
Threat Actors Intelligence Report: Qilin Ransomware
Securin Research Team
Securin Team


Sept 4, 2025
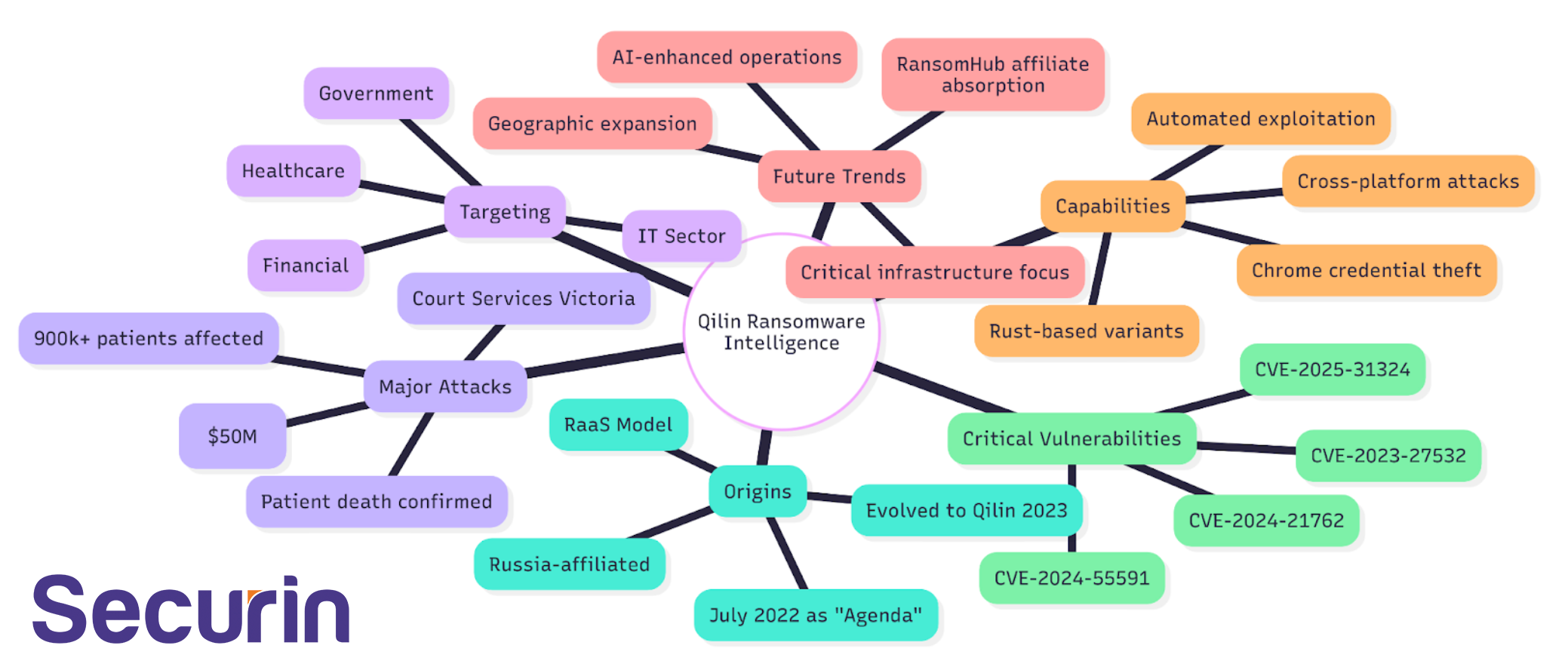
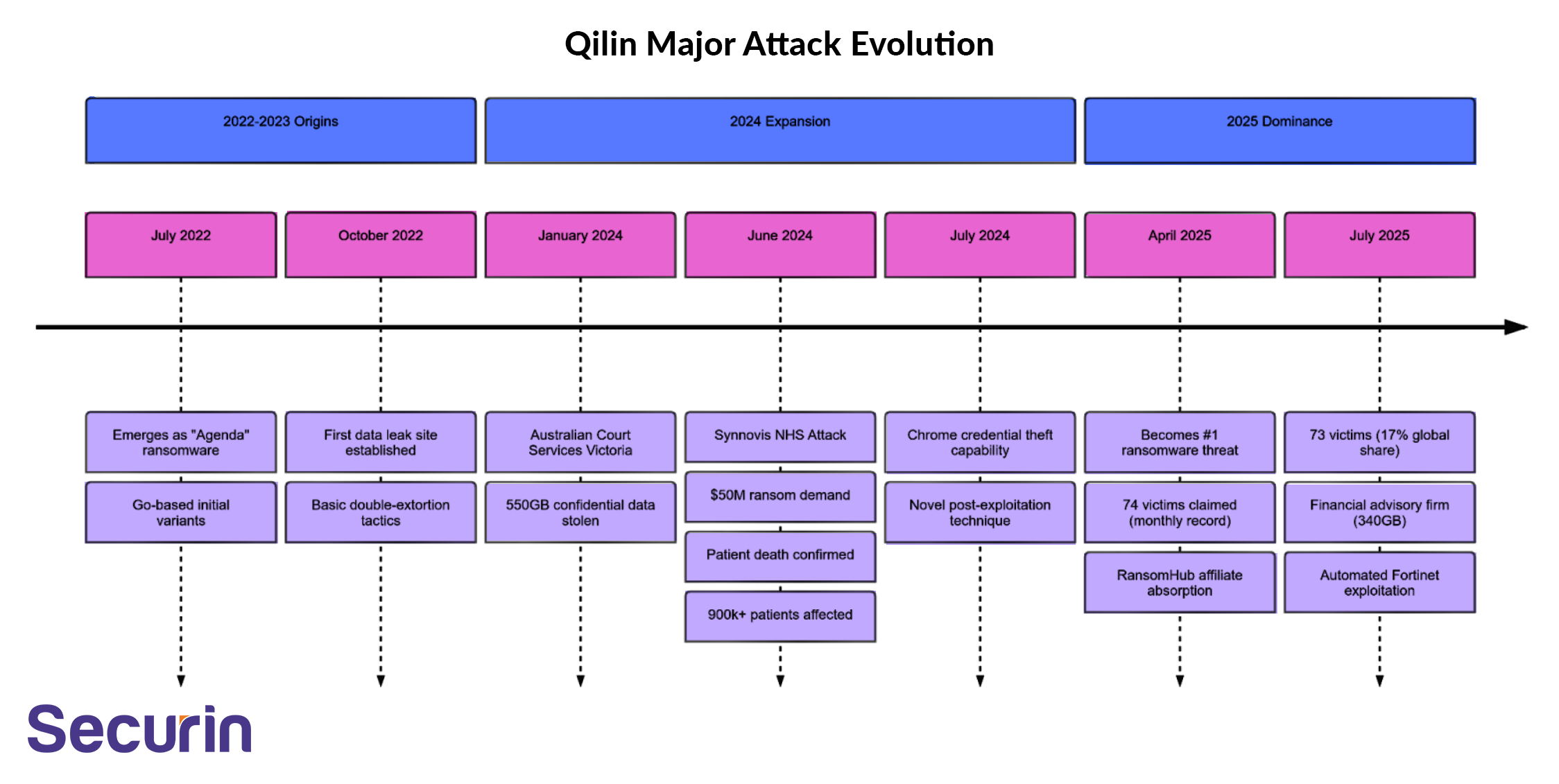
The Qilin ransomware ecosystem represents one of the most significant evolutionary leaps in cybercriminal operations witnessed in recent years. From its origins as the relatively straightforward "Agenda" ransomware in July 2022, the group has transformed into a sophisticated criminal enterprise that now leads global ransomware activity, claiming 73 victims in July 2025 alone—a 17% share of all ransomware attacks globally.
This transformation reflects broader trends in the ransomware economy, where successful groups evolve beyond simple encryption-for-payment models into comprehensive criminal services platforms. Qilin's RaaS architecture, offering affiliates 75-85% profit sharing, has created a magnetic ecosystem that attracted experienced operators following RansomHub's disruption in April 2025. This affiliate migration represents a consolidation of criminal expertise under the Qilin brand, amplifying both their operational capacity and technical sophistication.
Key Findings
• Qilin (also known as Agenda) has emerged as the most active ransomware threat globally in 2025, claiming 73 victims in July 2025 alone
• The group operates a sophisticated Ransomware-as-a-Service (RaaS) model with 75% affiliate profit sharing above $3M ransom payments
• Evolved from Go-based "Agenda" ransomware in 2022 to advanced Rust-based variants with cross-platform capabilities
• Demonstrated escalating operational sophistication with Chrome credential stealing capabilities and AI-enhanced social engineering
Strategic Implications
• Healthcare sector targeting has resulted in confirmed patient deaths, marking a new level of operational impact
• $50 million ransom demand against Synnovis represents one of the highest-value healthcare extortion cases
• Recent Fortinet vulnerability automation suggests systematic vulnerability weaponization capabilities
• Absorption of RansomHub affiliates indicates rapid organizational expansion and capability enhancement
Most concerning is Qilin's willingness to target life-critical infrastructure with full knowledge of potential human consequences. The June 2024 Synnovis attack, which disrupted NHS hospital services and contributed to a patient's death, represents a crossing of ethical boundaries that even many cybercriminal groups historically respected. This willingness to endanger human life for financial gain, combined with their $50 million ransom demand, signals an escalation in ransomware group operational philosophy.
