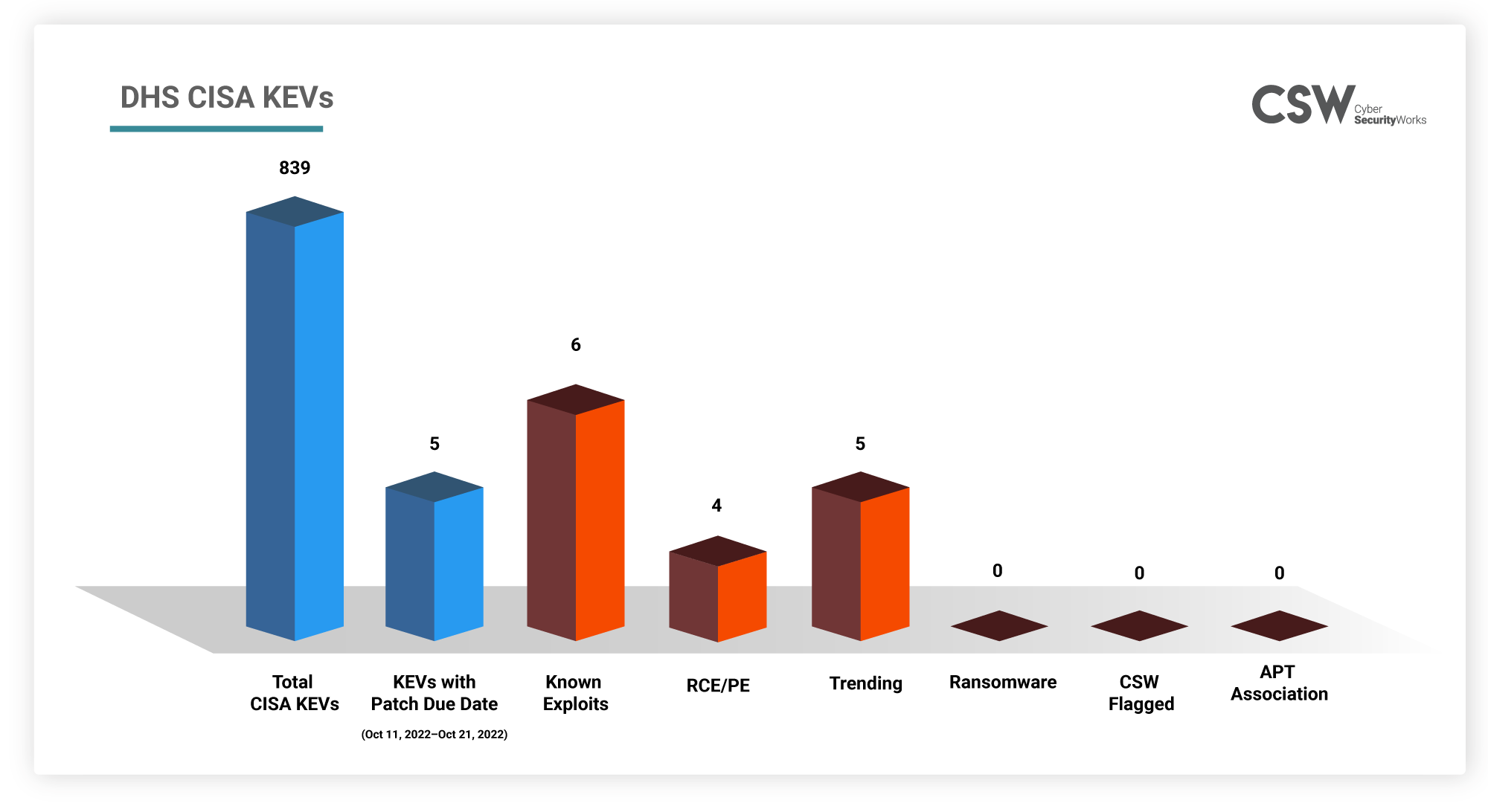
CISA added two more vulnerabilities, CVE-2022-40684 and CVE-2022-41033 to the KEV list on Oct 11, 2022 and Oct 12, 2022, respectively. This brings the total number of vulnerabilities to 839. Based on the level of threat these CVEs pose and the trending exploits, the CISA recommends Federal organizations to patch the CVEs by a given date. We have covered the CVEs that need to be patched between 10-10-2022 and 21-10-2022 in the blog. Let’s take a look at them
Why are these CVEs important?
