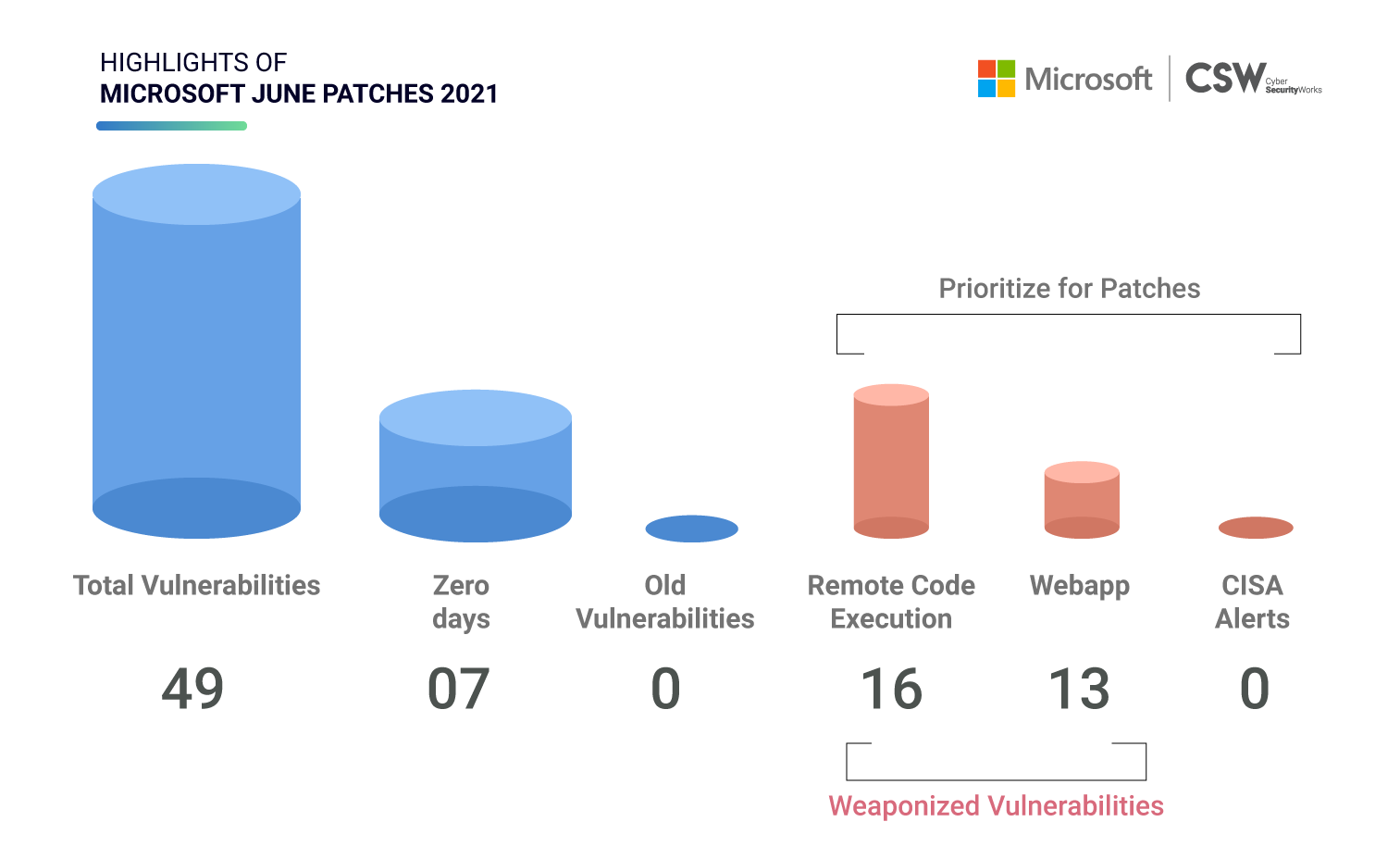
Microsoft patched 49 unique security vulnerabilities this June. We analyzed all 49 weaknesses and spotlighted the most important vulnerabilities that ought to be patched on priority.
 Microsoft Patches: Overview
Microsoft Patches: Overview
This June, Microsoft patched 49 vulnerabilities discovered earlier in 2021, including six publicly disclosed bugs.
Of these 49, Microsoft has fixed key vulnerabilities, including the following:
-
16 CVEs classified as RCE bugs
-
13 CVEs with privilege escalation capabilities
-
5 CVEs linked to denial of service (DoS)
-
7 CVEs with information disclosure issues
-
4 CVEs associated with a security feature bypass
-
3 CVEs with spoofing flaws
Zero-Day Vulnerabilities
Microsoft had released patches for seven zero-day vulnerabilities (CVE-2021-31955, CVE-2021-31956, CVE-2021-33739, CVE-2021-33742, CVE-2021-31199, CVE-2021-31201, and CVE-2021-31968). Currently, six of these CVEs have publicly known exploits under active attack and must be prioritized for patching.
Additionally, a new threat group called PuzzleMaker leveraged two zero-day exploits (CVE-2021-31955 and CVE-2021-31956) with a remote code execution weakness to target high-profile systems. The threat group utilized these two CVEs to execute malware modules with system privileges on compromised Windows 10 systems. To put a stop to this, Microsoft released patches for these two exploits.
However, organizations need to be wary of these two CVEs and ensure that they are patched immediately. Both vulnerabilities are of a high severity with a CWE of 200 (Exposure of Sensitive Information to an Unauthorized Actor) and 269 (Improper Privilege Management) classified under the Top 25 Most Dangerous Software Weaknesses.
