
Threat Actors Intelligence Report: Russia
Securin Research Team
Securin Team


Oct 8, 2025
Russia’s cyber operations represent one of the most aggressive, expansive, and coordinated state-backed campaigns in the world. Securin’s research identifies 178 state-sponsored threat groups exploiting 202 unique vulnerabilities across more than 50 countries, focused on Ukraine, Europe, and North America. Actors including Fancy Bear (APT28), Cozy Bear (APT29), Sandworm (APT44), and FIN7 employ zero-day exploits, wiper malware, and supply chain attacks. In 2024, Ukraine reported a 69.8% surge in infrastructure attacks (4,315 incidents, per Ukraine’s SSSCIP), while APT28 disrupted democratic processes, notably the 2016 U.S. and 2017 French presidential elections, APT29 advanced cloud-based espionage, Sandworm’s elevation to APT44, and FIN7’s expansion into critical infrastructure sectors.
These Russian campaigns demonstrate more than technical skill — they reflect a strategic intent to destabilize democracies, disrupt critical systems, and extend Russian influence globally. Their scale, persistence, and integration make Russian cyber activity a systemic security threat, posing immediate risks to global cybersecurity and democratic institutions.

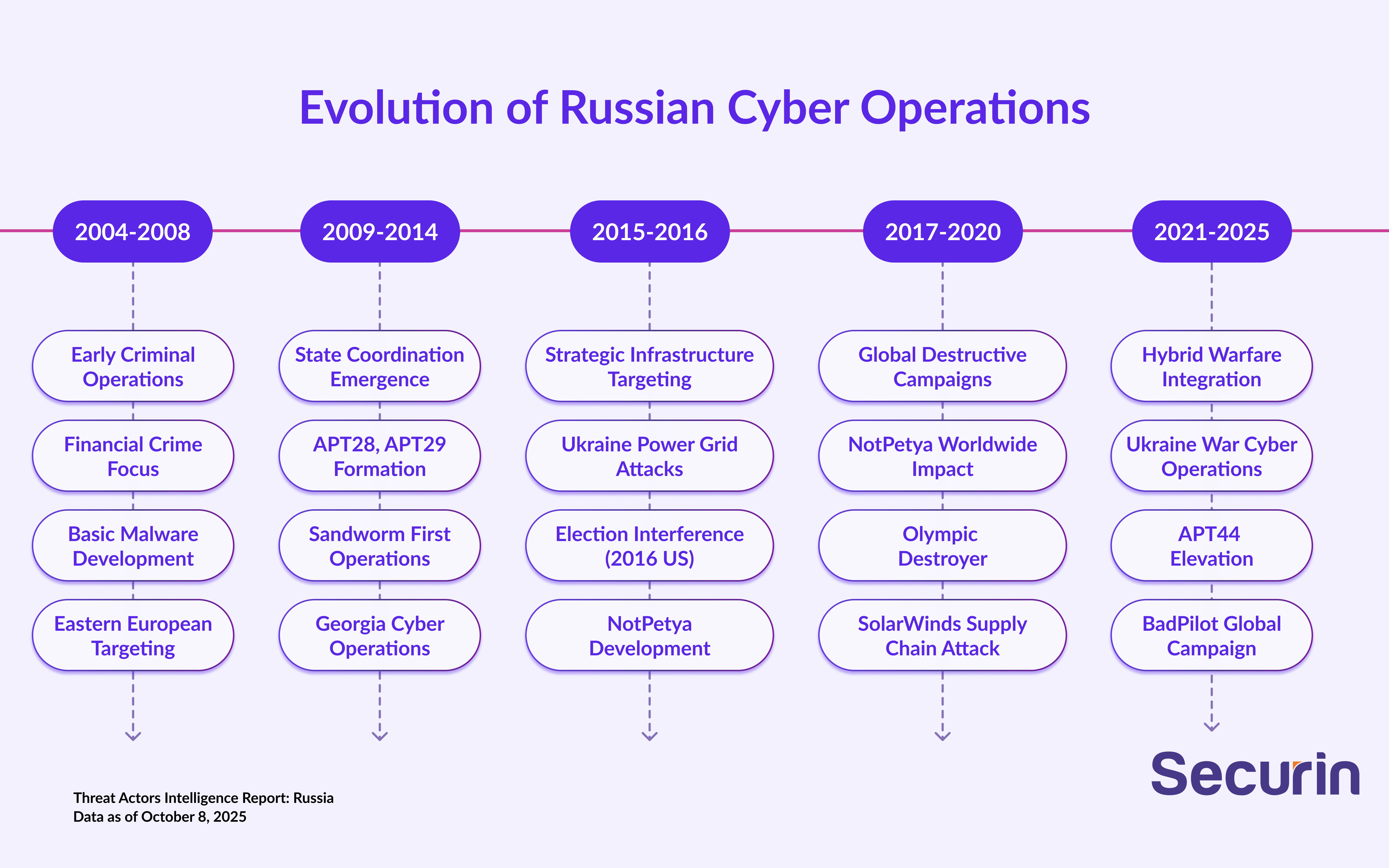
The image above provides a snapshot of key Russian threat groups, their strategies, and capabilities.