Initial Access Intelligence
Initial Access CVEs
CVE ID | Vendor/Product | Risk Index | Initial Access Technique | Exploitation Complexity |
|---|---|---|---|---|
CVE-2024-55591 | Fortinet FortiOS/FortiProxy | 9.94 | Authentication Bypass via Node.js WebSocket | Low - Automated by Qilin |
CVE-2023-27532 | Veeam Backup & Replication | 9.7 | Credential Extraction from Config DB | Medium - Requires network access |
CVE-2024-21762 | Fortinet FortiOS/FortiProxy | 9.49 | Out-of-bounds Write RCE | Low - Public exploits available |
CVE-2025-31324 | SAP NetWeaver | 9.7 | Unauthenticated Binary Upload | Low - No authentication required |
From an operational perspective, Qilin's systematic automation of Fortinet vulnerability exploitation suggests industrial-scale vulnerability weaponization capabilities. Their ability to rapidly integrate zero-day exploits (CVE-2024-55591) into their affiliate toolkit indicates sophisticated vulnerability research and development capabilities that rival nation-state threat actors.
Initial Access Techniques (MITRE ATT&CK)
Technique ID | Technique Name | Sub-techniques Used | Operational Frequency |
|---|---|---|---|
T1190 | Exploit Public-Facing Application | VPN/Firewall exploitation | High - Primary vector |
T1133 | External Remote Services | SSL-VPN, RDP compromise | High - Persistent access |
T1078 | Valid Accounts | Compromised credentials | Medium - Post-exploitation |
T1566.001 | Spearphishing Attachment | Malicious email attachments | Medium - Targeted campaigns |
T1566.002 | Spearphishing Link | Malicious URL delivery | Medium - Social engineering |
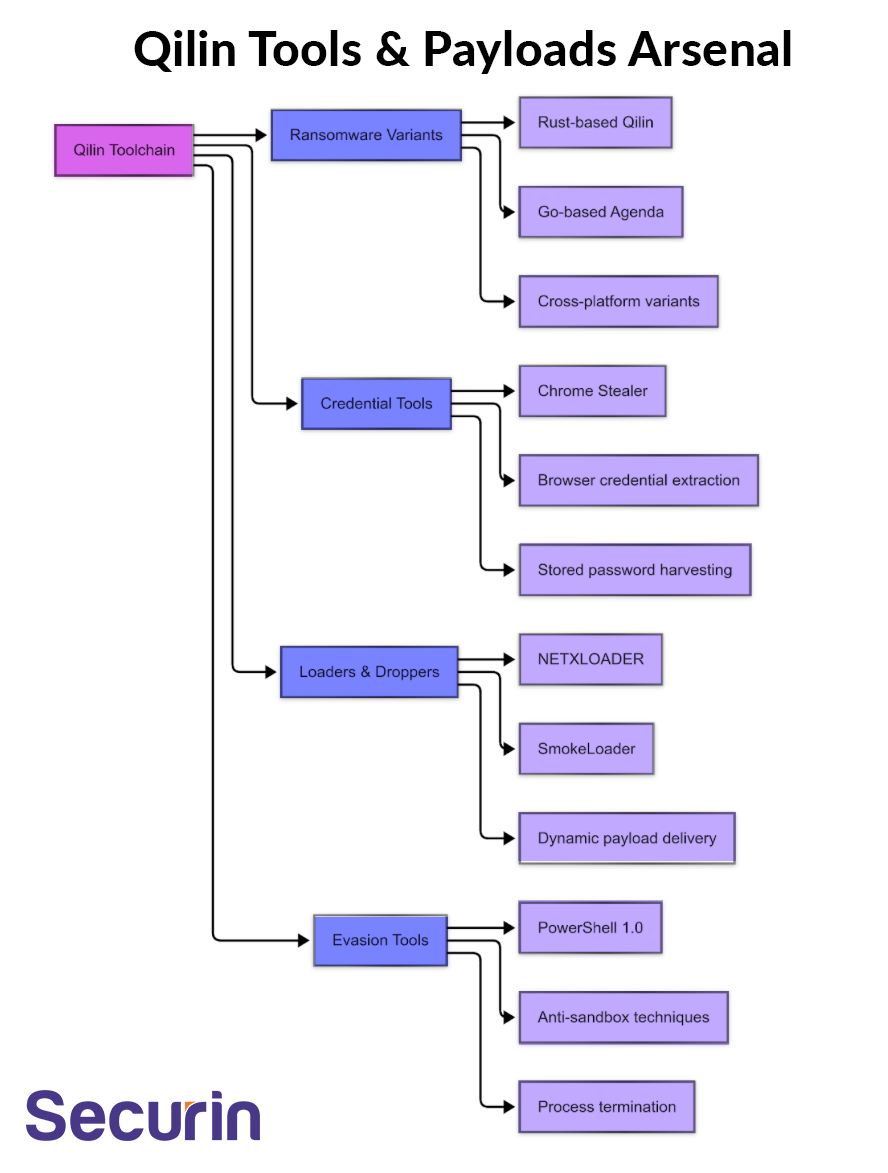
The group's technical evolution tells a story of deliberate capability enhancement. The migration from Go-based ransomware to Rust-based variants demonstrates understanding of modern defensive capabilities and the need for more robust evasion techniques. Rust's memory safety features and cross-platform compilation capabilities make detection and analysis significantly more challenging for security researchers and automated systems.
