
Threat Actors Intelligence Report: Scattered Spider
Securin Research Team
Securin Team


Jul 31, 2025
The arrest of key Scattered Spider operatives in 2024 was widely reported as a disruption success. But within weeks, intelligence analysts were tracking a new pattern: the group’s methods were being co-opted by criminal gangs across multiple sectors.
What followed is now classified as “Tactical Proliferation” – a force-multiplier effect in which a single group’s methodology becomes the operational standard for financially motivated threat actors. In other words: A new playbook for cybercriminals. Scattered Spider didn’t so much vanish as fragment, replicate and spread. It has become a codified model for scalable, high-impact cyber extortion.
Here’s everything you need to know – with some strategies for dealing with the threat.
Operational Profile: Discipline Over Innovation
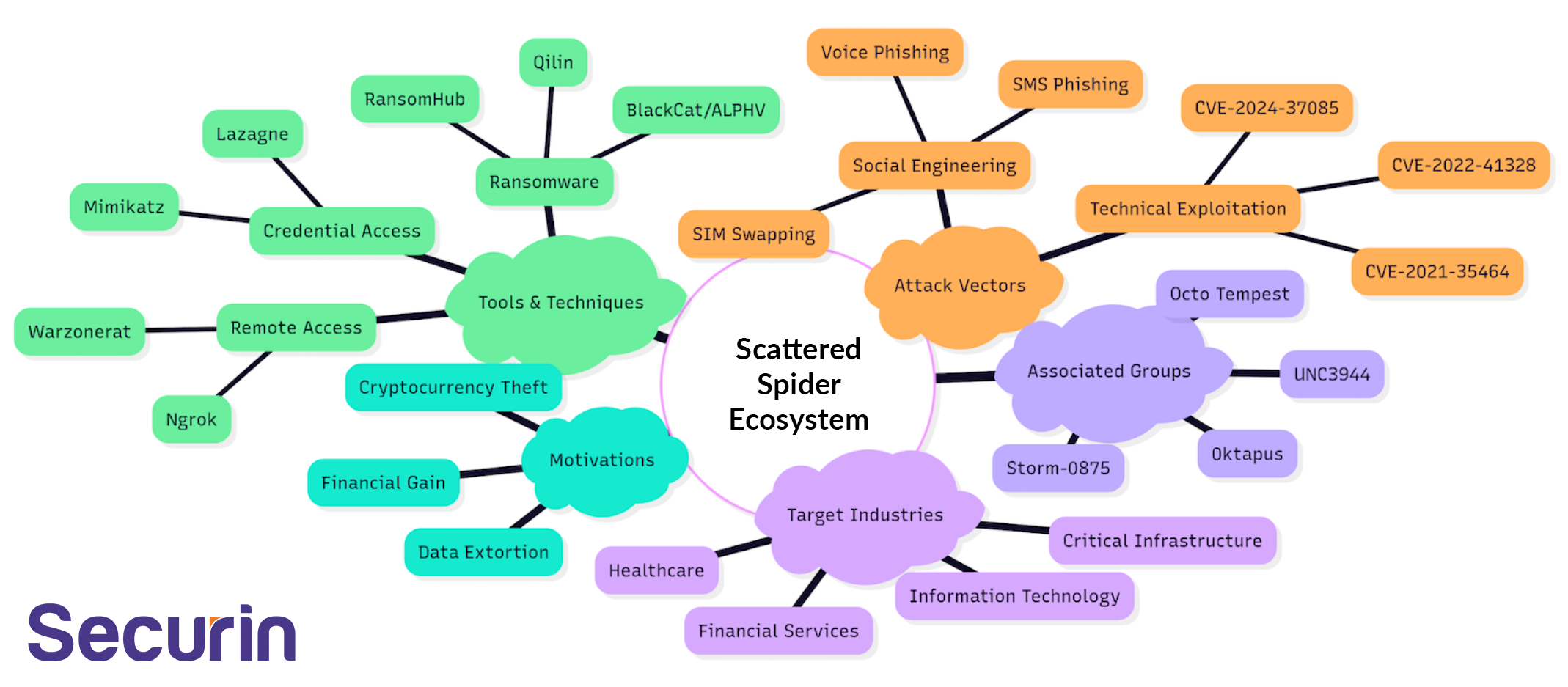
Scattered Spider’s model is distinguished by hybrid execution: combining credential-focused CVE exploitation with adaptive social engineering techniques, and layering it with dual-extortion operations.
