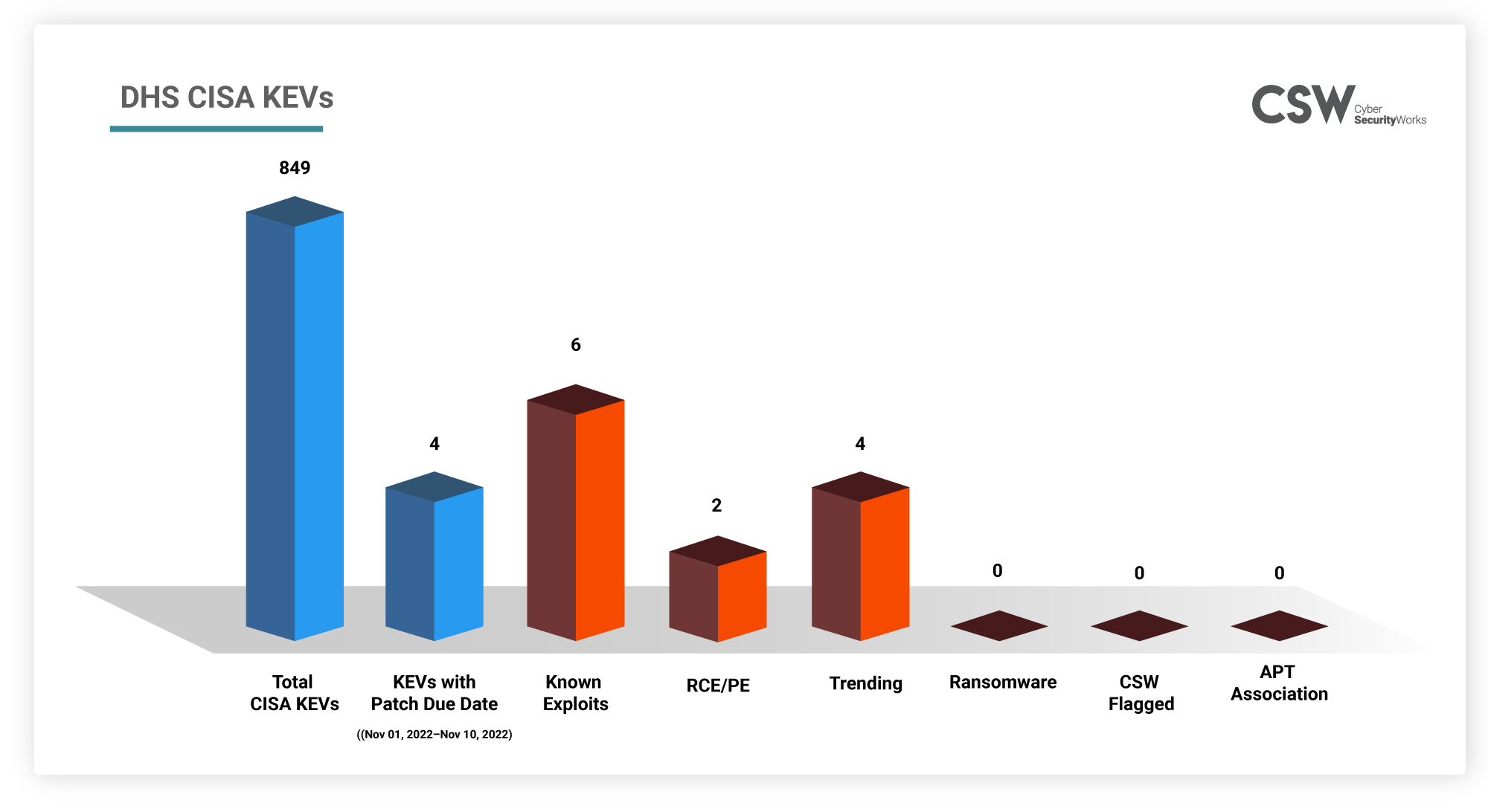
CISA added around 10 vulnerabilities to the KEV between Oct 20, 2022 and Oct 28, 2022. They are currently being exploited by hackers. CISA recommends that Federal organizations patch these vulnerabilities by the end of this year. In this blog, we have covered the CVEs that need to be patched between 01-11-2022 and 10-11-2022. Let’s take a look at them
Why are these CVEs important?