The recent integration of Chrome credential harvesting capabilities—a technique never previously observed in ransomware operations—demonstrates Qilin's innovative approach to post-exploitation activities. This capability creates cascading risks beyond the initial victim, as stolen credentials can enable attacks against other organizations, potentially creating supply chain compromise scenarios that multiply the impact of single incidents.
Qilin's initial access strategy demonstrates sophisticated understanding of enterprise perimeter security weaknesses. The systematic targeting of Fortinet devices reflects recognition that many organizations operate firewall clusters with mixed software versions, creating vulnerability windows. The automation of Fortinet exploitation through their affiliate panel reduces technical barriers for less sophisticated threat actors, democratizing advanced attack capabilities.
Scanner Coverage Analysis
• Fortinet vulnerabilities show 85% scanner coverage, but many organizations fail to patch SSL-VPN devices promptly
• Veeam backup systems often lack comprehensive scanning due to their critical operational role
• SAP NetWeaver instances frequently operate in isolated environments with limited security tooling
• Qilin specifically targets infrastructure gaps where scanner coverage is incomplete
Data Analysis
Category | Details | Strategic Significance |
|---|---|---|
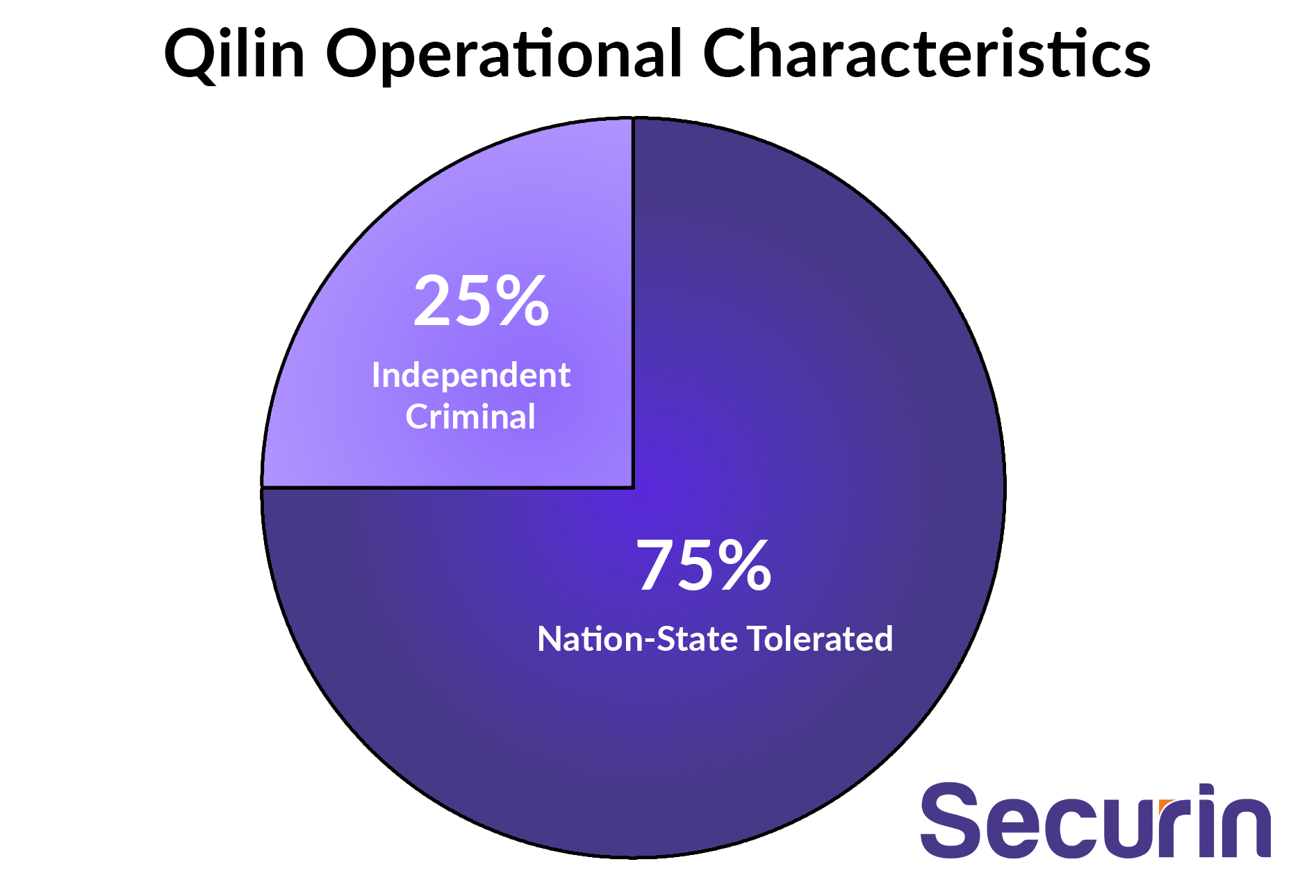
Origin | Russia-affiliated (despite Chinese mythological name) | State-sponsored or state-tolerated operations |
Operation Model | Ransomware-as-a-Service (RaaS) | Scalable, distributed threat ecosystem |
Active Since | July 2022 (as Agenda), evolved to Qilin 2023 | Mature operational framework with 3+ years experience |