It’s all about strategic adaptability as opposed to novel, cutting-edge malware and attack vectors. The group exploited known vulnerabilities, using widely available tools, implementing attacks systematically. When cloud defenses hardened, they pivoted to infrastructure targets. Think discipline over innovation. And it works: the group built a highly effective playbook and infrastructure with a low barrier to entry. It was efficient and, above all, repeatable – as we’re now seeing with the proliferation of copycat groups.
Attribution | Classification |
|---|---|
Threat Type | Criminal Group (High Confidence Attribution) |
State Affiliation | None Confirmed |
Primary Sectors Targeted | Financial Services Information Technology Healthcare |
Core Techniques | 54 Attack Techniques 25 Tool Relationships |
Geographic Reach | Global with a Focus on Developemed Economies |
Strategic Evolution | Cloud-First → Critical Infrastructure Targeting |
Engineered for Efficiency: Scattered Spider’s Access Methods
Scattered Spider’s vulnerability exploitation strategy is engineered for efficiency: Privilege escalation and identity compromise via low-complexity, high-impact flaws. As the tables below indicate, this is an impact-per-CVE play: instead of spray-and-pray or seeking zero-days, the group selects vulnerabilities that offer the highest privilege gain for the lowest exploitation complexity.
Initial Access CVEs
CVE ID | Vendor/Product | Risk Index | Initial Access Technique Name | Exploitation Complexity |
|---|---|---|---|---|
CVE-2021-35464 | ForgeRock AM | Critical | Exploit Public-Facing Application | Low |
CVE-2022-41328 | Fortinet FortiOS | High | Exploit Public-Facing Application | Medium |
CVE-2024-37085 | VMware ESXi | High | External Remote Services | Medium |
The initial access CVEs reveal clear intent, reflecting a deliberate pattern: target the perimeter, compromise identity, expand silently. This approach not only scales, it doesn’t require exploits – only access to exposed applications and unpatched systems.
Initial Access Techniques
Technique ID | Technique Name |
|---|---|
T1190 | Exploit Public-Facing Application |
T1133 | External Remote Services |
T1566.002 | Phishing: Spearphishing Link |
T1566.004 | Phishing: Spearphishing Voice |
T1598.001 | Phishing for Information: Spearphishing Service |
T1598.004 | Phishing for Information: Spearphishing Voice |
As the initial access techniques show, this is a two-pronged approach. Exploit both the exposed systems and the people who maintain them. What distinguishes Scattered Spider isn’t the use of phishing – it’s the granularity of it. They don’t rely exclusively on emails, but bring in SIM-swapping and reconnaissance-based pretexting to bypass Multi Factor Authentication (MFA), hijack sessions, and impersonate support functions, particularly help desk and IT roles. This layered access strategy gives great flexibility:
• If a target’s perimeter is poorly configured, T1190 or T1133 gets them in.
• If technical defenses are hardened, T1566.004 or T1598.004 lets them walk in the front door with a believable voice and an urgent request.
The philosophy is pragmatic: use what works, move laterally fast, and target identity and recovery layers. As the image shows, it’s a highly repeatable, modular threat model.
