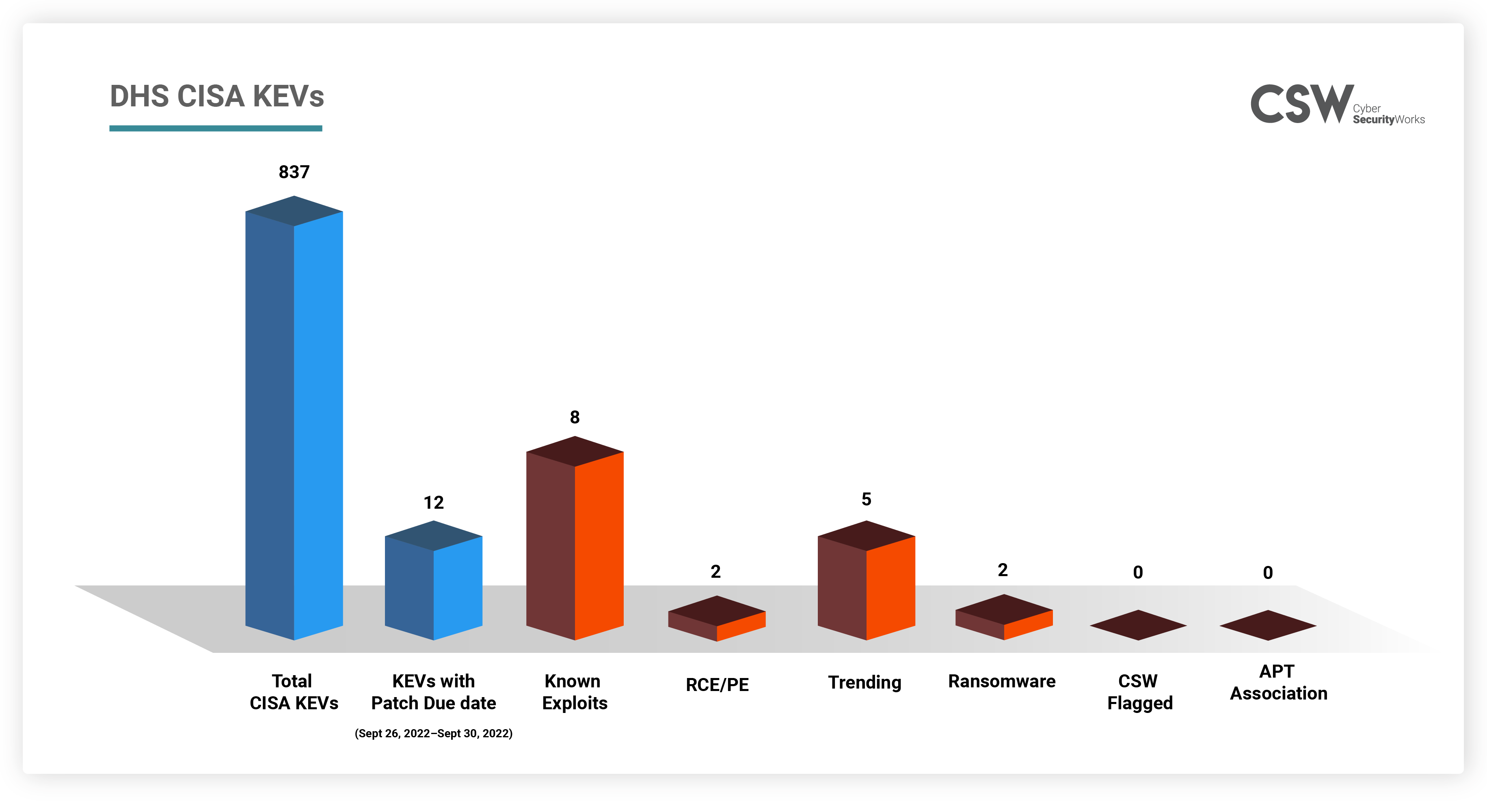
The US Cybersecurity and Infrastructure Security Agency (CISA) raises the alarm about known exploited vulnerabilities by adding new CVEs to the growing list of KEV catalog. It added 3 CVEs to the KEV on September 20, 2022 bring the total to 837. In this blog, we bring you all the DHS CISA KEVs that need to be prioritized for patching this week (September 26 to September 30, 2022).
Why are these vulnerabilities important?
CISA’s KEVs is a collection of vulnerabilities that have been exploited by threat actors time and again. If left unpatched, these become low hanging fruits that attackers can easily misuse.