Revenue Model | 75% affiliate share (payments <$3M), 85% (>$3M) | Highly attractive profit structure driving affiliate recruitment |
Verified Attacks | 150+ confirmed organizations compromised | Demonstrated high-volume operational capacity |
The Qilin ecosystem represents a sophisticated criminal enterprise leveraging advanced programming languages (Rust, Go) for cross-platform compatibility. Their RaaS model generates substantial revenue through affiliate partnerships, with profit-sharing structures that incentivize high-value target selection. The group's technical evolution from Go-based to Rust-based variants demonstrates continuous capability enhancement and adaptation to defensive countermeasures.
Vulnerability Exploitation Intelligence
CVE ID | Vendor/Product | Risk Index Score | Exploitation Context | Impact Level |
|---|---|---|---|---|
CVE-2024-55591 | Fortinet FortiOS/FortiProxy | 9.94 | Authentication bypass, super-admin privileges | Critical - Zero Day |
CVE-2023-27532 | Veeam Backup & Replication | 9.7 | Encrypted credential extraction | Critical - CISA KEV |
CVE-2025-31324 | SAP NetWeaver | 9.7 | Unauthenticated malicious binary upload | Critical - Zero Day |
CVE-2024-21762 | Fortinet FortiOS/FortiProxy | 9.49 | Out-of-bounds write, RCE | Critical - CISA KEV |
Qilin's vulnerability exploitation strategy focuses on perimeter security infrastructure, particularly VPN concentrators and backup systems. The emphasis on Fortinet vulnerabilities demonstrates systematic reconnaissance and weaponization of network security appliances. Risk Index scores consistently exceed CVSS ratings, indicating real-world exploitation impact. The targeting of backup infrastructure (Veeam) suggests sophisticated understanding of recovery prevention tactics.
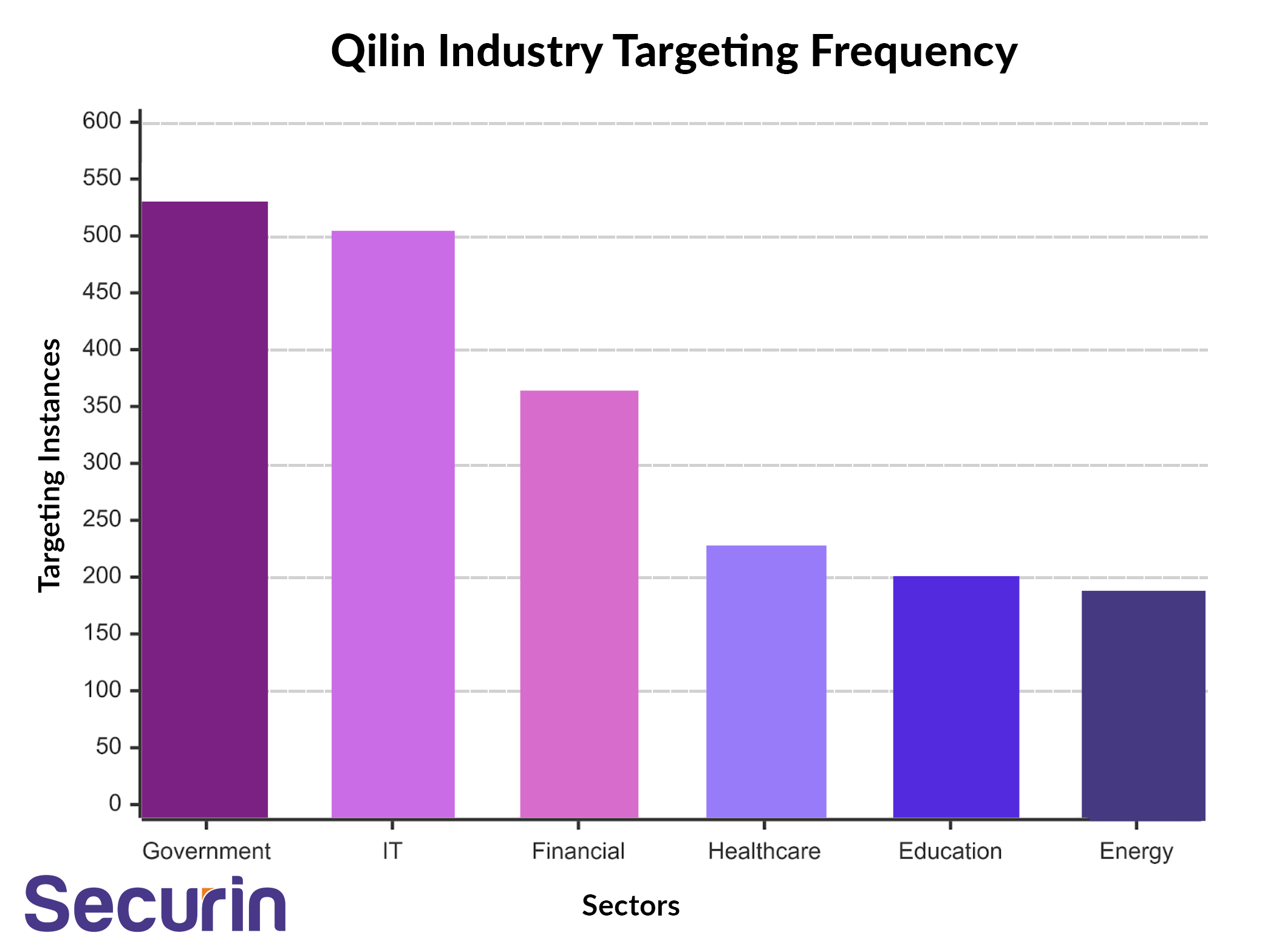
Industry Sector | Targeting Frequency | Strategic Rationale |