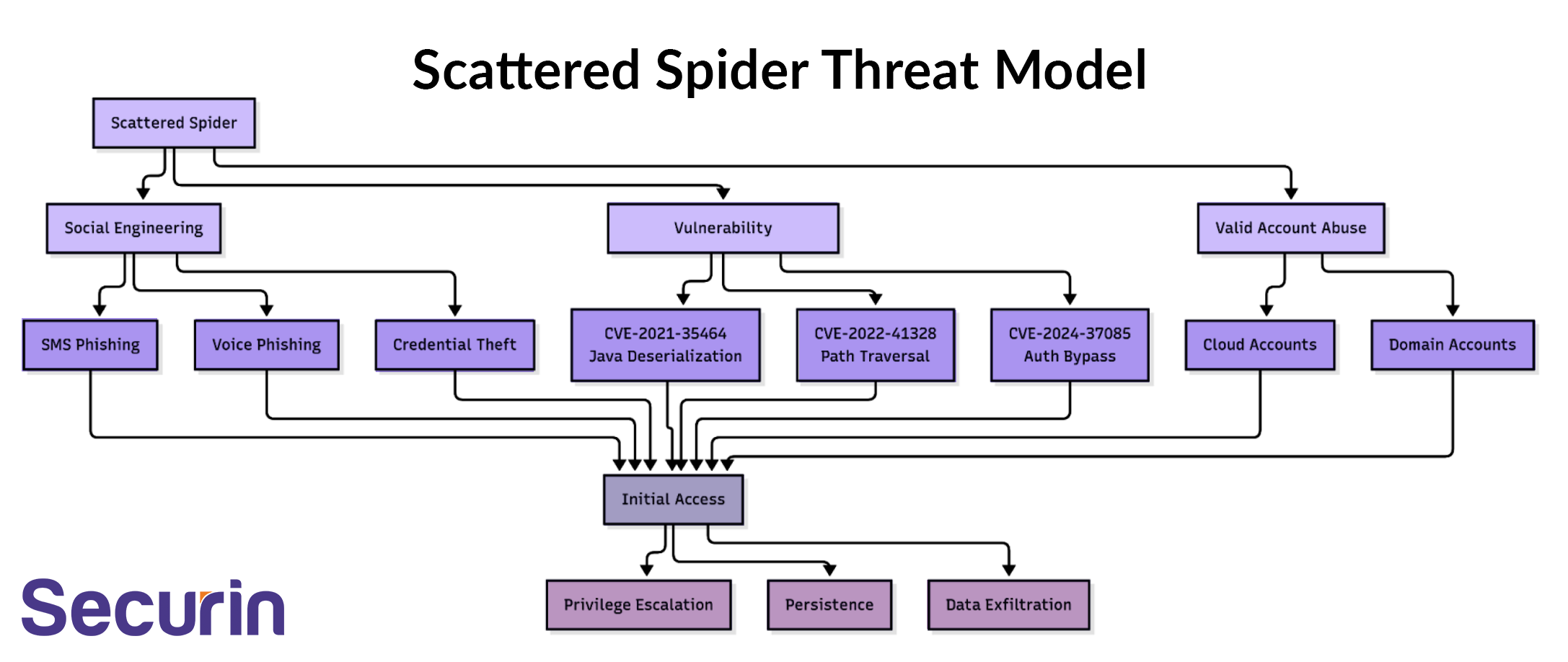
Bottom line: Scattered Spider uses whatever gets access first, and pivots from there. This is “initial access as a menu”, as opposed to a sequence. And it’s one of the key reasons why this playbook has proven so reproducible for copycat groups.
Vulnerability Intelligence Analysis
Scattered Spider’s vulnerability exploitation profile reveals a disciplined focus on identity subversion, privilege escalation, and system-level compromise. All achieved through a small, carefully selected set of high-impact vulnerabilities. As the table below shows, rather than cast a wide net, the group prioritizes CVEs with low exploitation complexity and high operational coverage. The intent is clear: minimal input for maximal access.
Vulnerability Exploitation Patterns
Vulnerability Type | CVE Count | Risk Level | Primary Impact | Exploitation Frequency |
|---|---|---|---|---|
Deserialization Flaws | 1 | Critical | Remote Code Execution | High |
Path Traversal | 1 | High | File System Access | Medium |
Authentication Bypass | 1 | High | Privilege Escalation | High |
Memory Corruption | 1 | High | Code Execution | Medium |
Privilege Escalation | 1 | High | System Compromise | High |
The pattern tells its own story:
- A deserialization flaw (CVE-2021-35464) delivers remote code execution — enabling direct execution on targeted systems with critical severity.
