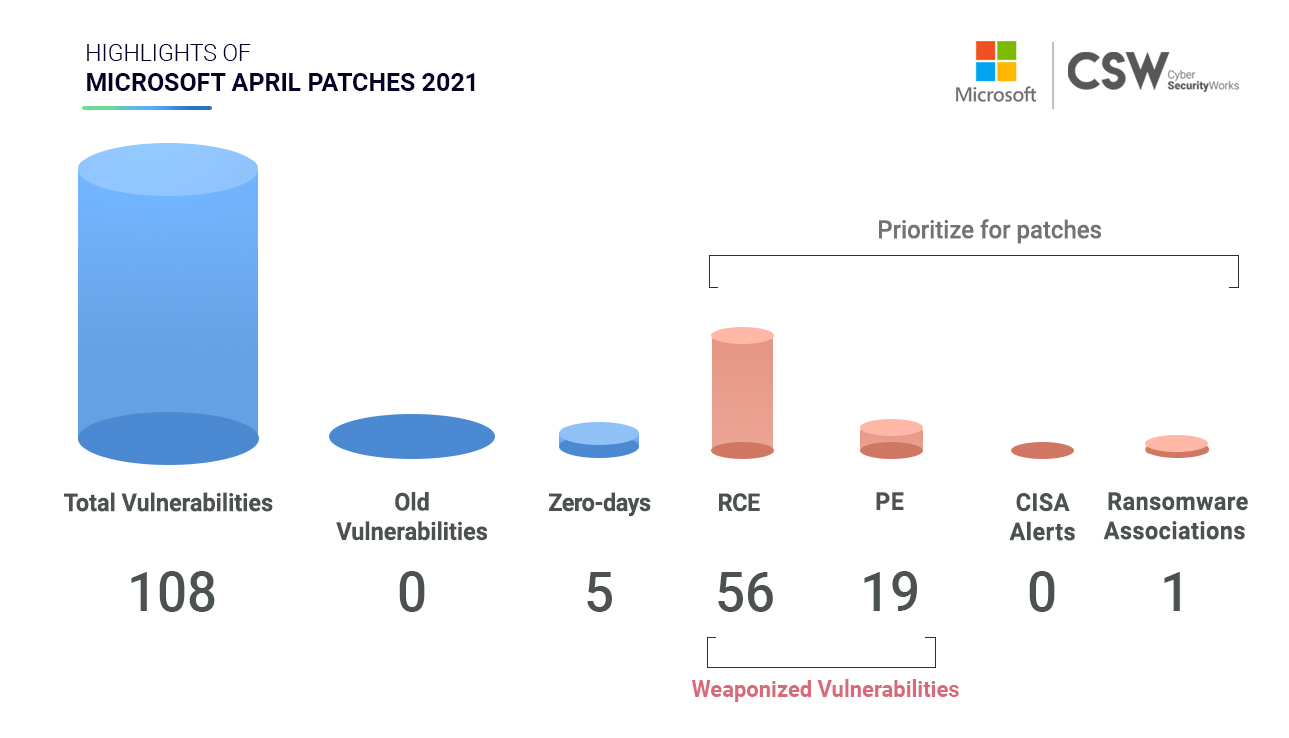
Microsoft patched 108 unique security vulnerabilities in April 2021. We analyzed these weaknesses and spotlighted important vulnerabilities that ought to be patched on priority.
Microsoft’s April Patches Overview
In April, Microsoft patched 108 vulnerabilities discovered in 2021 –
RCE/PE: Remote Code Execution and Privilege Execution are two of the most dangerous weaknesses that are most exploited by malicious actors. Microsoft has fixed –
-
56 CVEs that have been classified as RCE bugs
-
19 CVEs have Privilege Escalation capabilities
-
9 CVEs are linked to Denial of Service
Notably, four CVEs ( CVE-2021-28458, CVE-2021-27091, CVE-2021-2843, CVE-2021-28312) have publicly known exploits therefore, patching them would be essential.
The National Security Agency US has discovered four new Exchange server vulnerabilities (CVE-2021-28480, CVE-2021-28481, CVE-2021-28482, and CVE-2021-28483), which have been rated critical. Of these 2 vulnerabilities are pre-authentication weaknesses, which means unauthenticated attackers can exploit them without any user interaction.
Zero-Day Vulnerabilities: Microsoft has released 4 publicly disclosed and 1 actively exploited patches for five Zero-Day Vulnerabilities ( CVE-2021-2709, CVE-2021-28312, CVE-2021-28437, CVE-2021-28458, CVE-2021-28310)
The actively exploited CVE-2021-28310 in Win32k with Privilege Escalation capabilities is suspected to be associated with Bitter APT Group.