A total of 12 known exploited vulnerabilities from the DHS CISA catalog should be fixed by federal agencies this week before September 26 to September 30, 2022. We urge all organizations to address these to safeguard their networks from attacks.
We further analyzed these 12 KEVs and found that:
-
The vulnerabilities affect 59 products which are actively used in organizations. All these CVEs were added on September 9th and required to be patched by the end of the month indicating the danger these vulnerabilities bring.
-
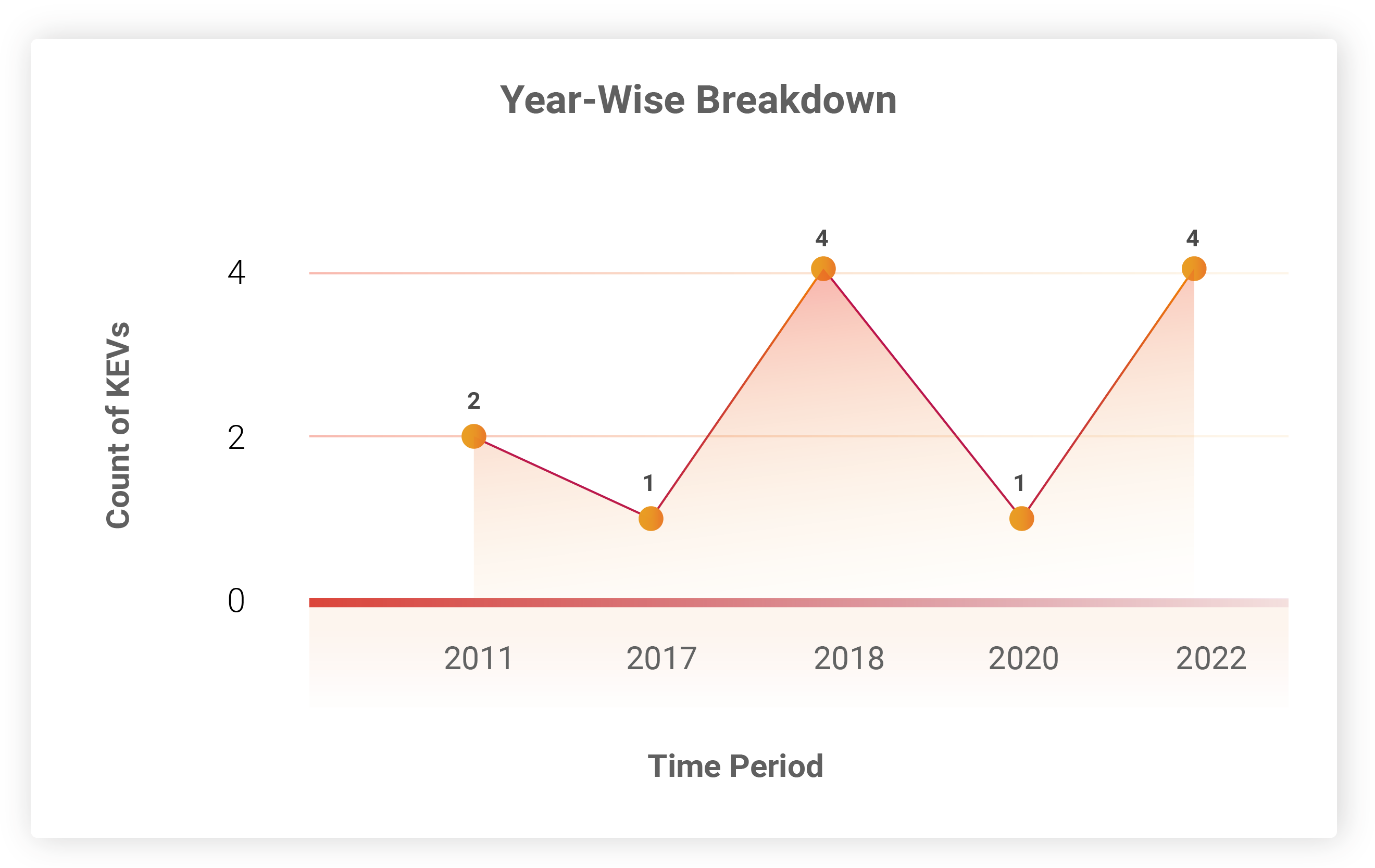
Among the 5 trending vulnerabilities, 4 are old CVEs dating back to 2011, 2017, and 2018. These have been exploited multiple times by threat actors and will continue to be easy targets unless patched.