We analyzed these 5 CVEs and found that:
-
All 5 vulnerabilities are trending this month.
-
CVE-2022-41082 is Microsoft’s zero-day vulnerability. Authenticated attackers who can access PowerShell Remoting on vulnerable Exchange systems will be able to trigger RCE using CVE-2022-41082.
-
CVE-2022-3236 is a Sophos firewall vulnerability which has been targeted in exploits against specific organizations in South Asia.
-
CVE-2022-35405, a ManageEngine vulnerability, has been actively exploited since August 2022.
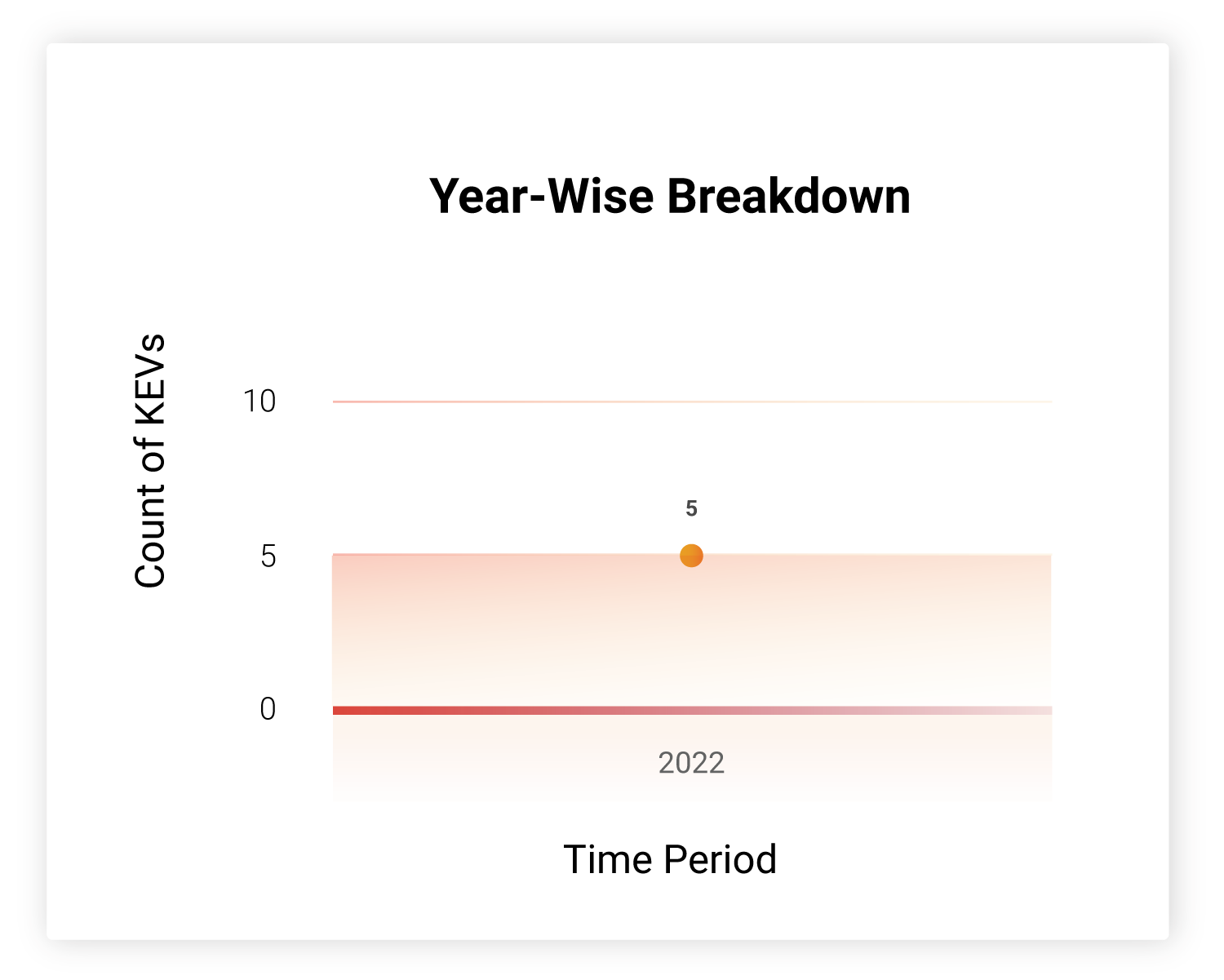
How Far Back Do They Go?