- A path traversal exploit provides file system access, often a precursor to lateral movement or data staging.
- An authentication bypass (CVE-2024-37085) facilitates privilege escalation — a recurring objective across the dataset.
- A memory corruption vulnerability offers another path to code execution, reinforcing the focus on execution over detection.
- Separately, a direct privilege escalation CVE completes the escalation chain with a route to system-level compromise.
Exploited CWEs (Common Weakness Enumeration)
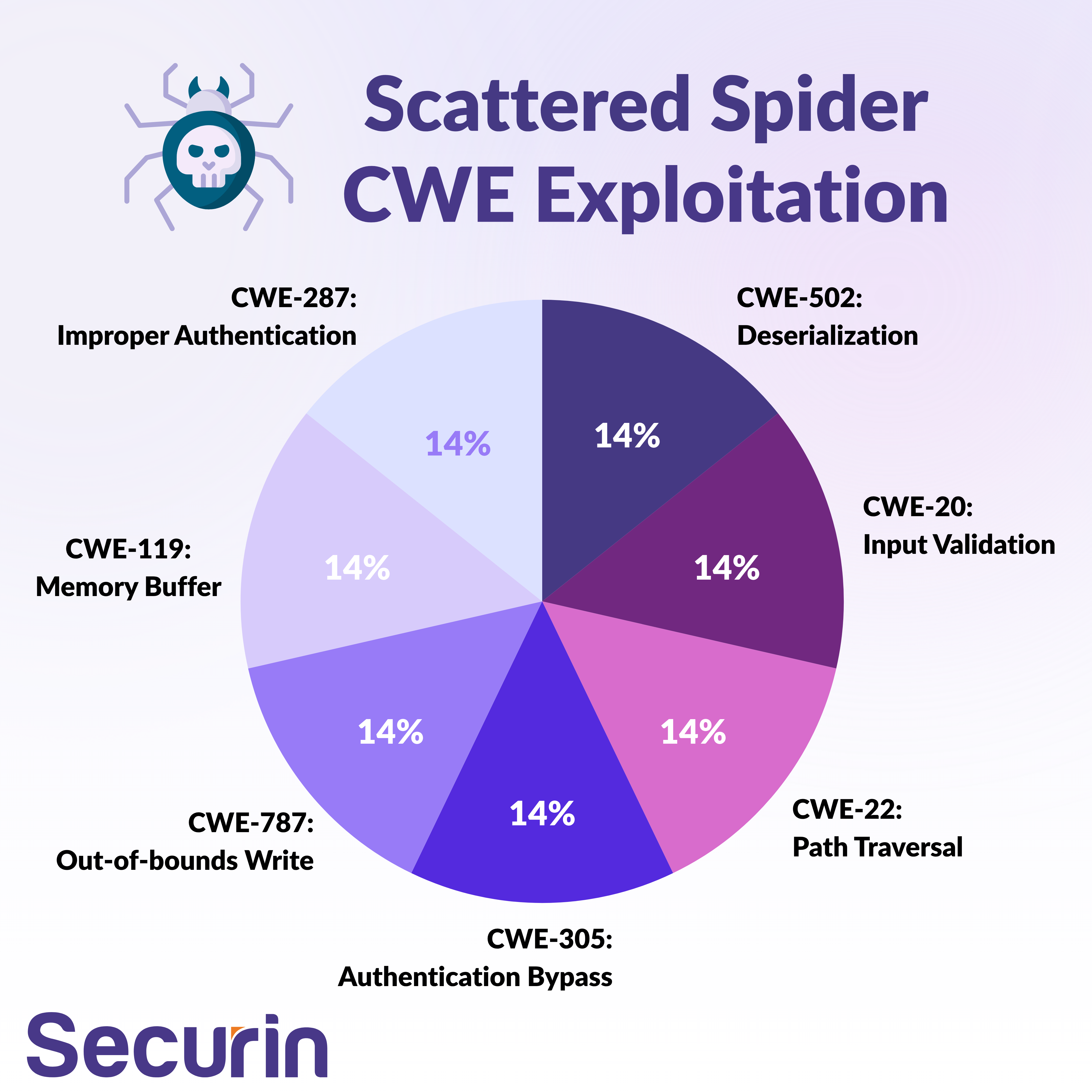
CWE ID | CWE Name | Associated CVEs | Risk Impact |
|---|---|---|---|
CWE-502 | Deserialization of Untrusted Data | CVE-2021-35464 | Critical |
CWE-20 | Improper Input Validation | CVE-2015-2291 | High |
CWE-22 | Improper Limitation of a Pathname to a Restricted Directory | CVE-2022-41328 | High |
CWE-119 | Improper Restriction of Operations within the Bounds of a Memory Buffer | CVE-2015-2291 | High |
CWE-787 | Out-of-bounds Write | CVE-2022-21882 | High |
CWE-287 | Improper Authentication | CVE-2024-37085 | High |
CWE-305 | Authentication Bypass by Primary Weakness | CVE-2024-37085 | High |
Bottom line: Start with execution. Elevate to control. Weaponize the trust model.