Key Findings
• 178 distinct Russian threat groups form a coordinated cyber warfare ecosystem.
• Operations are explicitly government-backed, with direct attribution to Russian intelligence services; the Main Directorate of the General Staff (GRU), the Foreign Intelligence Service (SVR), and the Federal Security Service (FSB).
• Priority targets include government facilities, financial services, and information technology providers.
• At least 202 unique vulnerabilities have been exploited, with emphasis on critical infrastructure and enterprise systems.
• Capabilities encompass destructive malware, supply chain infiltration, and hybrid warfare operations.
• Operations span more than 50 countries, with concentrated targeting of Ukraine, NATO allies, and Western democracies.
Strategic Implications
• Russia commands one of the world’s most aggressive and destructive state-sponsored cyber capabilities.
• Attacks on critical infrastructure and supply chains are escalating in scale and sophistication.
• Cyber operations are fully integrated with conventional military campaigns and information warfare.
• Systematic targeting of democratic institutions and elections poses an enduring threat to global security and stability.
Vulnerability Exploitation Intelligence
Securin’s analysis of Russian threat actors examines the top CVEs they exploit, the vendors and products they target, the industries they focus on, the techniques and tools they employ, and the specific software weaknesses (CWEs) they leverage.
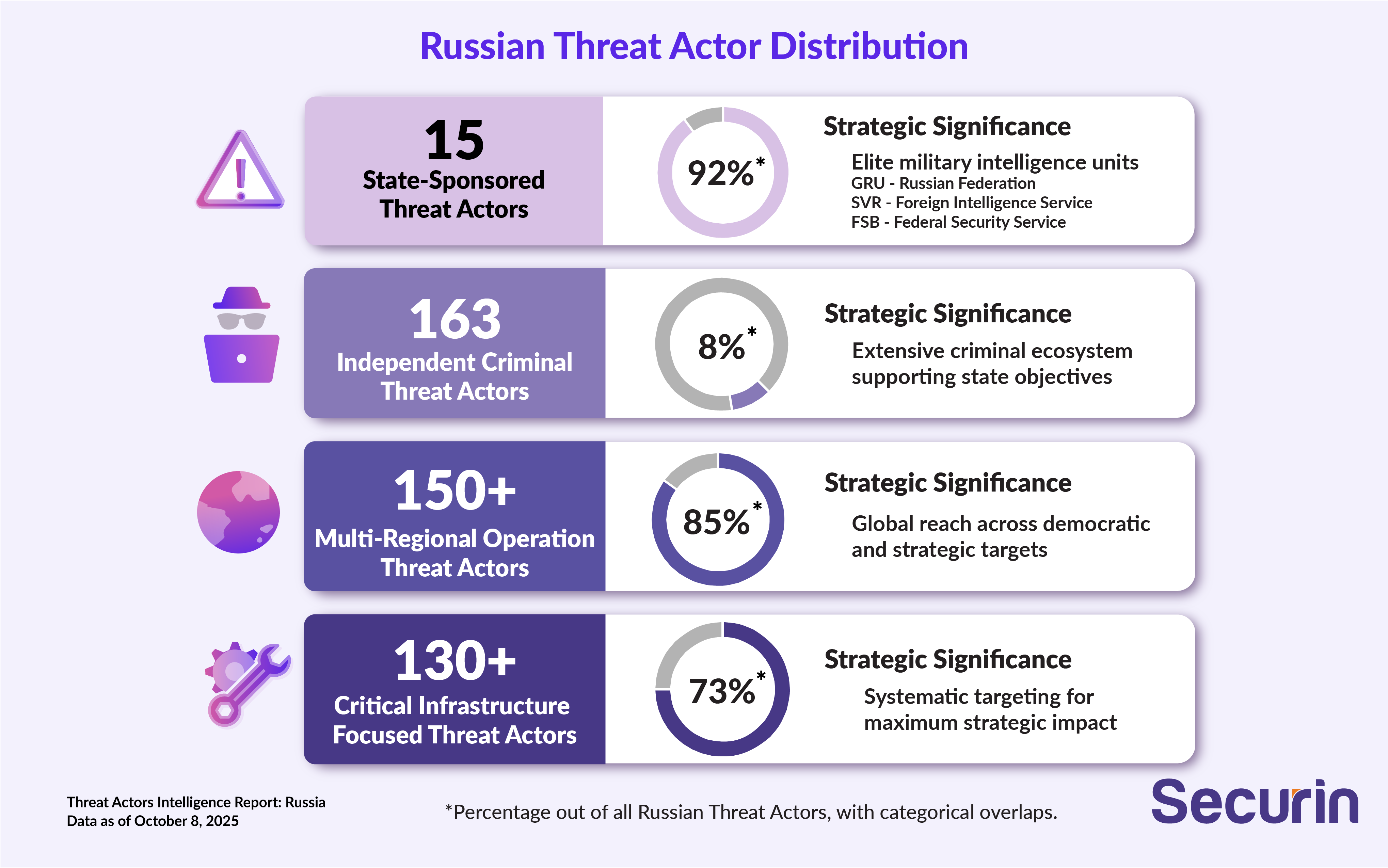
Russia’s cyber operations use a hybrid model, where a small number of elite state-sponsored groups coordinate with a broader criminal ecosystem. This structure delivers flexibility, plausible deniability, and extended operational reach, supporting state objectives. Criminal groups serve as initial access brokers, reconnaissance assets, and cover for sensitive operations. Notably, 15 elite groups account for 92% of high-impact activity, while the remaining 163 groups contribute only 8%, highlighting the outsized influence of a few core operators.