All the vulnerabilities have been discovered in 2022. Except for CVE-2022-3236, all have at least one publicly available exploit. These vulnerabilities are also weaponized.
Which Vendors Are Affected?
Microsoft Exchange servers have been targeted recently by the LockBit ransomware gang. There are two vulnerabilities from this vendor. Similarly, Atlassian vulnerabilities are also highly exploited.
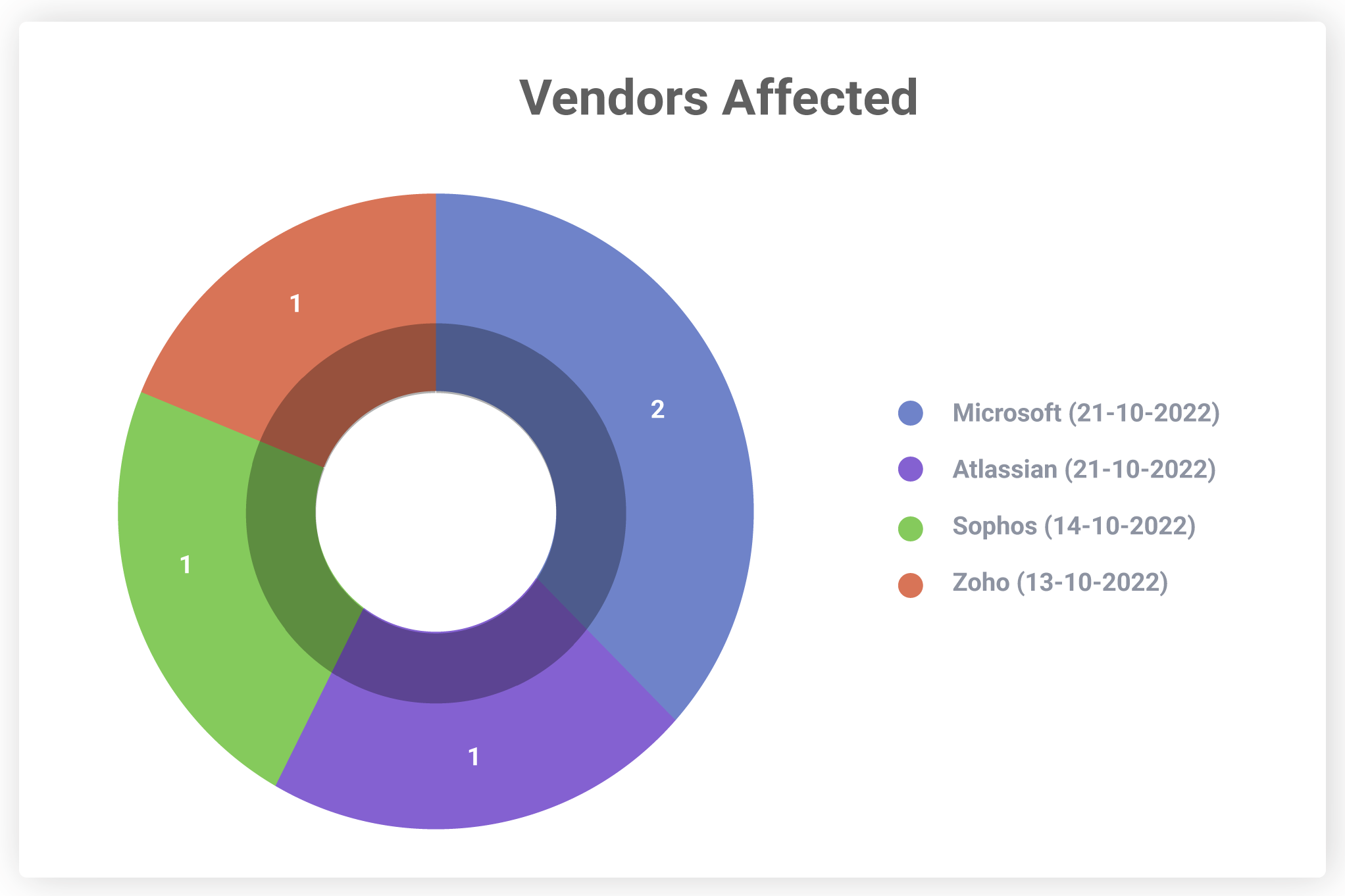
Organizations must keep themselves up-to-date with these vendor advisories and upgrade their products as and when new patches are released.