How does this stack up from a tactical perspective?
Tactical Analysis – Toolchain: Minimal Footprint, Maximum Effect
Scattered Spider’s tooling emphasizes low-detection profiles and legitimacy over novelty or sophistication. Their preference for living-off-the-land tactics – especially Windows-native utilities – makes traditional, signature-based detection ineffective.
Tools and Payloads
Tool Category | Primary Tools | Operational Role | Frequency |
|---|---|---|---|
Credential Access | Mimikatz, Lazagne | Credential Dumping | High |
Remote Access | Ngrok, Warzonerat | Persistence/C2 | High |
Ransomware | BlackCat, RansomHub, Qilin | Impact/Extortion | High |
Social Engineering | SMS Phishing, Phishing Websites | Initial Access | Critical |
Network Tools | Impacket | Lateral Movement | Medium |
Living Off Land | Windows Native Tools | Stealth Operations | High |
Persistence is often maintained via legitimate tools like RattyRat, while payloads like DragonForce indicate a tactical shift towards destructive operations with financial motivation.
Attack Techniques – MITRE ATT&CK
This is a full-spectrum, modular attack chain approach, covering every operational phase – from pre-access reconnaissance to post-exfiltration. Reconnaissance dominates, with techniques like account discovery, cloud infrastructure mapping, and social media intelligence gathering forming the foundation of highly targeted phishing and impersonation campaigns.
Command and control is maintained through web services, remote access software, and protocol tunneling, with final actions ranging from data encryption to financial theft – underscoring the new focus on extortion and monetization over disruption and sabotage.
Technique ID | Technique Name | Number of Sub-techniques | Purpose |
|---|---|---|---|
T1087 | Account Discovery | 4 sub-techniques | Reconnaissance |
T1018 | Remote System Discovery | 0 sub-techniques | Reconnaissance |
T1046 | Network Service Discovery | 0 sub-techniques | Reconnaissance |
T1069 | Permission Groups Discovery | 1 sub-technique | Reconnaissance |
T1083 | File and Directory Discovery | 0 sub-techniques | Reconnaissance |
T1217 | Browser Information Discovery | 0 sub-techniques | Reconnaissance |
T1538 | Cloud Service Dashboard | 0 sub-techniques | Reconnaissance |
T1580 | Cloud Infrastructure Discovery | 0 sub-techniques | Reconnaissance |
T1589 | Gather Victim Identity Information | 1 sub-technique | Reconnaissance |
T1593 | Search Open Websites/Domains: Social Media | 1 sub-techniques | Reconnaissance |
T1594 | Search Victim-Owned Websites | 0 sub-techniques | Reconnaissance |
T1597 | Search Closed Sources: Purchase Technical Data | 1 sub-techniques | Reconnaissance |
T1583 | Acquire Infrastructure: Domains | 1 sub-techniques | Resource Development |
T1585 | Establish Accounts: Social Media Accounts | 1 sub-techniques | Resource Development |
T1588 | Obtain Capabilities | 1 sub-technique | Resource Development |
T1566 | Phishing | 3 sub-techniques | Initial Access |