Top Vulnerabilities Exploited by Russian Threat Actors
CVE ID | Risk Score | CVSS v3 | Product/Vendor | CISA KEV | Exploitation Impact |
|---|---|---|---|---|---|
CVE-2022-26134 | 9.97 | 9.8 | Atlassian Confluence | ✓ | Remote Code Execution |
CVE-2023-47246 | 9.94 | 9.8 | SysAid Server | ✓ | Path Traversal |
CVE-2024-55591 | 9.94 | 9.8 | CyberPanel | ✓ | Remote Code Execution |
CVE-2021-26855 | 9.91 | 9.1 | Microsoft Exchange | ✓ | Server-Side Request Forgery |
CVE-2023-34362 | 9.91 | 9.8 | MOVEit Transfer | ✓ | SQL Injection |
CVE-2023-23397 | 9.88 | 9.8 | Microsoft Outlook | ✓ | Elevation of Privilege |
CVE-2023-3519 | 9.88 | 9.8 | Citrix NetScaler | ✓ | Code Injection |
CVE-2014-8361 | 9.88 | 9.8 | RealtekSDK | ✓ | Stack Buffer Overflow |
CVE-2021-35211 | 9.85 | 10.0 | Serv-U FTP Server | ✓ | Privilege Escalation |
CVE-2023-20198 | 9.82 | 10.0 | Cisco IOS XE | ✓ | Privilege Escalation |
The table highlights Russia’s focus on high-impact enterprise and government systems, including communication platforms (Exchange, Confluence), network infrastructure (Cisco, Citrix), and file transfer systems (MOVEit, Serv-U). The emphasis on Microsoft products reflects their ubiquity, while targeting network appliances shows a systematic focus on perimeter security.
Top Vendors Targeted

Vendor | Vulnerability Count | Strategic Significance |
|---|---|---|
Microsoft | 89,054+ | Enterprise and government system dominance |
Google | 83,142+ | Browser and cloud infrastructure targeting |
Cisco | 27,860+ | Network infrastructure and critical systems |
RedHat | 18,950+ | Enterprise Linux and open-source targeting |
Mozilla | 16,454+ | Alternative browser and email client targeting |
Adobe | 14,067+ | Content creation and document systems |
F5 | 7,829+ | Application delivery and load balancing |
Samba | 5,090+ | File sharing and network services |
Oracle | 3,622+ | Database and enterprise applications |
Apple | 3,360+ | macOS and iOS platform targeting |
Based on our research, Russia’s vendor targeting pattern reflects a strategic focus on widely used enterprise systems to maximize reach and damage. Microsoft products are the primary target due to their dominance in government and enterprise environments, while attacks on network infrastructure (Cisco, F5) and open-source platforms (RedHat, Samba) reveal a systematic effort to breach perimeters and exploit core enterprise systems.