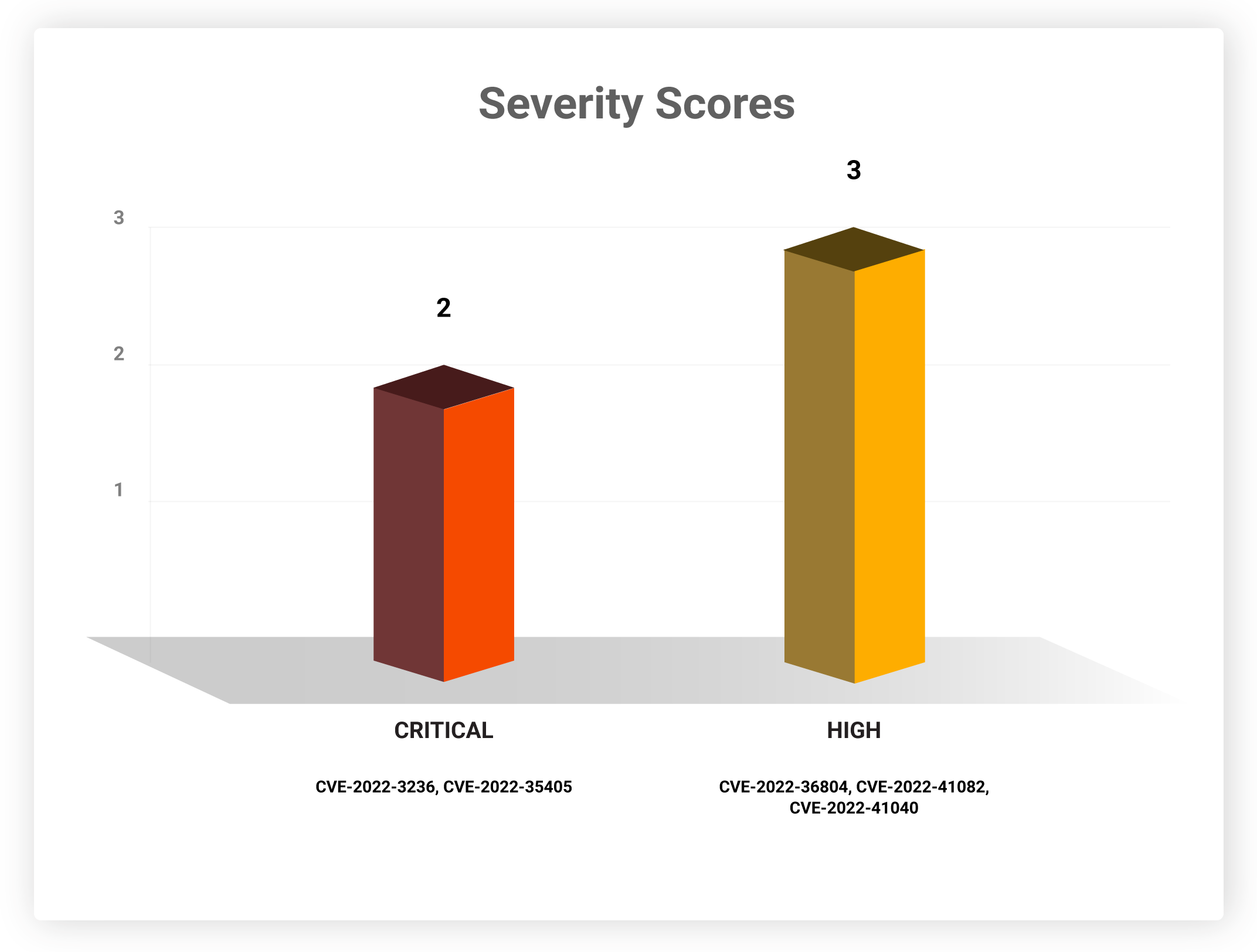
Severity Scores
Patching these vulnerabilities is of high priority, as they rank high and/or critical on the CVSS scoring scale. Exploiting such vulnerabilities will allow attackers to cause maximum damage to their victim networks.
Software Weaknesses
The following CWEs have caused the vulnerabilities that need to be patched this week.
