In this blog we will be taking a look at the CVEs that need to be patched by March 10, 2023. Let’s look at the analysis of all the vulnerabilities below:
Why are these CVEs important?
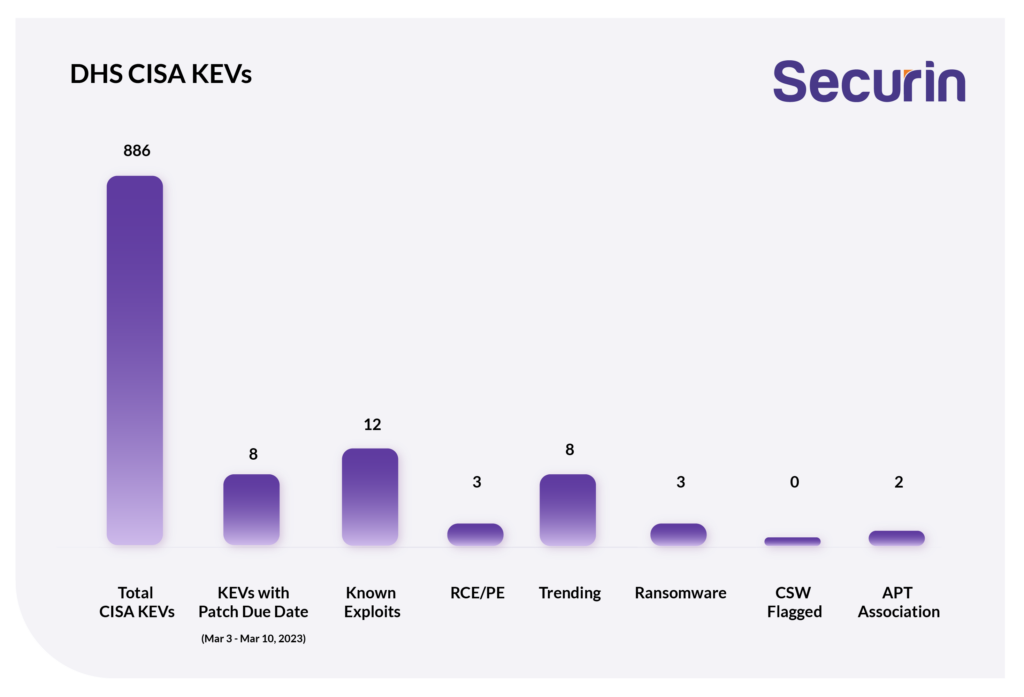
From our analysis, we found that
-
All 8 vulnerabilities are weaponized and have been exploited in the wild.
-
CVE-2023-23376, CVE-2023-21823, and CVE-2023-21715 are Microsoft vulnerabilities that can be exploited to gain privilege escalation. All three vulnerabilities have publicly exposed exploit concepts.
-
CVE-2023-23529 is Apple’s type confusion issue that can be exploited for arbitrary code execution by getting the targeted user to access a malicious website. It is actively being exploited now.
-
CVE-2022-46169 is a critical command injection flaw found in the Cacti monitoring solution. It allows an unauthenticated user to execute arbitrary code on a server running Cacti, if a specific data source was selected for any monitored device. Since an exploit for it was published, attackers have been actively exploiting this vulnerability in Cacti. CVE-2022-46169 was patched in December 2023.
-
CVE-2023-0669 is the much exploited Fortra GoAnywhere MFT Remote Code Execution Vulnerability. Clop ransomware has breached more than 130 organizations by exploiting this vulnerability.
-
CVE-2022-24990 is a remote command execution vulnerability that allows an unauthenticated user to execute commands on the target endpoint. It has been exploited by North Korean threat actors in attacks on the healthcare sector.
-
CVE-2015-2291 is an Intel driver vulnerability. Russian threat actors exploited this vulnerability to load a malicious driver designed to reduce the token integrity of Microsoft Defender.