We analyzed these 4 CVEs and found that:
-
All 4 vulnerabilities are trending this month.
-
CVE-2021-3493 is a Linux Kernel vulnerability which can be used for privilege escalation as well as remote code execution once the attackers gain initial access.
-
CVE-2022-40684 is a Fortinet vulnerability which could potentially allow administration access in vulnerable devices.
-
CVE-2022-41352, a Zimbra Collaboration (ZCS) vulnerability, allows an attacker to upload arbitrary files using cpio package to gain incorrect access to any other user accounts.
How Far Back Do They Go?
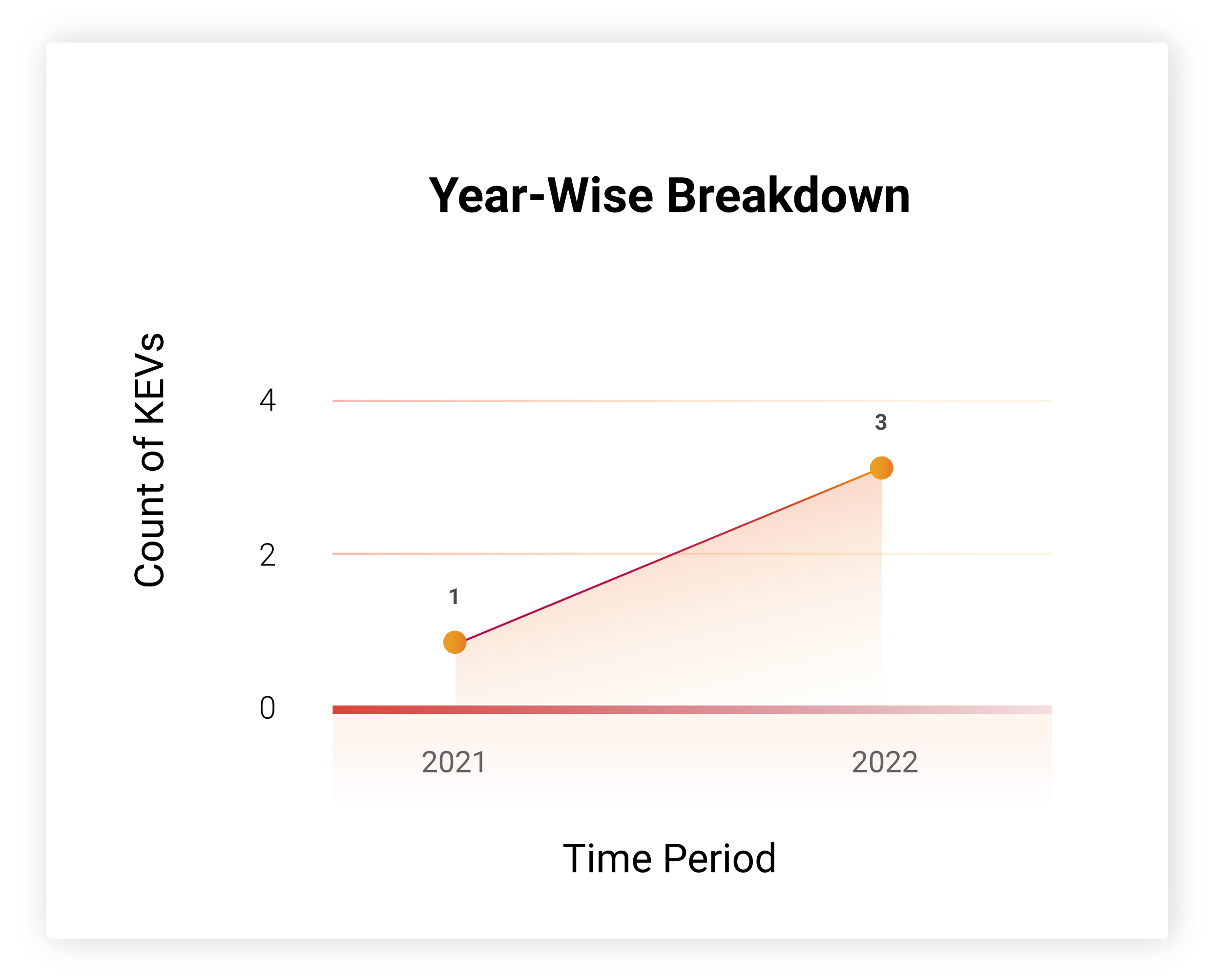
Three of these vulnerabilities are new and have 3 exploits. Except for CVE-2021-3493 which was discovered in 2021 has 3 known exploits. These vulnerabilities are also weaponized.