T1190 | Exploit Public-Facing Application | 0 sub-techniques | Initial Access |
T1204 | User Execution | 1 sub-technique | Initial Access |
T1656 | Impersonation | 0 sub-techniques | Initial Access |
T1660 | Phishing | 1 sub-technique | Initial Access |
T1199 | Trusted Relationship | 0 sub-techniques | Initial Access |
T1078 | Valid Accounts: Domain Accounts | 0 sub-techniques | Initial Access |
T1648 | Serverless Execution | 0 sub-techniques | Execution |
T1098 | Account Manipulation | 3 sub-techniques | Persistence |
T1133 | External Remote Services | 0 sub-techniques | Persistence |
T1136 | Create Account | 1 sub-technique | Persistence |
T1451 | SIM Card Swap | 0 sub-techniques | Persistence |
T1068 | Exploitation for Privilege Escalation | 0 sub-techniques | Privilege Escalation |
T1598 | Phishing for Information | 4 sub-techniques | Credential Harvesting |
T1003 | OS Credential Dumping | 2 sub-techniques | Credential Access |
T1552 | Unsecured Credentials | 2 sub-techniques | Credential Access |
T1006 | Direct Volume Access | 0 sub-techniques | Credential Access |
T1539 | Steal Web Session Cookie | 0 sub-techniques | Credential Access |
T1621 | Multi-Factor Authentication Request Generation | 0 sub-techniques | Credential Access |
T1021 | Remote Services | 1 sub-technique | Lateral Movement |
T1047 | Windows Management Instrumentation | 0 sub-techniques | Lateral Movement |
T1556 | Modify Authentication Process | 4 sub-techniques | Defense Evasion |
T1078 | Valid Accounts | 2 sub-techniques | Defense Evasion |
T1484 | Domain Policy Modification | 2 sub-techniques | Defense Evasion |
T1553 | Subvert Trust Controls | 1 sub-technique | Defense Evasion |
T1564 | Hide Artifacts | 1 sub-technique | Defense Evasion |
T1578 | Modify Cloud Compute Infrastructure | 2 sub-techniques | Defense Evasion |
T1213 | Data from Information Repositories | 4 sub-techniques | Data Collection |
T1074 | Data Staged | 0 sub-techniques | Data Collection |
T1114 | Email Collection | 0 sub-techniques | Data Collection |
T1530 | Data from Cloud Storage | 0 sub-techniques | Data Collection |
T1567 | Exfiltration Over Web Service | 1 sub-technique | Exfiltration |
T1090 | Proxy | 0 sub-techniques | Command and Control |
T1102 | Web Service | 0 sub-techniques | Command and Control |
T1105 | Ingress Tool Transfer | 0 sub-techniques | Command and Control |
T1219 | Remote Access Software | 0 sub-techniques | Command and Control |
T1572 | Protocol Tunneling | 0 sub-techniques | Command and Control |
T1486 | Data Encrypted for Impact | 0 sub-techniques | Impact |
T1657 | Financial Theft | 0 sub-techniques | Impact |
The sheer breadth of ATT&CK techniques reinforces Scattered Spider’s methodical planning and tactical versatility.
Who is Scattered Spider Targeting?
As the diagram below shows, Scattered Spider’s campaign shows a disciplined focus on high-value verticals, not random opportunism. This group prioritizes economic impact and operational interconnectivity over sheer volume.