Top Industries Targeted
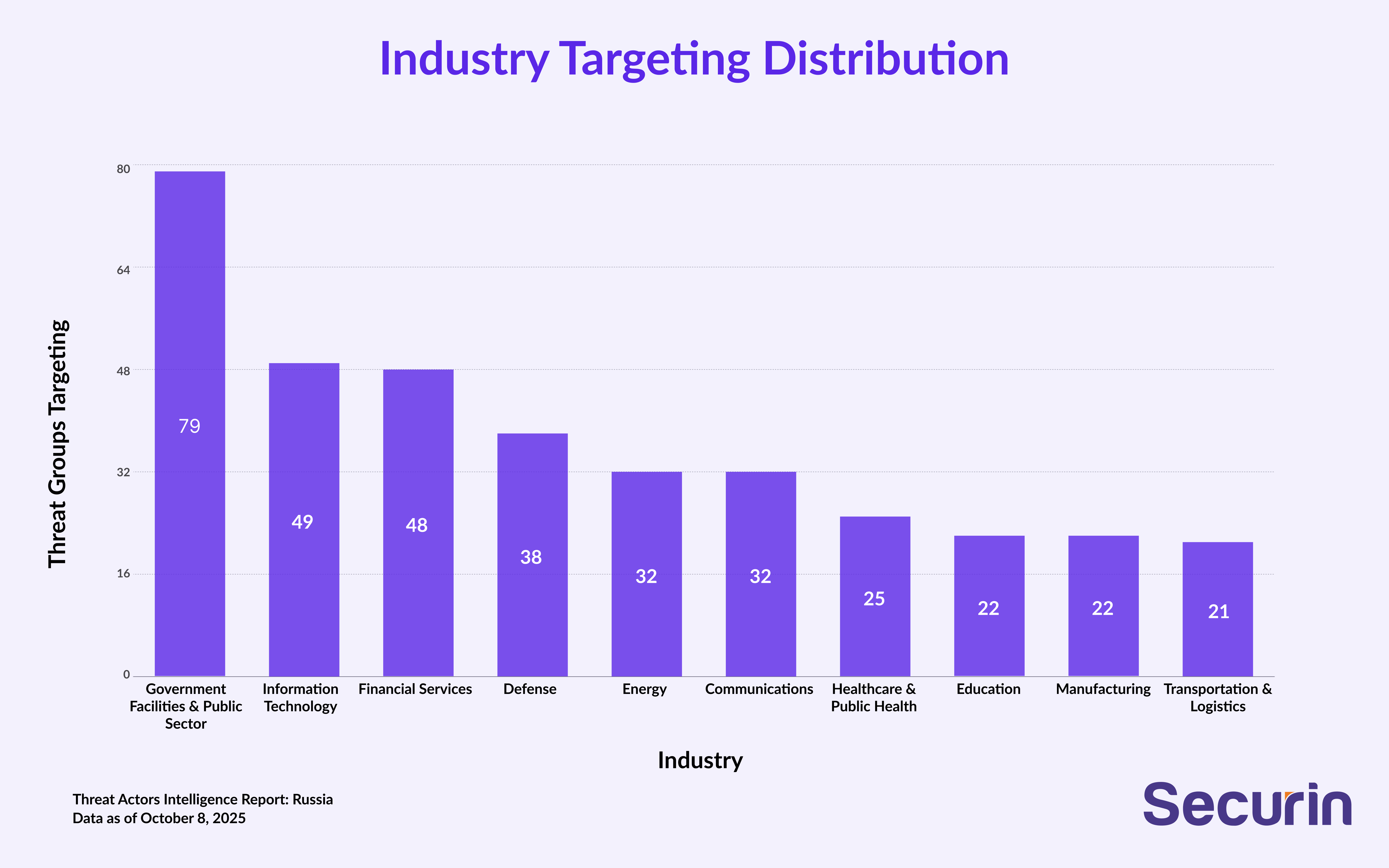
Industry | Groups Targeting | Strategic Rationale |
|---|---|---|
Government Facilities & Public Sector | 79 | Strategic intelligence and political influence |
Information Technology | 49 | Supply chain access and critical infrastructure |
Financial Services | 48 | Economic warfare and sanctions evasion |
Defense | 38 | Military intelligence and operational disruption |
Energy | 32 | Critical infrastructure and strategic leverage |
Communications | 32 | Information warfare and surveillance capabilities |
Healthcare & Public Health | 25 | Social disruption and intelligence collection |
Education | 22 | Research intelligence and long-term influence |
Manufacturing | 22 | Industrial espionage and supply chain targeting |
Transportation & Logistics | 21 | Infrastructure disruption and military support |
The chart above highlights how Russian cyber operations act like a state-sponsored cyber army, focusing on government, financial, and IT/communications sectors. Of 178 groups, 79 target government systems, with 15 elite groups responsible for 92% of high-impact activity, reflecting a coordinated strategy of espionage, political influence, economic warfare, and supply chain compromise.