Which Vendors Are Affected?
The Fortinet vulnerability is present in more than 100,000 FortiGate firewalls that are open to the Internet, although it’s unknown if their management interfaces are also exposed. Apart from it, the rest if the vulnerabilities are also present in multiple popularly used products.
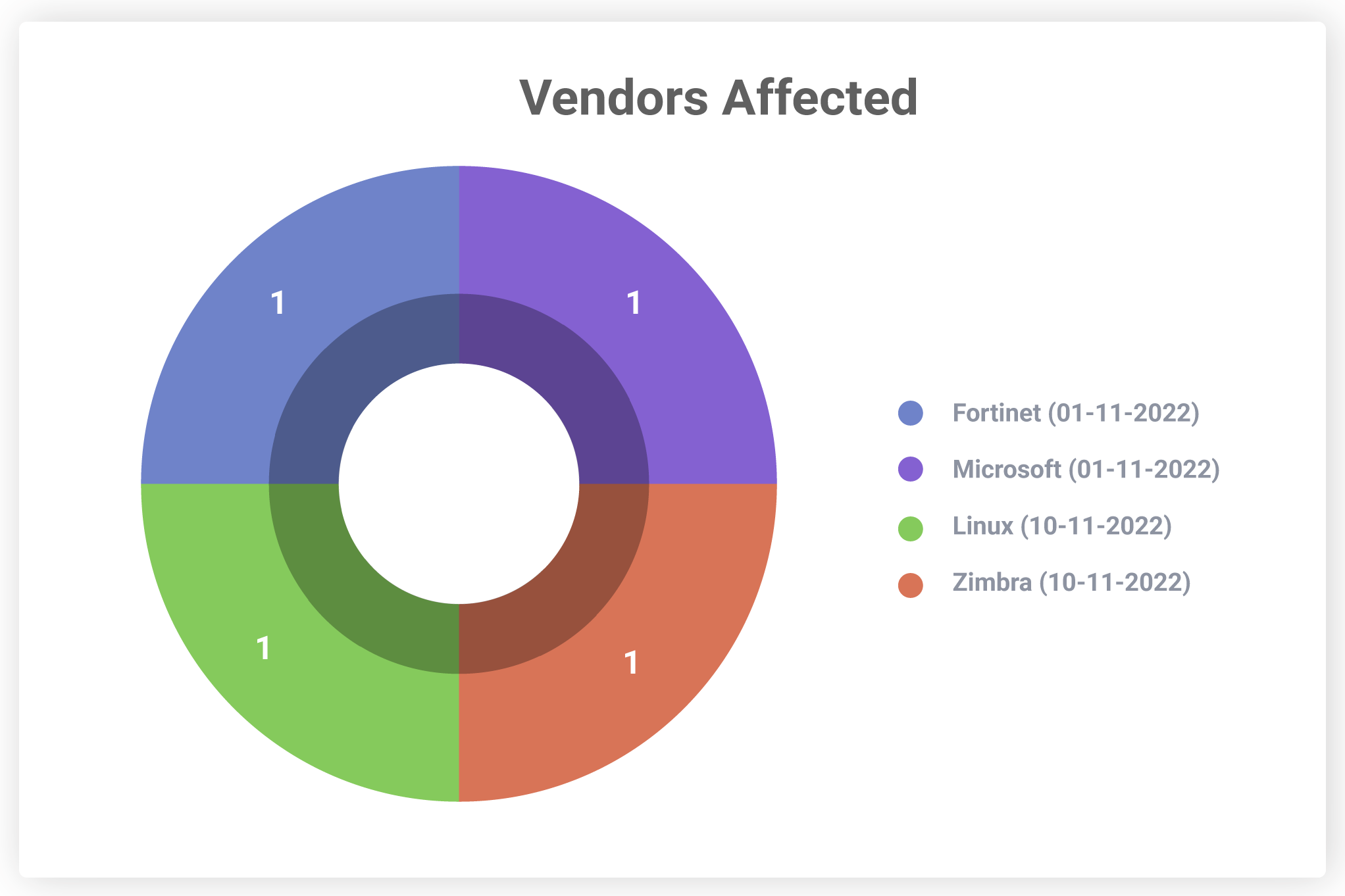
Organizations must keep themselves up-to-date with these vendor advisories and upgrade their products as and when new patches are released.