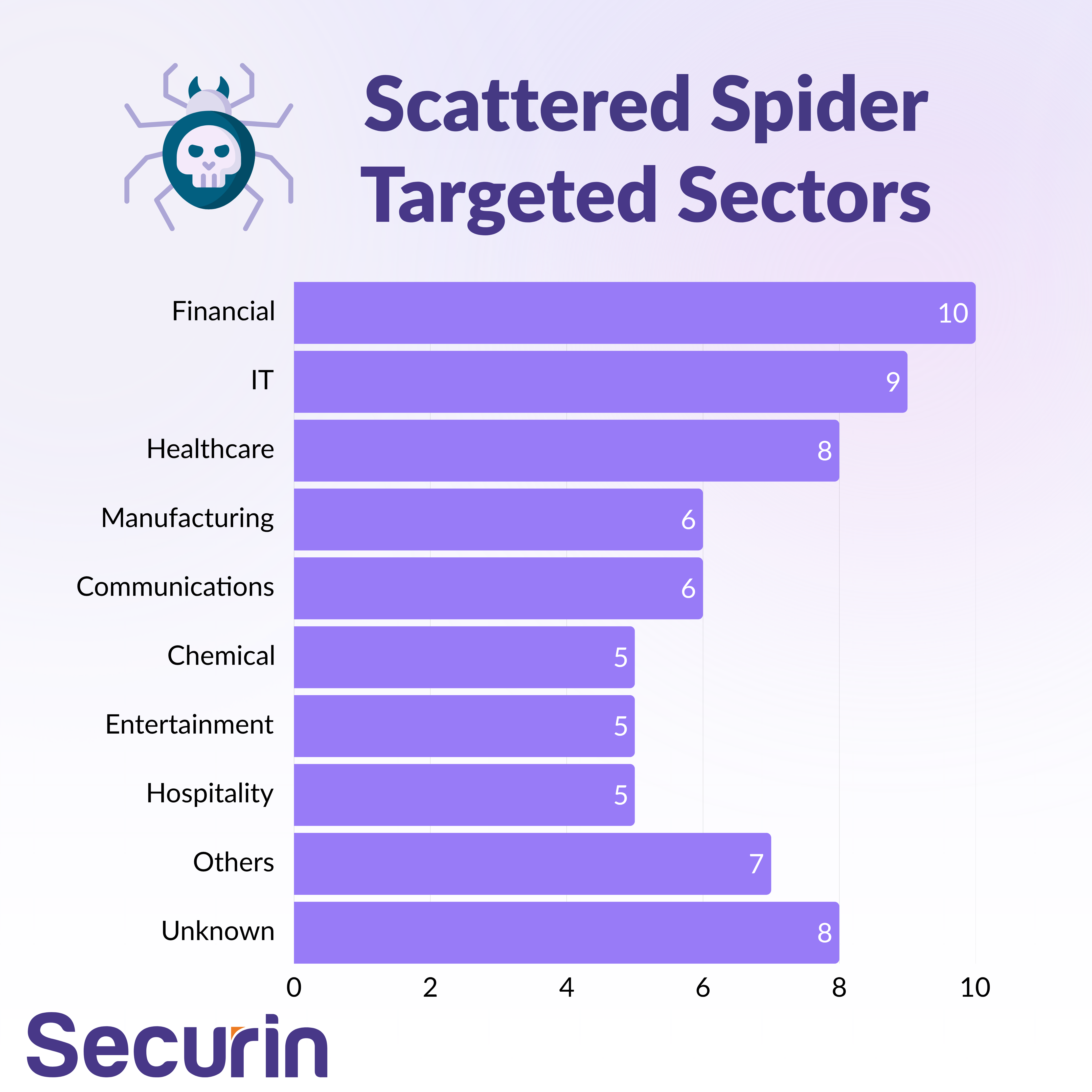
From a geographic perspective, we see alignment with developed, Anglophone economies, maximizing financial potential and exploitable operational similarities. The U.S. and U.K. are primary targets, followed by Australia and Canada.
Geographic Targeting Distribution
Region | Target Countries | Strategic Rationale |
|---|---|---|
Global | Worldwide Operations | Financial gain maximization across developed economies |
Primary Focus | United States, United Kingdom | High-value targets with advanced financial infrastructure |
Secondary | Canada, Australia | English-speaking targets with similar business practices |
Capability Profile: Mature Tradecraft Across the Kill Chain
As the table below indicates, Scattered Spider demonstrates high operational maturity across core adversarial domains. The group’s social engineering is classified as advanced, and technically they maintain high exploitation capability, chaining CVEs across vendors to compromise critical systems. Intelligence gathering and persistence are standout strengths – this is a threat actor operating with repeatable, scalable techniques, not opportunistic chaos.