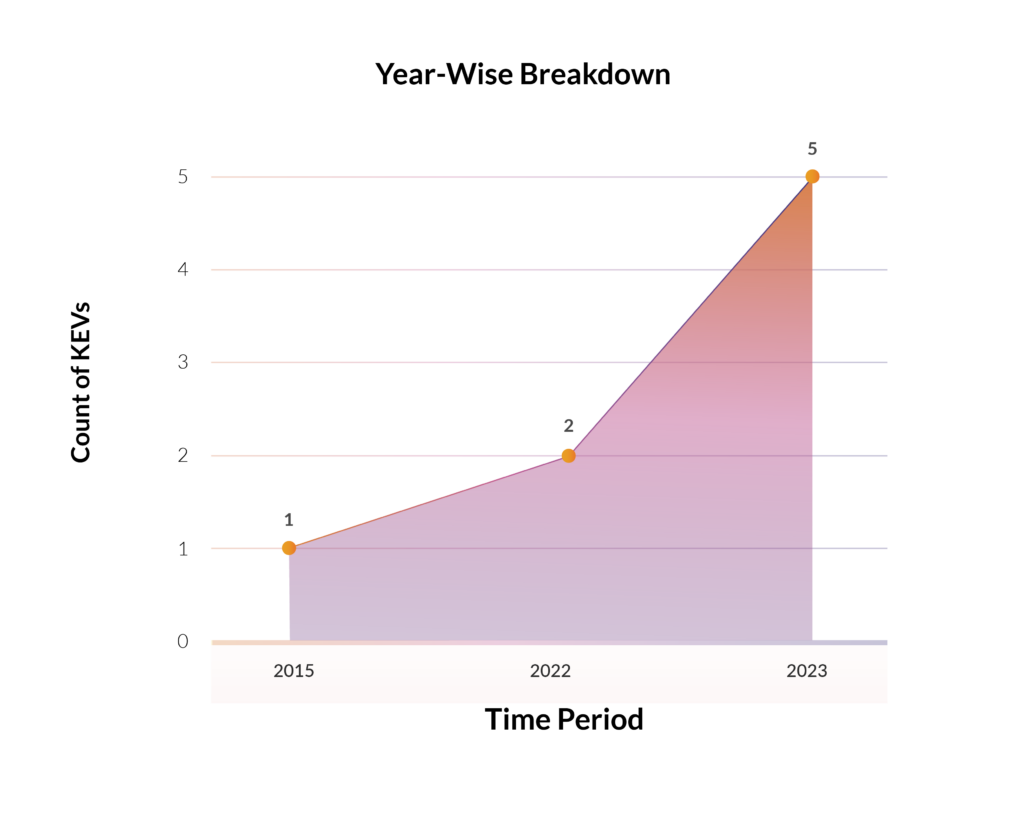
How Far Back Do They Go?
The Intel vulnerability CVE-2015-2291 which dates back to 2015 caught CISA’s attention after the Russian APT groups exploited it in attacks. Other CVE were recently discovered and added to the KEV catalog.
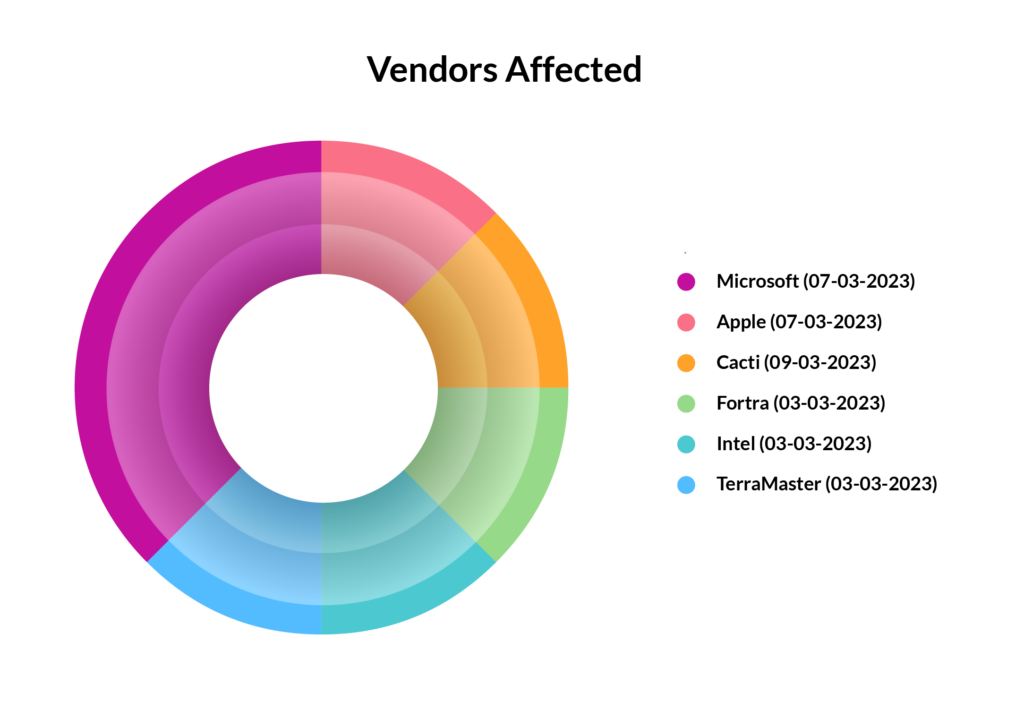
Which Vendors Are Affected?