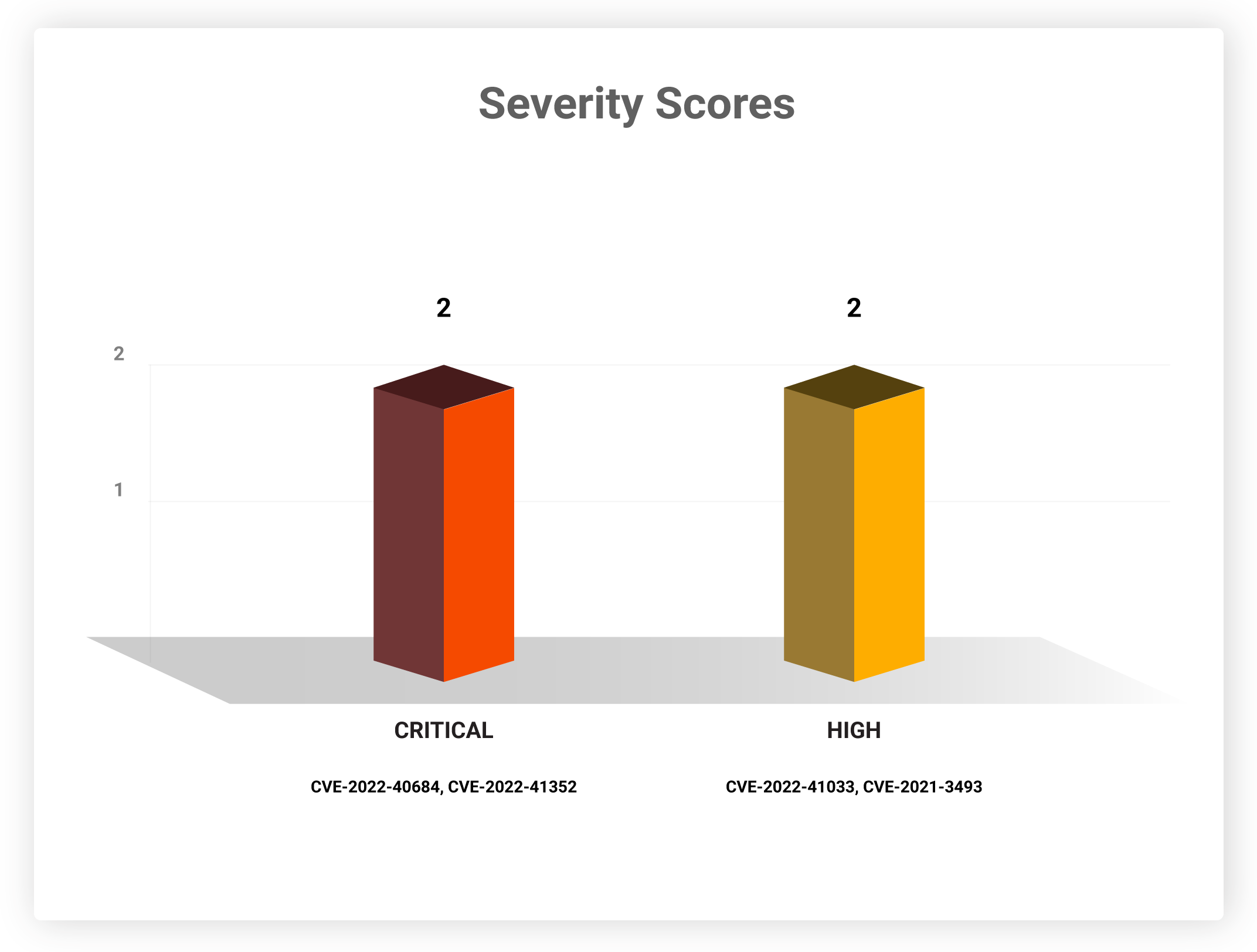
Severity Scores
Patching these vulnerabilities is of high priority, as they rank high and/or critical on the CVSS scoring scale. Exploiting such vulnerabilities will allow attackers to cause maximum damage to their victim networks.
Software Weaknesses
The following CWEs have caused the vulnerabilities that need to be patched this week.