|---|---|---|
Government Facilities & Public Sector | High | High-value intelligence and disruption potential |
Information Technology | High | Supply chain access and credential harvesting |
Financial Services | High | High ransom payment capability |
Healthcare & Public Health | Medium | Life-critical services create payment pressure |
Education | Medium | Research IP and credential harvesting opportunities |
Energy | Medium | Critical infrastructure disruption potential |
The targeting pattern reveals sophisticated threat actor reasoning prioritizing sectors with high payment likelihood and maximum disruption potential. Government and IT sector focus suggests espionage capabilities beyond pure financial motivation. Healthcare targeting demonstrates willingness to endanger human life for financial gain, evidenced by the confirmed patient death in the NHS Synnovis attack.
MITRE ATT&CK Techniques Analysis
Technique ID | Technique Name | Tactic Category | Operational Purpose |
|---|---|---|---|
T1190 | Exploit Public-Facing Application | Initial Access | VPN/firewall compromise |
T1133 | External Remote Services | Initial Access, Persistence | VPN/RDP exploitation |
T1078 | Valid Accounts | Multiple Tactics | Credential-based lateral movement |
T1566.001 | Spearphishing Attachment | Initial Access | Social engineering campaigns |
T1566.002 | Spearphishing Link | Initial Access | Malicious link distribution |
Qilin's technique portfolio emphasizes perimeter compromise and credential abuse, consistent with their targeting of remote access infrastructure. The multi-tactic application of valid accounts demonstrates sophisticated post-exploitation capabilities. Integration of spearphishing indicates social engineering competencies alongside technical exploitation.
