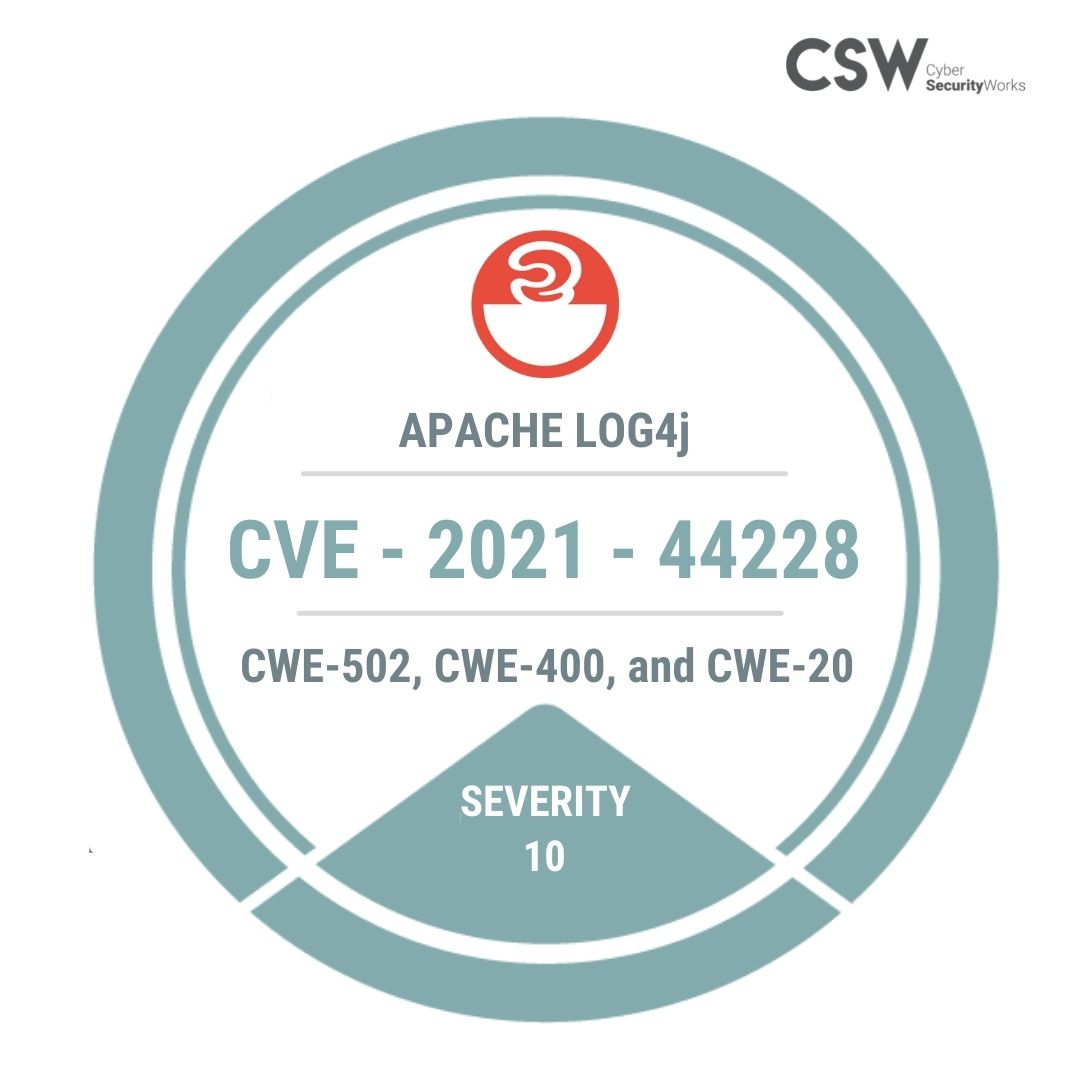
On December 9, 2021, a new critical zero-day vulnerability (CVE-2021-44228) was discovered in Apache Log4J, a Java-based logging tool that affects any organization that uses Apache Log4j framework including Apache Struts2, Apache Solr, Apache Druid, Apache Flink, and others.
We analyzed this critical vulnerability and highlighted why patching this vulnerability is absolutely vital.
Seven Reasons to Patch this Vulnerability
#1 Widely Used Library – Since many vendors use the Log4J library in their products, CVE-2021-44228, a code-execution vulnerability in the Apache Log4J open-source logging utility may have a supply-chain impact.
#2 Threat Actor Chatter – Hacker and threat group channels are abuzz with chatter regarding this vulnerability as everyone scrambles to exploit the vulnerability. Our security analysts were alarmed by the chatter and think CVE-2021-44228 has the potential to be similar to the SolarWinds saga. All organizations should take action now to avoid such a scenario.
#3 Critical RCE Exploit – CVE-2021-44228 gets a rare CVSS v3 score of 10. RCE exploits are the most dangerous exploitation type and in this case, it enables a complete take over of the server and facilitates override of the validation processes that are required to process the data safely and correctly. This vulnerability affects all versions from 2.0-beta9 to 2.14.1)
#4 CWE Categorization – This RCE vulnerability has been categorized under CWE-502, CWE-400, and CWE-20 that are listed under 2021 Top 30 Most Dangerous Software Weaknesses, making patching extremely crucial.
#5 Threat Associations – Researchers identified that log4J vulnerabilities are being exploited by ransomware families such as Khonsari, Conti, and TellYouThePass, APT groups (Nemesis Kitten, Hafnium, Phosphorus), Dridex banking malware, and Mirai botnets.
#6 CERT Alerts – US-CERT and New Zealand issued an alert to users to apply the recommended mitigations “immediately” in order to address the critical vulnerabilities.
#7 Patches are available – Apache released an official patch for this vulnerability – 2.15.0.rc1, which was quickly bypassed. Subsequently, patch 2.15.0.rc2 was released to protect users from this vulnerability. We urge all organizations to patch the vulnerability on priority to avoid a potential supply-chain attack.
Securin researchers have developed a script to help organizations detect exploitation of the Apache Log4j vulnerability. Organizations are encouraged to use this script to check for attacks against their environment.
We also urge users to upgrade to the latest version of Apache Log4j and apply the necessary mitigations as quickly as possible.
Check out our detailed analysis on Apache Log4J vulnerability here