Top Attack Techniques (MITRE ATT&CK)
Technique ID | Technique Name | Groups Using | Operational Purpose |
|---|---|---|---|
T1190 | Exploit Public-Facing Application | 35 | Initial access through perimeter systems |
T1566.002 | Phishing: Spearphishing Link | 35 | Social engineering and credential theft |
T1078 | Valid Accounts | 32 | Persistent access and lateral movement |
T1566.001 | Phishing: Spearphishing Attachment | 30 | Malware delivery and initial compromise |
T1133 | External Remote Services | 27 | Persistent remote access establishment |
T1195.002 | Supply Chain Compromise | 19 | Systematic infrastructure targeting |
T1059.001 | PowerShell | 16 | Living-off-the-land execution |
T1547.001 | Registry Run Keys / Startup Folder | 13 | Persistence establishment |
T1204.002 | User Execution: Malicious File | 13 | Social engineering exploitation |
T1059.003 | Windows Command Shell | 13 | System administration tool abuse |
The table below on technique distribution highlights Russia’s focus on legitimate system exploitation, social engineering, and supply chain compromises, reflecting a systematic approach to enterprise, government, and strategic infrastructure targeting.

Tool/Malware | Groups Using | Primary Function | Sophistication Level |
|---|---|---|---|
Cobalt Strike | 17 | Command & Control, Post-Exploitation | Advanced |
PsExec | 12 | Lateral Movement, Remote Execution | Intermediate |
Mimikatz | 11 | Credential Harvesting, Authentication | Advanced |
Living Off The Land | 7 | Defense Evasion, Stealth | Advanced |
AdFind | 6 | Active Directory Reconnaissance | Intermediate |
Net | 6 | Network Enumeration | Basic |
Meterpreter | 6 | Post-Exploitation Framework | Advanced |
Trickbot | 5 | Banking Trojan, Ransomware Delivery | Advanced |
WhisperGate | 5 | Destructive Wiper Malware | Advanced |
BloodHound | 5 | Active Directory Mapping | Advanced |
Based on Securin’s analysis, Russian threat actor tool use shows a sophisticated grasp of enterprise environments, prioritizing credential theft and lateral movement. Widespread use of Cobalt Strike signals professionalization, while WhisperGate highlights sabotage capabilities. The blend of commercial tools and custom malware reflects operational flexibility and ambitions beyond espionage.
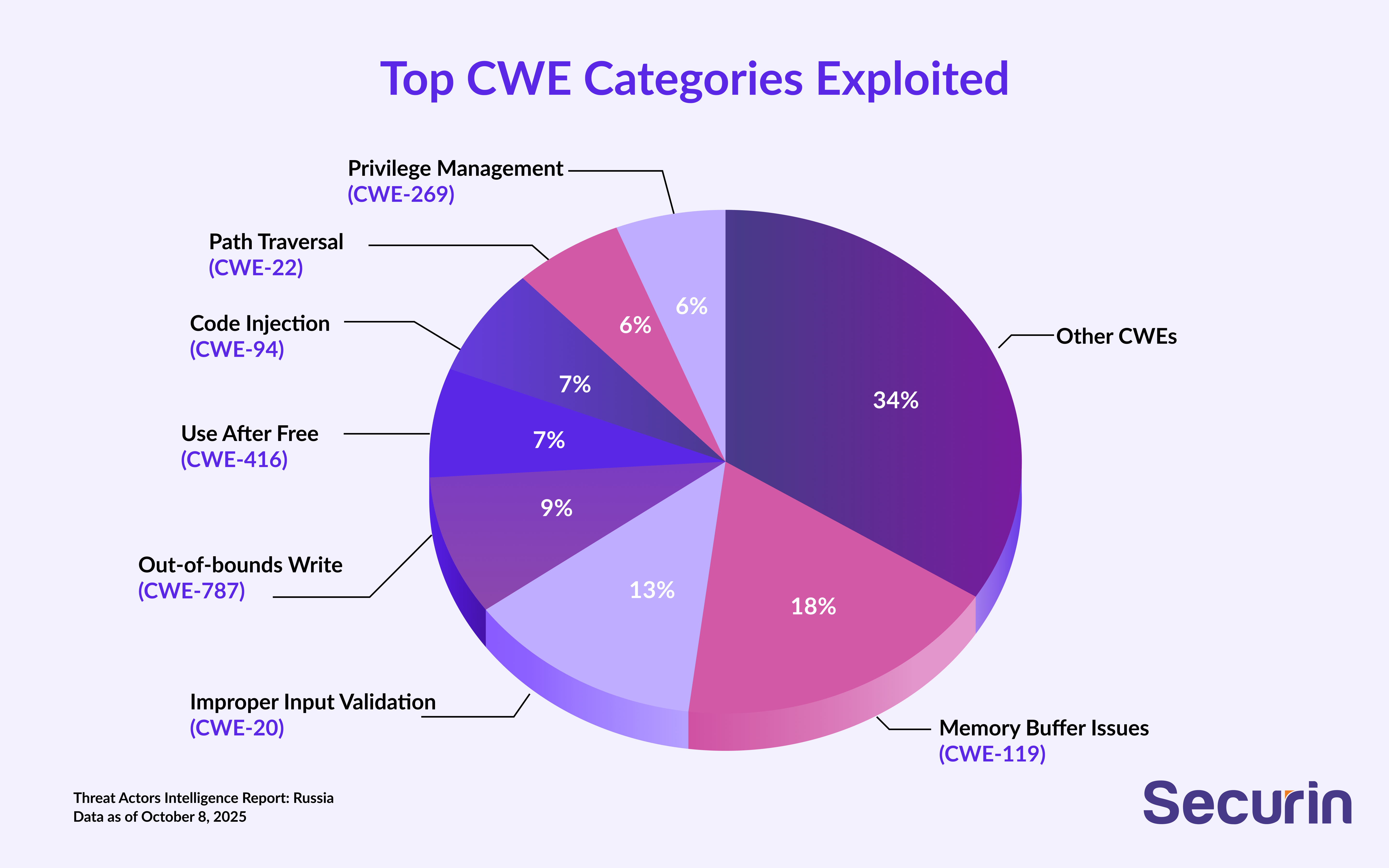
