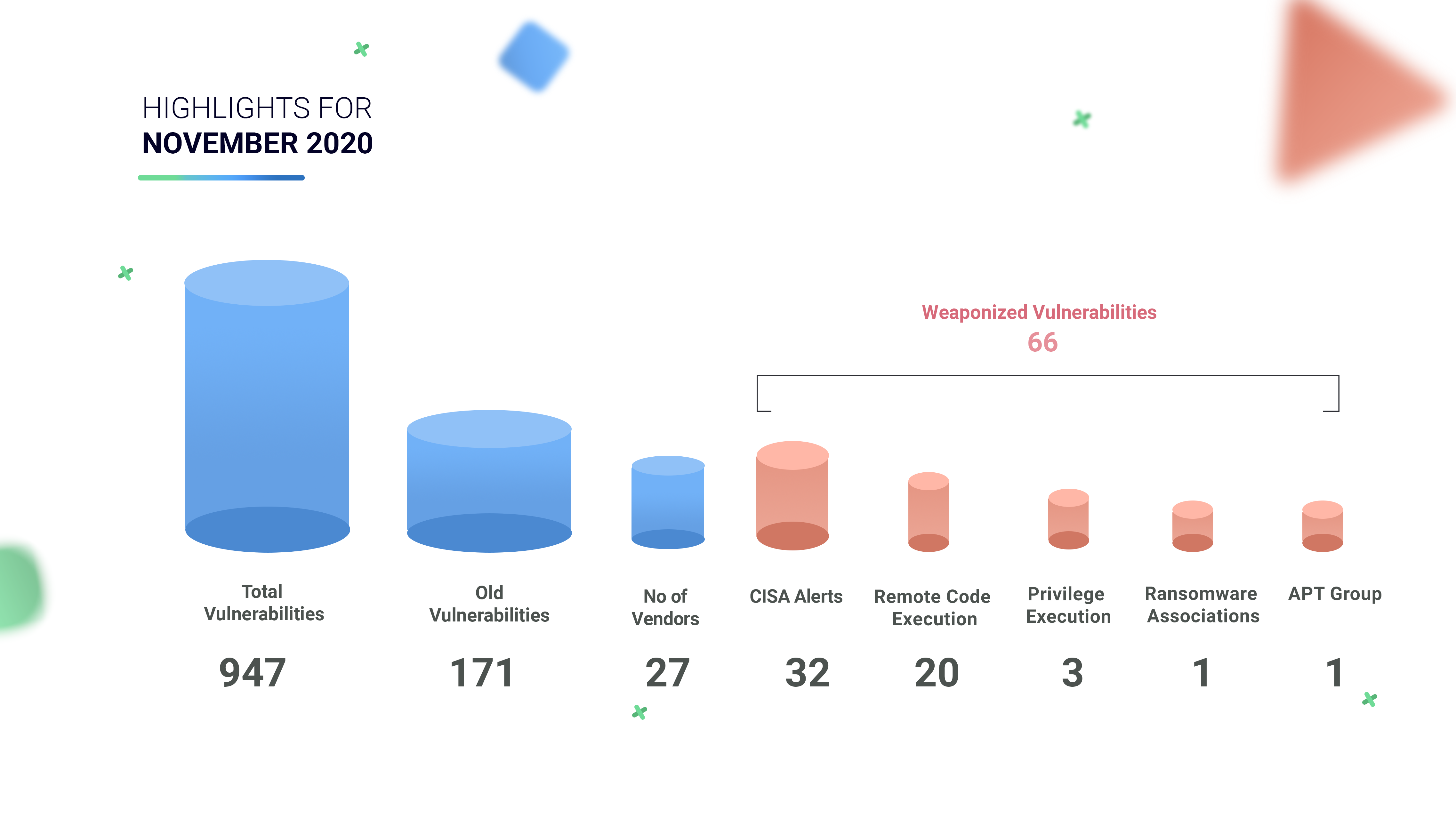
Highlights of November Digest
-
CISA has released an alert for 86 vulnerabilities that got patched this month.
-
171 Old vulnerabilities have been patched this month and 5 CVEs have RCE and PE capabilities.
-
20 CVEs have Remote code Execution flaws
-
3 CVEs have PE Capabilities
-
29 CVEs are Web app exploits
-
5 CVEs can be exploitable in any form
-
6 CVEs are associated with Denial of Service
-
2 CVEs are linked with Local exploits, and 1 CVE can be exploited in the form of File upload.
Table 1: Weaponized Vulnerabilities
-
Out of 86 CVEs, 11 are publicly exploitable vulnerabilities.
-
5 CVEs are ranked critical, 15 with high severity, 40 of medium, 13 of low severity, and 13 with unknown severity.
Table 2: CISA Alerts
-
24 CVEs are associated with Remote Code Execution hence patching these would be optimum.
-
Of these, 17 are critical, 93 are important, and two are low in severity.
-
CVE-2020-17087 – This is a Zero-day bug, an actively exploitable vulnerability with PE capabilities.
-
CVE-2020-17087 exists in Windows Kernel Cryptography Driver, which facilitates a locally accessible attack surface.
-
When CVE-2020-15999 (a type of memory-corruption vulnerability) and CVE-2020-17087 are linked together, it would allow an attacker to break out of Google Chrome’s sandbox.
Table 3: Microsoft November Patches
-
CVE-2018-7600 is associated with the Sea turtle APT group and Satan ransomware.
-
22 CVEs are weaponized with publicly known exploits.
-
6 CVEs are rated critical, 37 are high, and 100 are medium.
-
17 CVEs have been issued a warning alert by CISA.
Table 4: Old Vulnerabilities
According to the Threat landscape report, 63% of unpatched vulnerabilities belong to 2018 and earlier period. Therefore, organizations are recommended to adopt patch management solutions as early as possible.
Table 5: Vulnerabilities yet to be weaponized
Cybercriminals often target unpatched vulnerabilities and publicly known exploits to deploy cyberattacks. Maintain good cyber hygiene practices by patching or upgrading vulnerable systems and stay safe.
Happy Patching
Team CSW