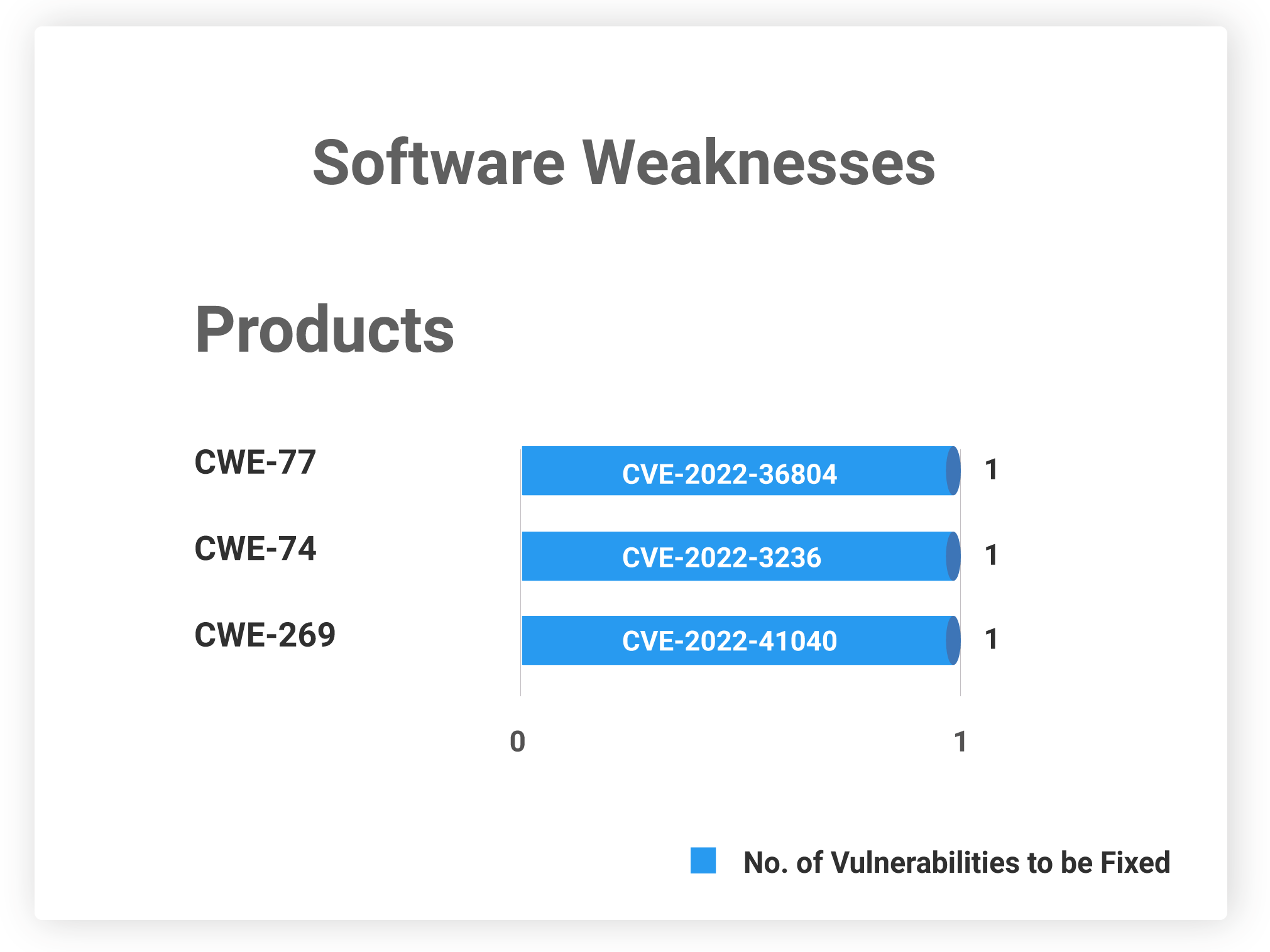
CVE-2022-41082 and CVE-2022-35405 do not have any CWE associated with it.
Table: DHS CISA KEVs
We urge organizations to implement patches for these CVEs at the earliest. With CSW’s threat-based approach and vulnerability intelligence, security teams can prioritize the threats, including all KEVs, and minimize their attack surface.
For the latest news regarding vulnerabilities that are exploited and critical threats, read our blog on Weekly Threat Intelligence.