CWE ID | Weakness Name | Vulnerability Count | Exploitation Impact |
|---|---|---|---|
CWE-119 | Memory Buffer Boundary Issues | 76 | Memory corruption, system compromise |
CWE-20 | Improper Input Validation | 55 | Remote code execution, data manipulation |
CWE-787 | Out-of-bounds Write | 39 | Memory corruption, privilege escalation |
CWE-416 | Use After Free | 29 | Memory corruption, arbitrary code execution |
CWE-94 | Code Injection | 29 | Arbitrary code execution |
CWE-22 | Path Traversal | 26 | Unauthorized file access |
CWE-269 | Improper Privilege Management | 24 | Privilege escalation |
CWE-287 | Improper Authentication | 21 | Authentication bypass |
CWE-78 | OS Command Injection | 19 | System command execution |
CWE-434 | Type Confusion | 14 | Memory corruption, code execution |
The chart highlights Russia’s focus on fundamental software vulnerabilities, with heavy targeting of memory corruption and system-level exploits. Buffer overflows and use-after-free flaws show advanced exploitation capability, while input validation and authentication weaknesses are used for initial access and privilege escalation.
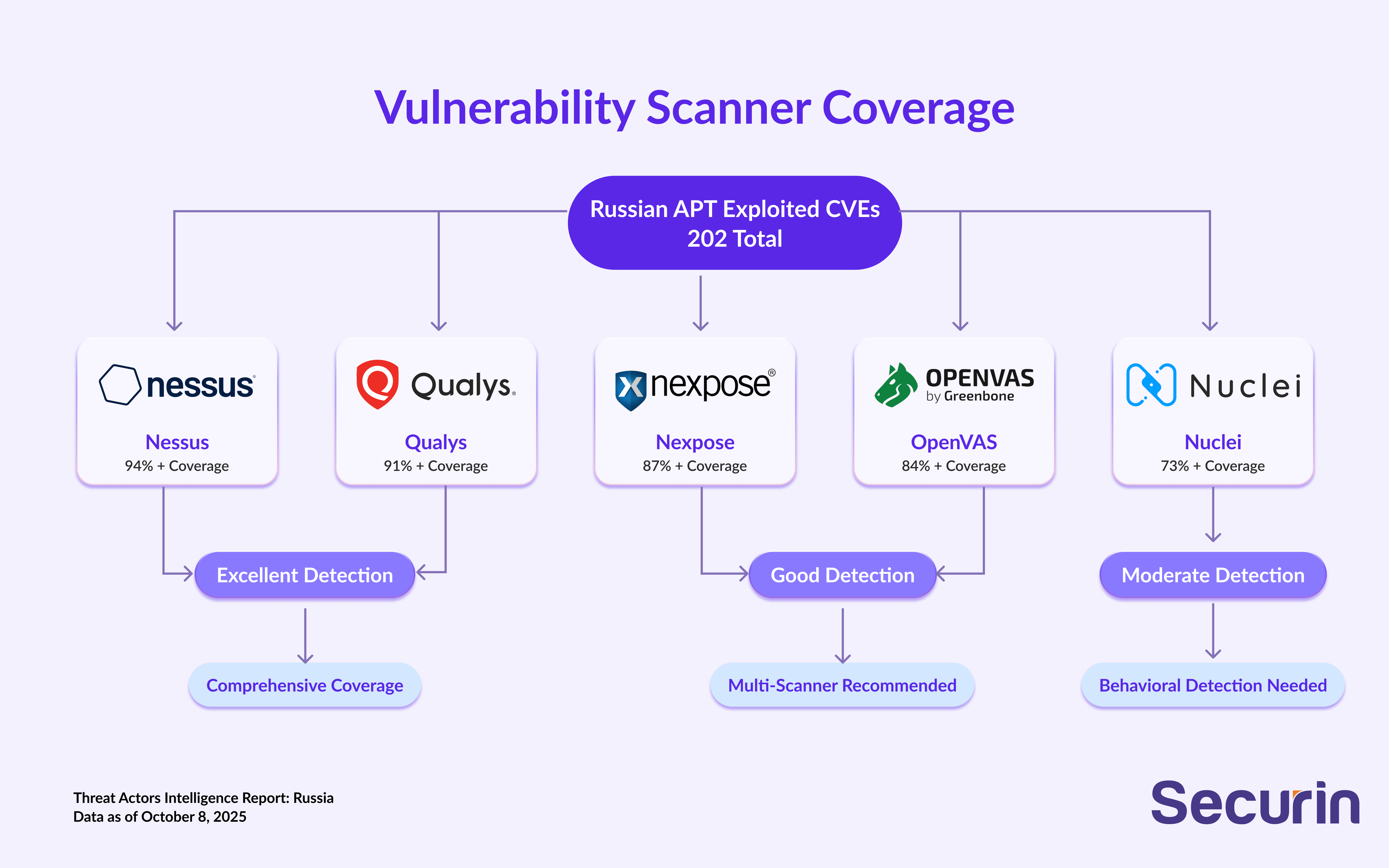
Scanner Coverage Analysis
• Security scanners detect most Russian exploits, but coverage is weaker than for Chinese threats because Russia relies more on zero-days and supply chain attacks.
• Gaps require rapid patching and behavioral detection.
• High-risk areas include destructive malware and living-off-the-land techniques.
The Convergence of Crime and State: Russia’s Cyber Evolution
Starting in the early 2000s with financial malware, Russian cyber operations grew into a sophisticated state-sponsored ecosystem. By 2014, Russia’s top three threat groups—Sandworm (APT44), APT28 (Fancy Bear), and APT29 (Cozy Bear)—emerged, escalating Russia’s global impact through espionage, sabotage, and influence operations, blending military strategy with advanced cyber tactics.
1.Sandworm (APT44): From early espionage, Sandworm shifted to infrastructure long-term sophistication, while its cloud adaptations—token manipulation, MFA bypass, and device registration—counter modern enterprise security.
2.APT28 (Fancy Bear): Transitioning from military intelligence, APT28 embraced strategic influence, interfering in the 2016 U.S. election, 2017 French campaign, and Ukraine logistics, adapting to geopolitical priorities while retaining GRU tradecraft.