Tool Category | Primary Tools | Operational Role | Technical Sophistication |
|---|---|---|---|
Ransomware Variants | Qilin, Agenda, Synnovis Ransomware | Encryption and extortion | Rust-based, cross-platform |
Credential Harvesters | Chrome Stealer (novel capability) | Post-exploitation data theft | Browser-integrated extraction |
Loaders | NETXLOADER, SmokeLoader | Payload delivery | .NET obfuscated, anti-analysis |
Lateral Movement | PowerShell 1.0 (deliberately outdated) | Privilege escalation | Evasion through legacy tools |
Targeting Analysis
Major Attack Timeline & Impact
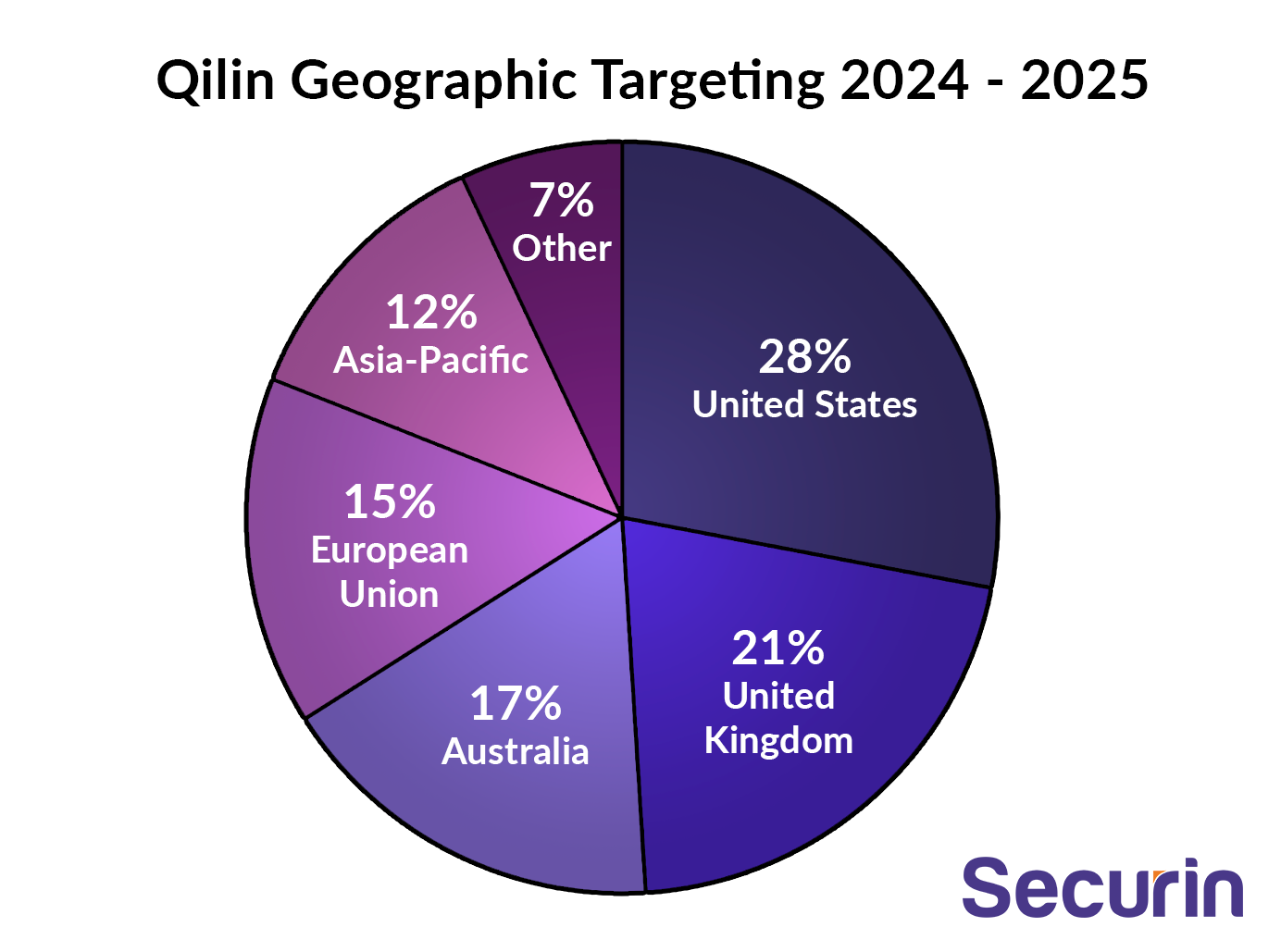
Region | Target Countries | Groups Involved | Strategic Rationale |
|---|---|---|---|
North America | US, Canada | 28 groups | Strategic adversary monitoring, high-value targets |
Europe | UK, Germany, Spain, Netherlands | 24 groups | NATO intelligence, healthcare targeting |
Asia-Pacific | Australia, Singapore, Malaysia | 18 groups | Economic espionage, critical infrastructure |
Other Regions | Various | 12 groups | Opportunistic expansion |
Recent Activity Patterns
Recent intelligence indicates Qilin's operational tempo has dramatically increased since February 2025, with monthly victim disclosures doubling from historical averages. This acceleration coincides with several significant developments:
The absorption of RansomHub affiliates following that group's shutdown in April 2025 provided Qilin with experienced operators and established victim networks. Security researchers observed direct recruitment activities on dark web forums, with Qilin representatives advertising updated toolsets and attractive profit-sharing arrangements to displaced affiliates.