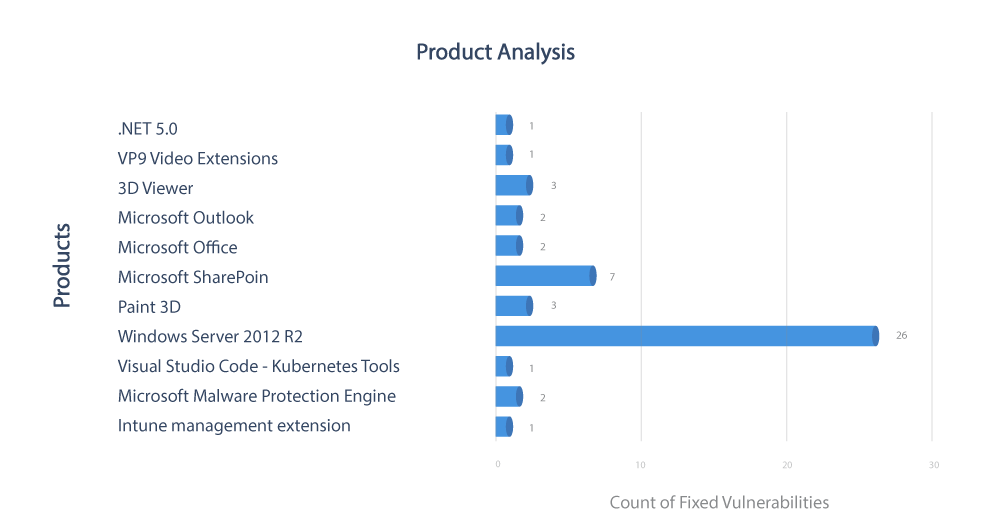
Product Analysis
In this Patch Watch, we focus on patches that were issued for 11 products. The Windows server accounted for 26 vulnerabilities, of which 12 have been categorized with privilege escalation capabilities, and two have been marked for remote code execution.
Severity
Notably, five of these 26 vulnerabilities have been marked critical and under remote code execution flaws.
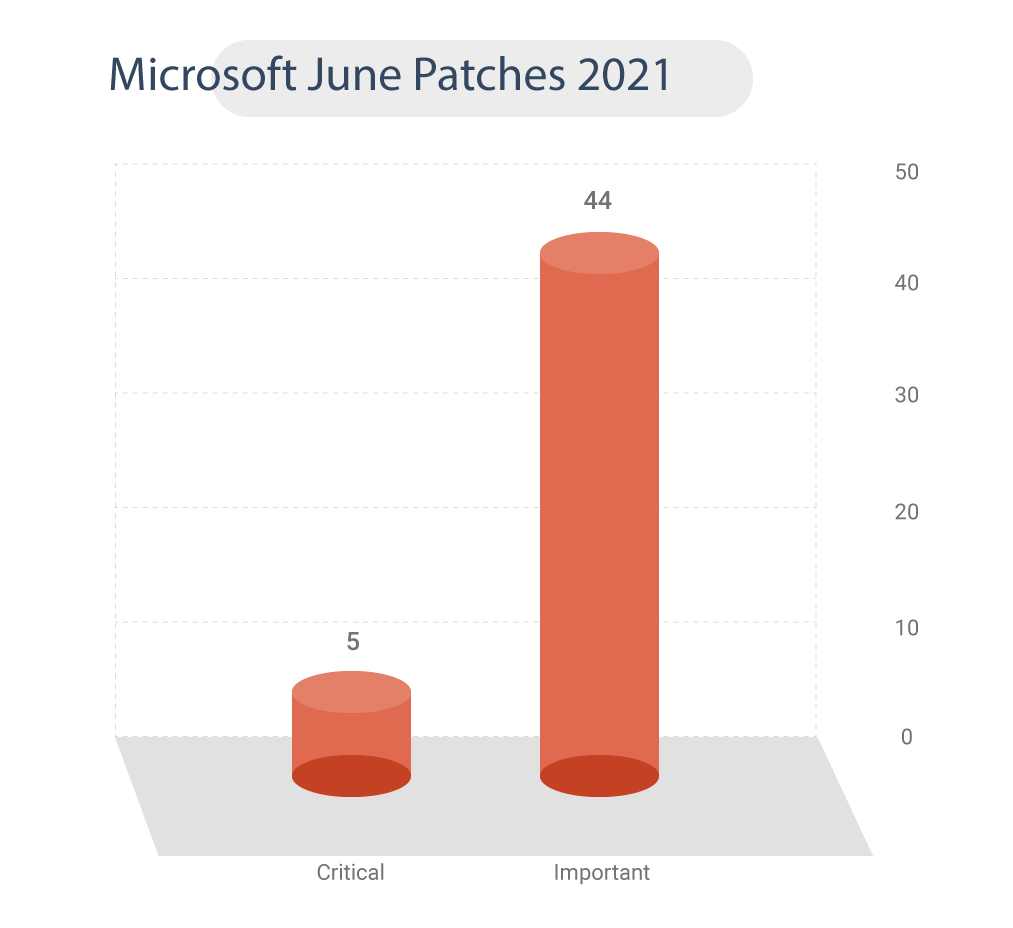
Table: June Microsoft Security Patches 2021
Despite releasing a set of fixes in June, Microsoft still has several vulnerabilities that need to be addressed. These CVEs need immediate patching based on their risk potential. Therefore, we urge all Microsoft users to update the latest version of the software to reduce their attack surface and risk.