Securin Zero-Days
CVE-2024-47095 - Reflected Cross-Site Scripting in Follett School Solutions Destiny Library Manager
Description
Versions of Follett School Solutions Destiny Library manager before v22.0.1 AU1 are affected by a reflected cross-site scripting vulnerability. Due to this vulnerability, if the application is accessed through an attacker-controlled link, the attacker can display arbitrary (potentially hostile and dangerous) content in the context of the otherwise legitimate website.
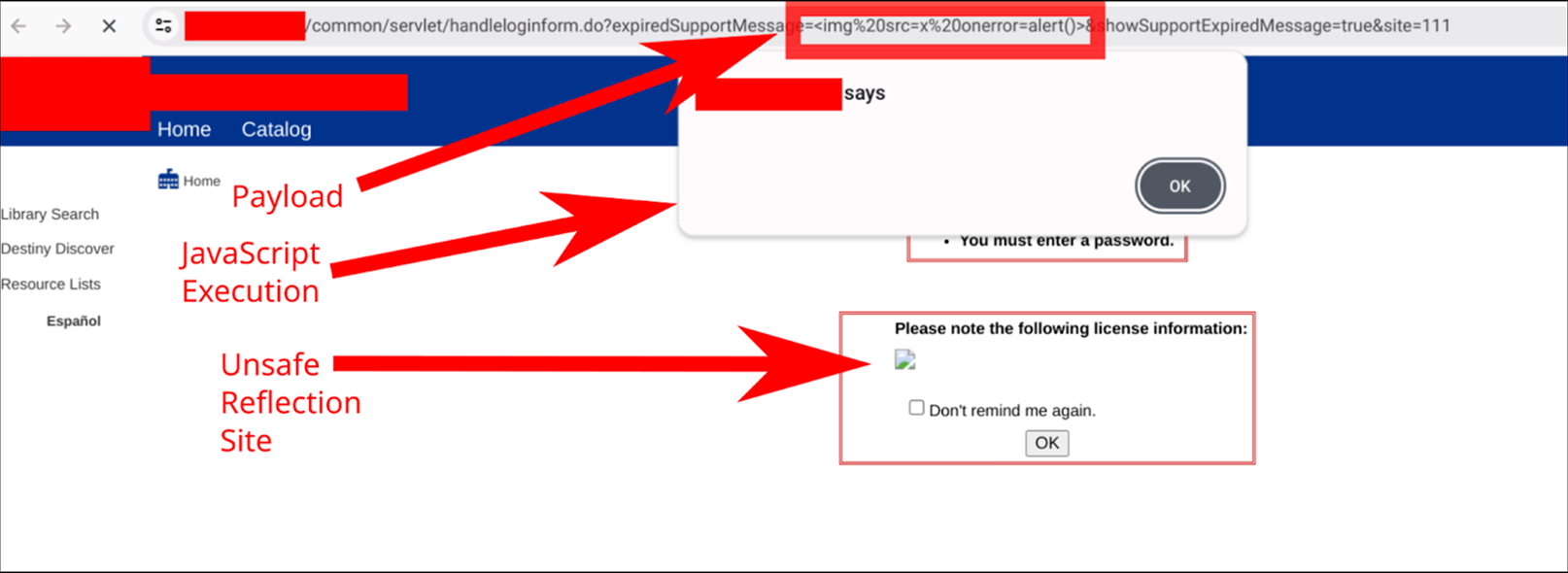
Proof of Concept (POC):
We tested the following vulnerability on a deployment of Follett School Solutions Destiny Library Manager version 21.2.0 RC2.
- Navigate the application normally to identify the site ID of any valid site within the target deployment. For many deployments the main landing page of the application will consist of links to particular site IDs. As these values are expected to be small integers it is also possible to identify a valid site ID via brute force if necessary.
- Construct a URL of the form here where “affected.domain” is replaced with the domain of the deployment and “1234” is replaced with a valid site ID for that deployment.
Impact
If a user accesses the vulnerable application through an attacker controlled link, the attacker can arbitrarily modify the contents of the site as displayed to the victim user. This can be abused to achieve a form of vandalism, to spread misinformation, and to steal any passwords users may submit to the site.
Remediations
Encode special characters prior to reflecting them in an HTML or JavaScript context via server-side templating.
Timeline
Encode special characters prior to reflecting them in an HTML or JavaScript context via server-side templating.