Technical capabilities have expanded beyond traditional ransomware operations to include sophisticated credential harvesting and AI-enhanced social engineering. The integration of NETXLOADER, a heavily obfuscated .NET-based loader protected by .NET Reactor 6, demonstrates investment in custom development capabilities. This loader's just-in-time (JIT) hooking techniques and dynamic payload retrieval create significant challenges for traditional signature-based detection systems.
Geographic expansion patterns show increased targeting of critical infrastructure across multiple continents. Recent attacks in Southeast Asia, targeting countries like Malaysia and Indonesia, suggest operational expansion beyond traditional North American and European focus areas. This geographic diversification may indicate either affiliate-driven expansion or strategic targeting of regions with developing cybersecurity capabilities.
Proactive Analysis
Industry-Specific Implications:
Healthcare organizations face unprecedented risk levels from Qilin operations. The confirmed patient death at King's College Hospital following the Synnovis attack establishes a new precedent where ransomware directly contributes to mortality. Healthcare CISOs must implement crisis management protocols that account for life-critical system dependencies and alternative care delivery mechanisms during cyber incidents.
Financial services organizations represent high-value targets due to both regulatory pressures and customer trust implications. The July 2025 attack on a U.S. financial advisory firm, involving 340GB of client data exfiltration, demonstrates Qilin's capability to execute sophisticated data theft operations beyond encryption. Financial institutions must enhance monitoring for data exfiltration indicators and implement immutable backup strategies.
Government and critical infrastructure entities face strategic targeting due to Qilin's apparent willingness to accept geopolitical risks. The group's government sector focus (527 targeting instances) suggests either state-tolerance or direct coordination with nation-state interests. These organizations require enhanced threat hunting capabilities and incident response plans that account for potential coordinated attacks across multiple agencies.
Risk Mitigation Recommendations
Immediate Actions:
• Prioritize patching of Fortinet vulnerabilities CVE-2024-55591 and CVE-2024-21762, which Qilin has automated for affiliate use
• Implement enhanced monitoring for Chrome browser credential extraction activities, particularly on domain controllers and administrative workstations
• Deploy behavioral detection capabilities targeting PowerShell 1.0 usage, which Qilin affiliates leverage for evasion
Strategic Recommendations
• Develop immutable backup strategies that account for prolonged restoration periods, as Qilin attacks have required weeks to months for full recovery
• Implement crisis communication protocols for double-extortion scenarios, including legal counsel engagement procedures (noting Qilin now offers affiliates legal support services)
• Establish cross-sector threat intelligence sharing arrangements to enable rapid warning dissemination for Qilin TTPs
Advanced Countermeasures
• Deploy deception technologies targeting Qilin's reconnaissance methodologies, particularly credential harvesting and lateral movement techniques
• Implement zero-trust architectures with particular focus on VPN and remote access security, given Qilin's systematic targeting of perimeter infrastructure
• Develop tabletop exercises specifically addressing Qilin's double-extortion and data leak scenarios, including regulatory notification requirements and public relations strategies
Future Threat Projections
Qilin's trajectory indicates continued expansion and sophistication enhancement through 2025 and beyond. Several factors suggest sustained threat evolution:
The successful integration of displaced RansomHub affiliates provides Qilin with experienced operators and established victim networks, likely sustaining high operational tempo through the remainder of 2025. The group's attractive profit-sharing model (75-85% affiliate retention) creates powerful incentives for continued affiliate recruitment and retention.
Technical capability advancement appears focused on evasion and automation. The development of Chrome credential harvesting represents novel post-exploitation techniques that other ransomware groups are likely to adopt. Automated vulnerability exploitation capabilities, currently limited to Fortinet devices, may expand to include other infrastructure vendors, creating systematic supply chain risks.
Geopolitical factors may influence Qilin's strategic targeting decisions. The group's willingness to target critical infrastructure and accept human casualties suggests potential coordination with or tolerance from nation-state actors. This dynamic could lead to politically motivated targeting during international tensions or conflicts.
The healthcare sector faces particular future risk due to Qilin's demonstrated willingness to endanger patients and the sector's critical service dependencies. Future attacks may specifically target hospitals during crisis periods or natural disasters when alternative care options are limited, potentially creating mass casualty scenarios.
Timeline Projections:
• Q4 2025: Continued high operational tempo with potential expansion into new geographic markets
• H1 2026: Integration of AI-powered reconnaissance and social engineering capabilities
• 2026: Potential development of supply chain targeting capabilities leveraging harvested credentials
• Long-term: Possible evolution into politically motivated attacks during international conflicts or crises