3.APT29 (Cozy Bear): APT29’s 2020 SolarWinds supply chain attack showcased long-term sophistication, while its cloud adaptations—token manipulation, MFA bypass, and device registration—counter modern enterprise security.
Attribution and Operational Patterns
Russian cyber operations can be distinguished by the roles of their primary intelligence services:
• GRU (APT28, APT44): Known for aggressive targeting and integration with military objectives, these groups conduct destructive operations (Ukraine power grid, NotPetya) and maintain persistent access for battlefield advantage.
• SVR (APT29): Specializes in long-term intelligence collection with patient tradecraft, exemplified by the SolarWinds supply chain attack. Its operations prioritize stealth, persistence, and strategic intelligence value over immediate disruption.
• FSB: Focused on domestic control and near-abroad influence, emphasizing information warfare and social manipulation rather than traditional espionage.
Hybrid State–Criminal Ecosystem
A defining feature of the Russian threat landscape is the integration of state and criminal groups, creating a unique hybrid model. Criminal organizations often act as initial access brokers, reconnaissance assets, and cover for sensitive state operations, enabling operational flexibility, plausible deniability, and resource multiplication.
• Resource Sharing: State services provide intelligence, targeting data, and technical tools, while criminal groups contribute revenue streams and operational support.
• Attribution Challenges: Criminal activity obscures state involvement, while state capabilities enhance criminal effectiveness.
• Operational Coordination: Coordinated campaigns across different domains amplify impact, producing compound effects greater than any group alone could achieve.
• Strategic Alignment: Despite operational independence, all actors ultimately advance Russia’s geopolitical and military objectives.

Russian Cyber Threat Outlook: Next 5 Years
• Hybrid Warfare Expansion: Russian cyber operations will increasingly integrate with conventional military campaigns, leveraging AI-enhanced tools, targeting quantum-resistant encryption, and executing coordinated cyber-kinetic attacks.
