Securin Zero-Days
CVE-2026-5525 - Stack-Based Buffer Overflow in Notepad++ File Drop Handler leads to DoS
Description
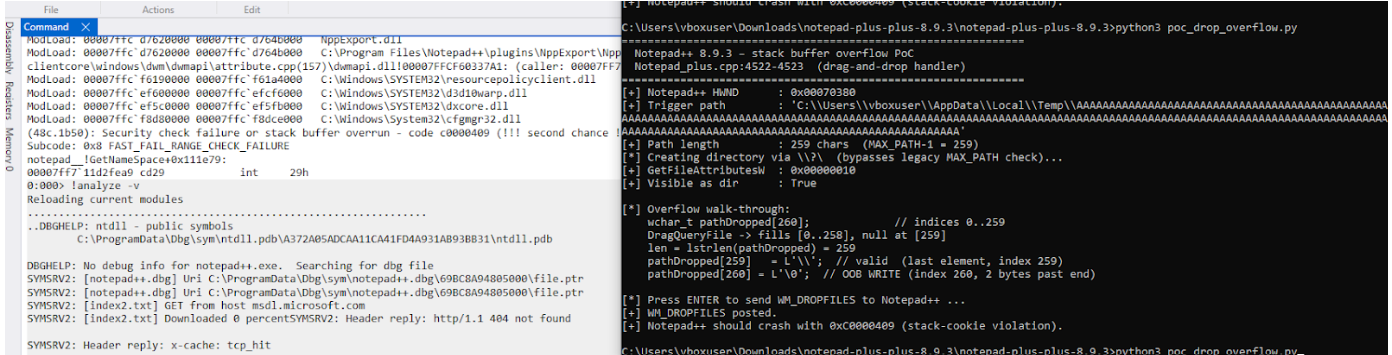
A stack-based buffer overflow vulnerability exists in Notepad++ version 8.9.3 within the file drop handler component (PowerEditor/src/Notepad_plus.cpp, lines 4514-4526). The vulnerability is triggered when a user drags and drops a directory path of exactly 259 characters (MAX_PATH - 1) without a trailing backslash onto the Notepad++ application window.
When processing the dropped path, the application attempts to append a backslash and a null terminator to the buffer without performing adequate bounds checking. Since the buffer is declared as wchar_t pathDropped[MAX_PATH] (260 elements, indices 0-259), and the path already occupies 259 characters, the null terminator write at index 260 overflows the stack-allocated buffer, resulting in a STATUS_STACK_BUFFER_OVERRUN (0xC0000409) error.
Proof of Concept
The following steps reproduce the vulnerability:
Step 1: Enable Win32 long path support on the target Windows system (requires registry modification or Group Policy change, as this is not enabled by default).
Step 2: Create a nested directory structure where the full path is exactly 259 characters long (e.g., C:\aaa...aaa\bbb...bbb totaling 259 characters).
Step 3: Launch Notepad++ version 8.9.3.
Step 4: Open Windows File Explorer and navigate to the parent of the crafted directory.
Step 5: Drag and drop the 259-character directory onto the Notepad++ window.
Vulnerable Code
The following code in Notepad_plus.cpp demonstrates the vulnerable pattern:
typescript
wchar_t pathDropped[MAX_PATH]; // 260 elements, indices 0-259
DragQueryFile(hdrop, i, pathDropped, MAX_PATH);
// ...
if (::PathIsDirectory(pathDropped))
{
size_t len = lstrlen(pathDropped);
if (pathDropped[len - 1] != '\\')
{
pathDropped[len] = '\\'; // Valid write at index 259
pathDropped[len + 1] = '\0'; // OVERFLOW at index 260!
}
}Trigger Conditions
- Notepad++ version 8.9.3 running on Windows (x86 or x64)
- A directory path exactly 259 characters long
- The directory path does not end with a trailing backslash
- The user drags the directory onto the Notepad++ application window
- Windows long paths must be enabled (a non-default configuration)
MITRE ATT&CK TTP Mapping
The vulnerability maps to MITRE ATT&CK techniques involving User Execution, Exploitation for Client Execution, and Endpoint Denial of Service, as it requires user interaction to trigger a client-side buffer overflow that results in application crash (DoS).
ATT&CK Stage | Technique ID | Technique Name |
Initial Access | T1204 | User Execution |
Execution | T1203 | Exploitation for Client Execution |
Impact | T1499 | Endpoint Denial of Service |
Impact
Successful exploitation of this vulnerability results in the following:
- Denial of Service (DoS): Reliable application crash triggered by the stack buffer overrun, causing immediate termination of Notepad++ and potential loss of unsaved work.
Remediations
The vulnerability was remediated by adding proper bounds validation before appending characters to the buffer. The fix ensures the buffer length is checked against MAX_PATH before the write operation.
- Update Notepad++ to the latest version which includes the fix.
Timeline
References
- GitHub Issue: https://github.com/notepad-plus-plus/notepad-plus-plus/issues/17921
- GitHub Pull Request: https://github.com/notepad-plus-plus/notepad-plus-plus/pull/17930
- Fix Commit: https://github.com/notepad-plus-plus/notepad-plus-plus/commit/bfe7514d68bc559534c046c4ef2d1865267aa2b0
- CWE-121: Stack-based Buffer Overflow — https://cwe.mitre.org/data/definitions/121.html