-
CVE-2018-13374 is a vulnerability famously exploited by the Conti group. Although this APT group is no longer operational, multiple threat actors imitate Conti’s exploits. If this CVE is present in your system, it will pose a grave threat.
How Far Back Do They Go?
Except for 4 vulnerabilities, all CVEs have been around for a while, 2 of them since 2011. One of the 2011 CVEs is a PE vulnerability in Andriod OS.
Which Vendors Are Affected?
D-LINK is the worst affected with 4 vulnerabilities. Recently, APT groups such as especially in China have targeted SOHO routers to break into organization networks The rest of the vulnerabilities are also in popular vendors which are used widely at organizations and homes.
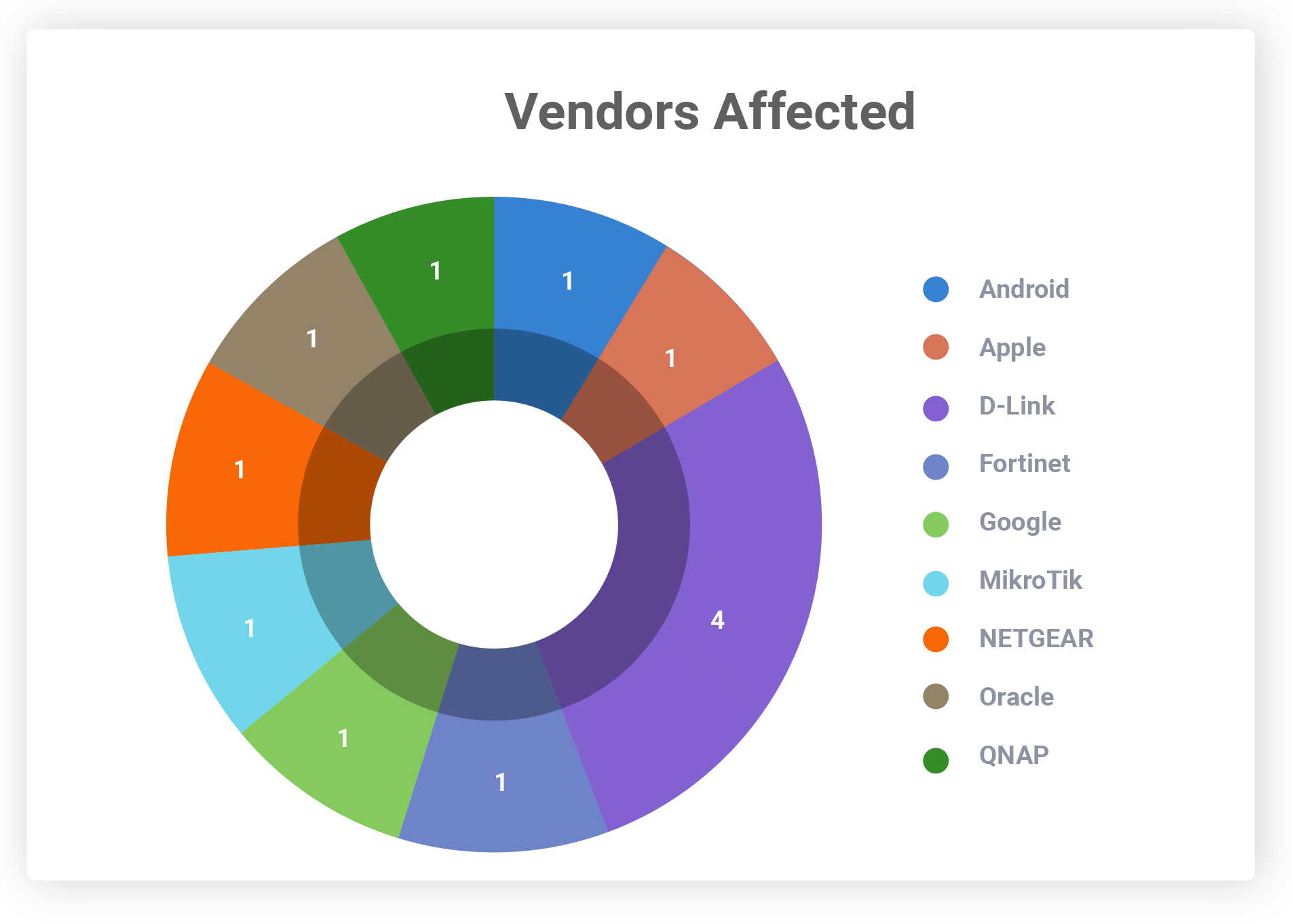
Organizations must keep themselves up to date with these vendor advisories and upgrade their products as and when new patches are released.