Microsoft has the most number of vulnerabilities (3) among the CISA CVEs.
Severity Scores
Most vulnerabilities are ranked high on the CVSS scale. CVE-2023-0669, the GoAnywhere MFT vulnerability is present in over 1000 admin consoles that are exposed on the internet.

Software Weaknesses
Each vulnerability is caused due to a flaw in the software design or implementation.
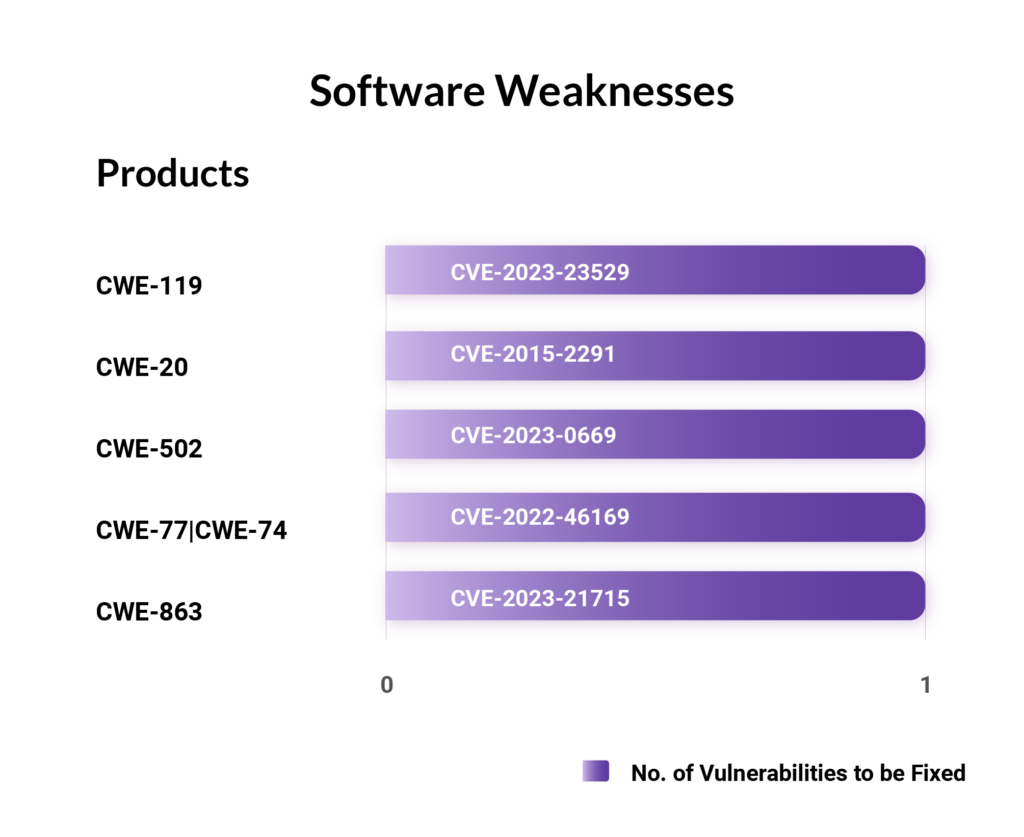
CVE-2023-23376, CVE-2022-24990, and CVE-2023-21823 do not have any CWEs associated with them.
Table: DHS CISA KEVs
We urge organizations to implement patches for these CVEs at the earliest. With Securin’s threat-based approach and vulnerability intelligence, security teams can prioritize the threats, including all KEVs, and minimize their attack surface.
For the latest news regarding vulnerabilities that are exploited and critical threats, read our blog on Weekly Threat Intelligence.