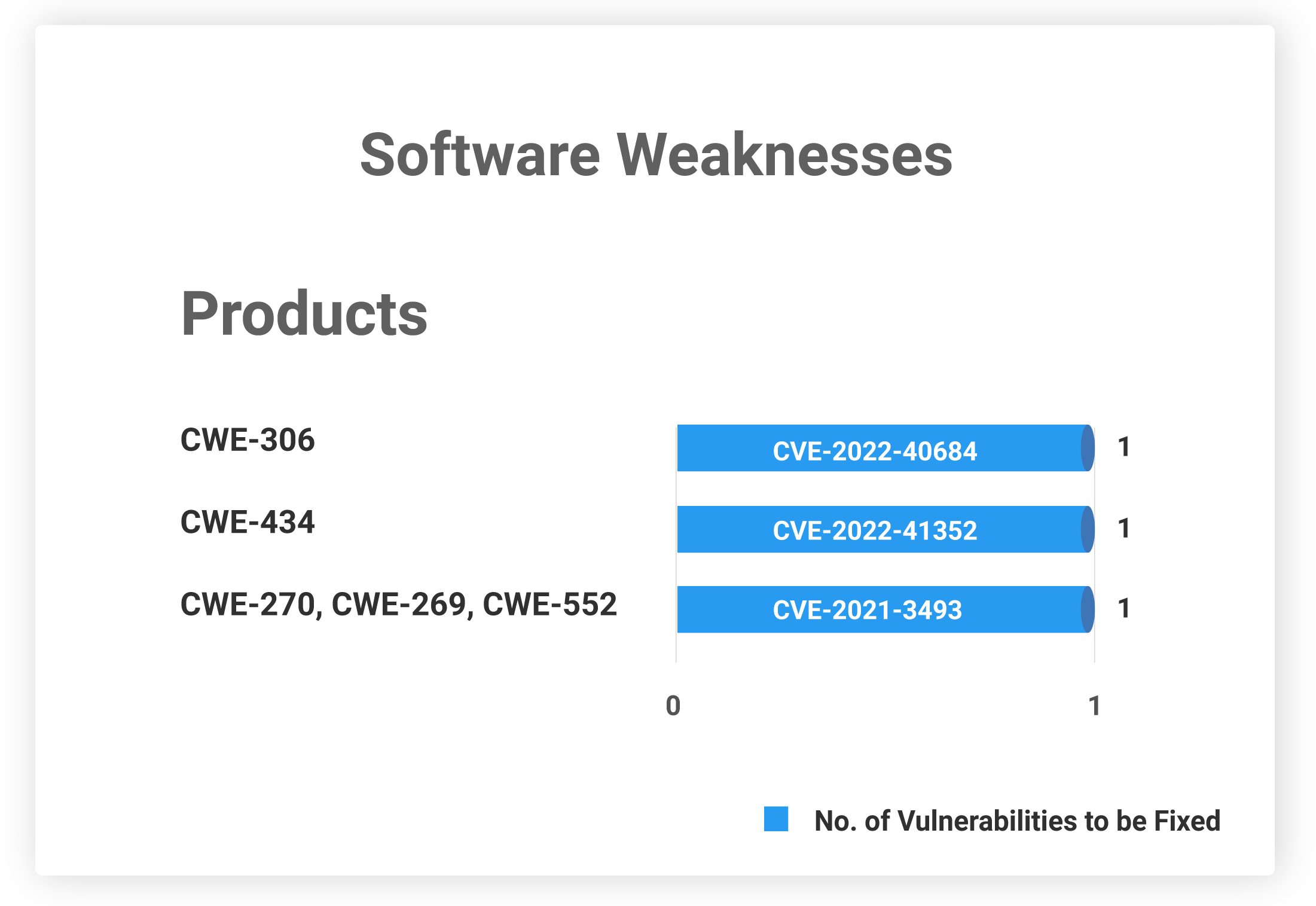
CVE-2021-3493 does not have any CWE associated with it.
Table: DHS CISA KEVs
We urge organizations to implement patches for these CVEs at the earliest. With CSW’s threat-based approach and vulnerability intelligence, security teams can prioritize the threats, including all KEVs, and minimize their attack surface.
For the latest news regarding vulnerabilities that are exploited and critical threats, read our blog on Weekly Threat Intelligence.