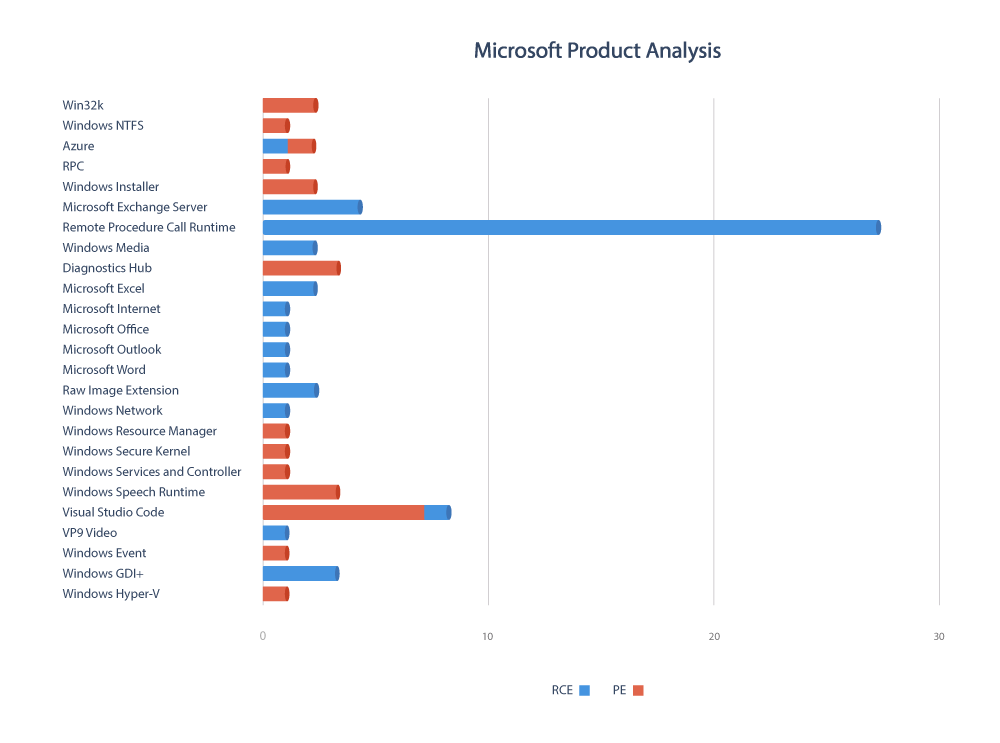
Product Analysis
Microsoft has released patches for 45 different products where 59% of security vulnerabilities accounted for RCE exploit.
Severity Scores
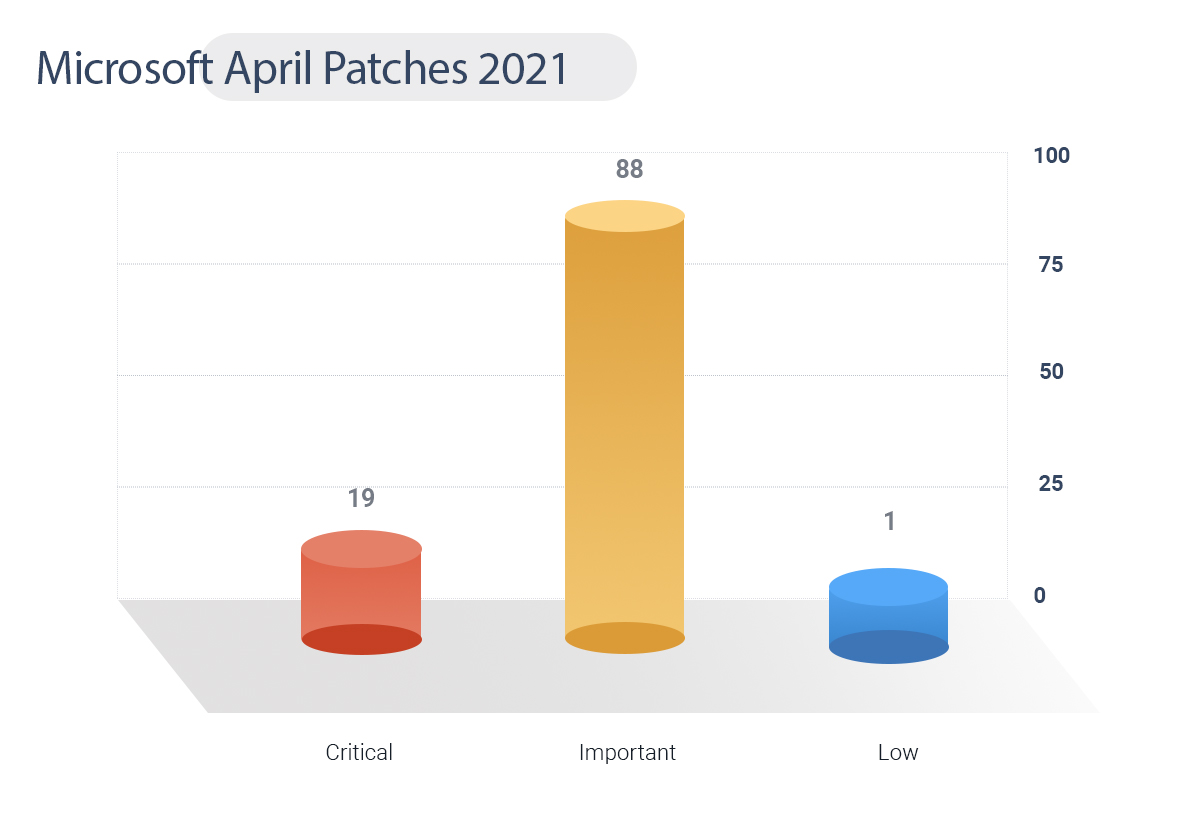
Table: Microsoft April 2021 Patches
These critical vulnerabilities are actively exploited and they need to be patched on priority.