Operational Classification
Capability Category | Assessment Level | Evidence/Indicators |
|---|---|---|
Social Engineering | Advanced | Sophisticated SMS/voice phishing, SIM swapping |
Technical Exploitation | High | 5 CVEs across multiple vendors, complex attack chains |
Operational Security | High | Successful evasion of law enforcement until recent arrests |
Tool Development | Medium | Primarily uses existing tools with custom configurations |
Intelligence Gathering | Advanced | Detailed target reconnaissance, insider knowledge |
Persistence Mechanisms | High | Cloud infrastructure abuse, legitimate tool exploitation |
Scattered Spider: Current Threat Landscape
Recent Activity Patterns
Recent intelligence indicates a significant operational shift following targeted arrests in 2024, with original Scattered Spider activity substantially decreasing while copycat threat actors rapidly adopt their sophisticated social engineering playbook. CISA and international partners released updated joint advisories highlighting the group's evolution toward more advanced tactics, including deployment of DragonForce ransomware and exploitation of legitimate tools like RattyRAT for persistent access.
The threat landscape shows concerning tactical proliferation as multiple financially motivated actors target backup systems using Scattered Spider's proven methodologies. Microsoft reports the group has shifted from cloud-first strategies to targeting critical infrastructure sectors, including airlines, maintaining their dual-extortion model of data theft followed by ransomware deployment. This operational adaptability demonstrates continued threat evolution despite law enforcement pressure.
Active Campaigns and TTPs
Campaign | Target Sectors | Primary TTPs | Vulnerabilities Exploited | Timeline |
|---|---|---|---|---|
Post-Arrest Operations | Airlines, Critical Infrastructure | Social Engineering, DragonForce Ransomware | CVE-2024-37085 | 2024-Present |
Copycat Proliferation | Financial Services, Healthcare | SMS Phishing, Backup System Targeting | Legacy CVEs | 2024-Present |
Cloud Infrastructure Attacks | IT Services, SaaS Providers | Valid Account Abuse, Cloud Service Dashboard | Authentication Bypass | Ongoing |
Risk Assessment and Mitigation
Defensive Recommendations
Immediate Actions:
• Prioritize patching of deserialization vulnerabilities (CVE-2021-35464) and authentication bypass flaws (CVE-2024-37085)
• Implement enhanced monitoring for social engineering attacks targeting help desk and IT support functions
• Deploy multi-factor authentication with phishing-resistant methods across all cloud and critical systems
Strategic Recommendations:
• Zero-trust architecture implementation focusing on identity verification and conditional access policies
• Enhanced threat intelligence sharing frameworks for social engineering attack indicators
• Critical infrastructure hardening against social engineering and legitimate tool abuse
Risk Mitigation Framework
Risk Category | Mitigation Strategy | Implementation Priority | Expected Impact |
|---|---|---|---|
Social Engineering | Employee training, verification procedures | Critical | High |
Vulnerability Exploitation | Patch management, vulnerability scanning | High | High |
Credential Compromise | MFA, privileged access management | Critical | High |
Ransomware Deployment | Backup security, network segmentation | High | Medium |
Cloud Infrastructure Abuse | Cloud security posture management | High | Medium |
Future Threat Projections
Evidence-based assessment indicates continued tactical proliferation of Scattered Spider's methodologies across multiple threat actor groups, effectively democratizing advanced social engineering capabilities. The integration of artificial intelligence and machine learning into social engineering attacks represents the next evolution phase, with projected capability advancement in voice synthesis and personalized phishing content generation.
Operational model evolution toward distributed-but-coordinated approaches will likely continue, with copycat groups maintaining tactical alignment while operating independently. Strategic targeting shifts toward critical infrastructure and supply chain providers are projected to intensify, leveraging interconnected business dependencies for maximum impact. Timeline projections suggest full tactical proliferation across financially motivated threat actors within 12-18 months.