• Strategic Degradation: Russia will focus on systematically undermining Western democratic institutions and critical infrastructure, aiming to trigger cascading failures in crisis scenarios.
• Dual-Use Threat Model: Destructive capabilities will evolve alongside espionage operations, combining intelligence collection, battlefield support, and strategic deterrence through high-impact cyber attacks.
• State–Criminal Integration: Russia will continue to fuse state and criminal operations, enabling rapid capability growth, revenue generation, plausible deniability, and expanded operational reach aligned with geopolitical objectives.
• Critical Infrastructure Vulnerabilities: Energy, water, transportation, and communications systems will remain key targets, creating escalation-ready risks that will demand sustained defensive investment and international coordination.
Strategies for Mitigating Russian Cyber Risk
Securin outlines mitigation strategies to counter Russian state-sponsored threats, focusing on:
• Strengthening defense and threat management
• Enhancing collaboration and intelligence sharing
• Protecting election security
Together, these measures build resilience against APTs, supply chain attacks, and disinformation.The following table summarizes key risks, mitigation strategies, implementation priorities, and expected impacts to provide a high-level overview.
Risk Category | Mitigation Strategy | Implementation Priority | Expected Impact |
|---|---|---|---|
Destructive Malware | Comprehensive backup systems, network segmentation | Critical | High reduction in recovery time |
Supply Chain Compromise | Vendor security assessment, software integrity verification | High | Significant attack surface reduction |
Credential Theft | Multi-factor authentication, privileged access management | High | Major authentication security improvement |
Social Engineering | Security awareness training, email security enhancement | Medium | Moderate initial access reduction |
Living-off-the-Land | Behavioral analytics, application whitelisting | Medium | Significant evasion technique detection |
Election Interference | Voter system assessments, disinformation monitoring, secure communication channels | Critical | High integrity protection for democratic processes |
Strengthening Defense and Threat Management
Vulnerability Management and Patching
• Prioritize patching vulnerabilities exploited by Russian actors: Microsoft Exchange (e.g., CVE-2021-26855, CVE-2023-23397 via expedited procedures), Atlassian Confluence, Citrix NetScaler (with emergency change management), and Cisco IOS XE (with behavioral anomaly detection for privilege escalation)
• Monitor supply chain attack indicators, focusing on software integrity verification and trusted installer processes
Threat Detection and Monitoring
• Monitor destructive malware indicators such as file system changes, registry modifications, and unusual behavior
• Implement PowerShell logging and behavioral analysis for encoded command detection
• Establish network traffic analysis to detect lateral movement and command-and-control communications
• Develop custom detection rules for Russian threat actor tools (e.g., Cobalt Strike, Mimikatz, living-off-the-land techniques) using behavioral analytics and application whitelisting
• Deploy Active Directory monitoring for unusual authentication and credential access
Incident Response and Recovery
• Establish response procedures for destructive malware and nation-state incidents, emphasizing rapid containment, forensic preservation, and law enforcement coordination
• Implement backup and recovery systems with offline storage and regular restoration testing
• Create communication plans for public disclosure and stakeholder notification during nation-state incidents
Access and Social Engineering Defenses
• Deploy multi-factor authentication and privileged access management
• Implement email security solutions for spearphishing detection and link analysis, paired with security awareness training
• Establish strict network segmentation between IT and OT systems, with attention to industrial control systems and critical infrastructure
Enhancing Collaboration and Intelligence Sharing
• Share threat indicators rapidly with allied intelligence services
• Develop coordinated response procedures for cross-border cyber incidents with clear escalation protocols
• Create diplomatic frameworks for addressing nation-state cyber activities
• Implement joint training programs for nation-state incident response
• Establish threat intelligence sharing focused on Russian state-sponsored activities and hybrid warfare indicators
• Strengthen supply chain security with vendor assessments and trusted relationships
Protecting Election Security
Given Russian threat actors’ persistent focus on election interference, organizations and governments should implement these measures to safeguard democratic processes.
Infrastructure Protection
• Conduct security assessments for voter registration systems, emphasizing database integrity, and enhance infrastructure for voter systems, campaign networks, and media organizations
• Monitor campaign networks for spearphishing and credential theft, leveraging email security solutions (see Access and Social Engineering Defenses)
• Enhance media organization security during election periods to protect information integrity
• Create rapid response capabilities for election incidents, coordinating with federal, state, and local authorities
Information Integrity
• Monitor social media for disinformation campaigns, paired with fact-checking and verification procedures, and develop public communication strategies to address cyber threats while maintaining electoral confidence
• Implement secure communication channels for election officials, emphasizing authentication and integrity
Securin recommends the above measures to help organizations anticipate, withstand, and counter Russian state-sponsored cyber threats while protecting critical systems and democratic institutions.