Severity Scores
Patching these vulnerabilities is of high priority, as they rank high and critical on the CVSS scoring scale. Exploiting such vulnerabilities will allow attackers to cause maximum damage to their victim networks.
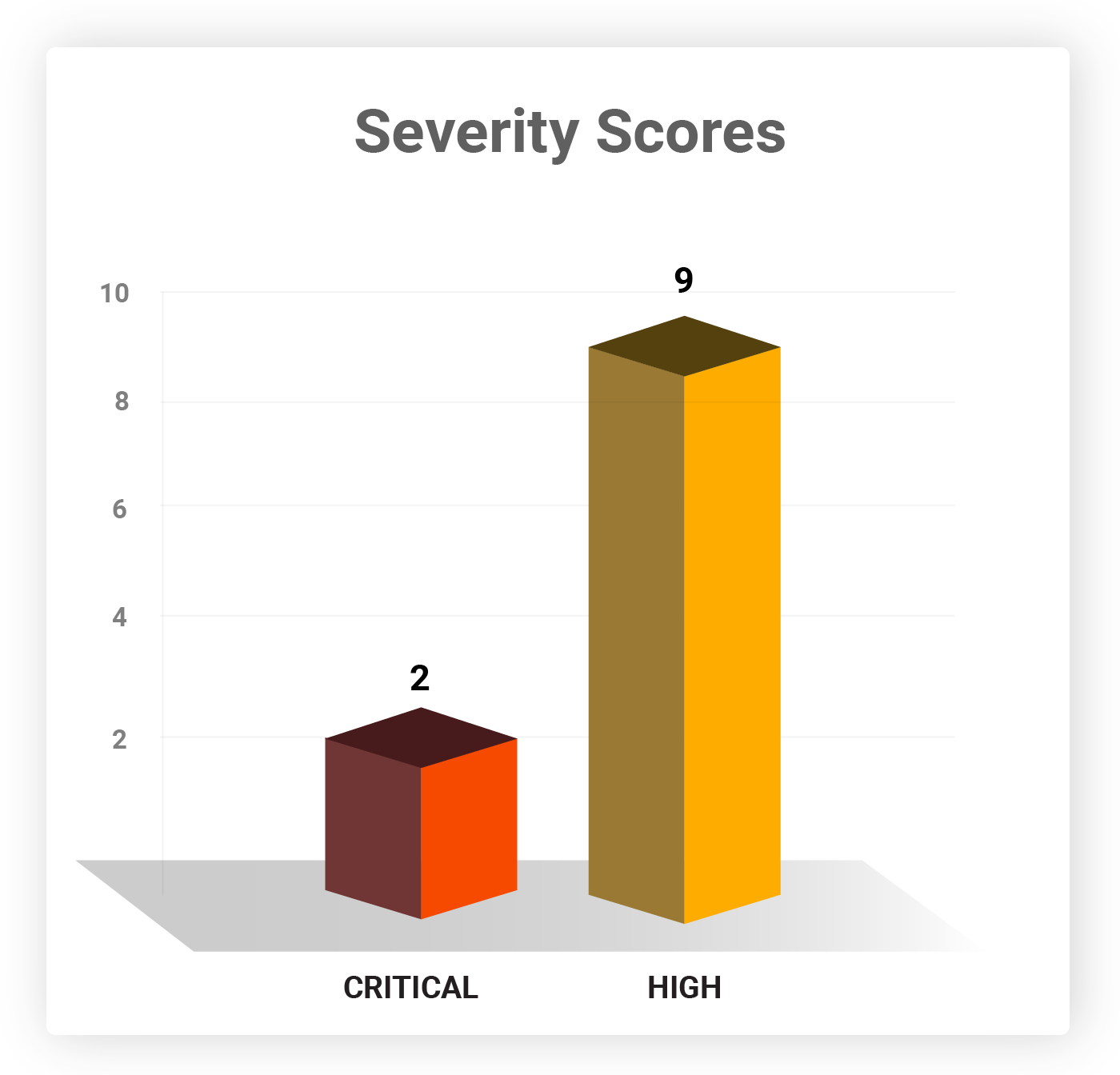
CVE-2022-3075, the Chromium vulnerability has not been assigned any CVSS score.
