Securin Zero-Days
CVE-2026-6057 - Unauthenticated Path Traversal in Falkor DB Browser Leads to Remote Code Execution
Description
FalkorDB Browser version 1.9.3 contains a critical security vulnerability in its file upload API endpoint (app/api/upload/route.ts). The endpoint fails to enforce any authentication, allowing unauthenticated remote attackers to reach the file write logic.
Furthermore, the uploaded filename is passed unsanitized to Node.js's path.join(), which resolves traversal sequences like ../. This allows an attacker to write arbitrary files to the server's filesystem, including the Next.js source tree. In development environments using Turbopack, this leads to immediate Remote Code Execution (RCE) via hot-reloading when an attacker overwrites an existing API route with a webshell.
Proof of Concept
The following steps reproduce the vulnerability:
Step 1: Confirm unauthenticated access by sending a probe POST request to /api/upload without credentials. The server will reveal the absolute path in its error response.
Step 2: Upload a webshell payload using path traversal to overwrite an existing route, such as ../../app/api/status/route.ts.
Step 3: Wait approximately 6 seconds for Turbopack to hot-reload the modified route.
Step 4: Execute OS commands by sending a GET request to the newly overwritten endpoint (e.g., /api/status?cmd=id).
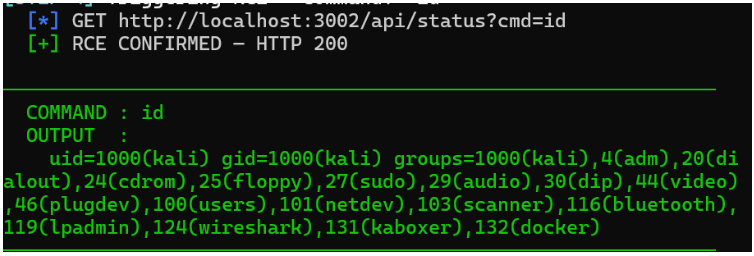
Figure 1: “Id” output to confirm the RCE through uploaded web shell
Vulnerable Code
The following snippet from app/api/upload/route.ts demonstrates the missing authentication and unsafe path construction:
typescript
export async function POST(request: NextRequest) {
// Missing getClient(request) call found in other routes
const formData = await request.formData();
const file = formData.get("file") as File;
// Unsafe: resolves traversal sequences from file.name
const filename = file.name.replaceAll(" ", "_");
const filePath = path.join(process.cwd(), `public/assets/${filename}`);
await pump(file.stream(), fs.createWriteStream(filePath));
return NextResponse.json({ path: filePath, status: 200 });
}
Trigger Conditions
- FalkorDB Browser version ≤ 1.9.3.
- Application is accessible over the network.
- For immediate RCE, the server must be running in development mode (npm run dev) with Turbopack.
MITRE ATT&CK TTP Mapping
ATT&CK Stage | Technique ID | Technique Name |
Initial Access | T1190 | Exploit Public-Facing Application |
Execution | T1203 | Command and Scripting Interpreter |
Persistence | T1499 | Server Software Component: Web Shell |
Impact
Successful exploitation of this vulnerability results in:
- Remote Code Execution (RCE): Attackers can execute arbitrary OS commands as the Node.js process user.
- Full Host Escape: Due to docker group membership, an attacker can achieve root access on the underlying host.
- Data Exfiltration: Sensitive environment secrets like NEXTAUTH_SECRET and ENCRYPTION_KEY can be stolen.
- Credential Theft: All stored PAT passwords in the database can be decrypted.
Remediation
Two primary fixes are required to fully secure the application:
- Enforce Authentication: Add the getClient(request) call at the beginning of the POST handler to block unauthenticated access.
- Secure File Handling: Generate server-side UUIDs for filenames instead of using file.name, and use path.resolve() with prefix validation to prevent traversal.
Disclosure Timeline