Software Weaknesses
The following CWEs have caused the vulnerabilities that need to be patched this week. These are the weaknesses developers should be aware of and work to overcome while making their products.
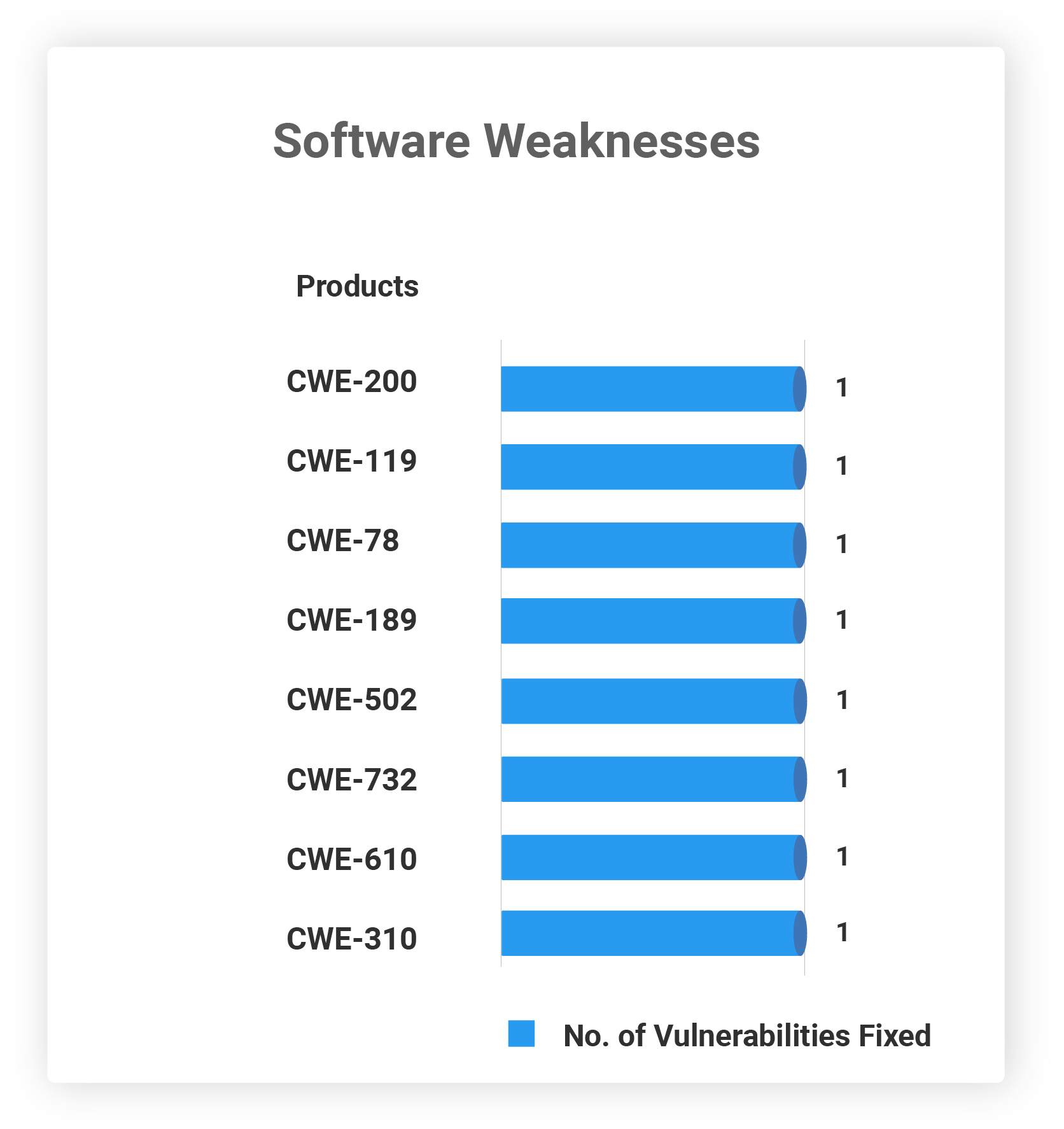
Table: DHS CISA KEVs
We urge organizations to implement patches for these CVEs at the earliest. With Securin’s threat-based approach and vulnerability intelligence, security teams can prioritize the threats, including all KEVs, and minimize their attack surface.
For the latest news regarding vulnerabilities that are exploited and critical threats, read our blog on Weekly Threat Intelligence.