
Threat Actors Intelligence Report: China
Securin Research Team
Securin Team


Nov 6, 2025
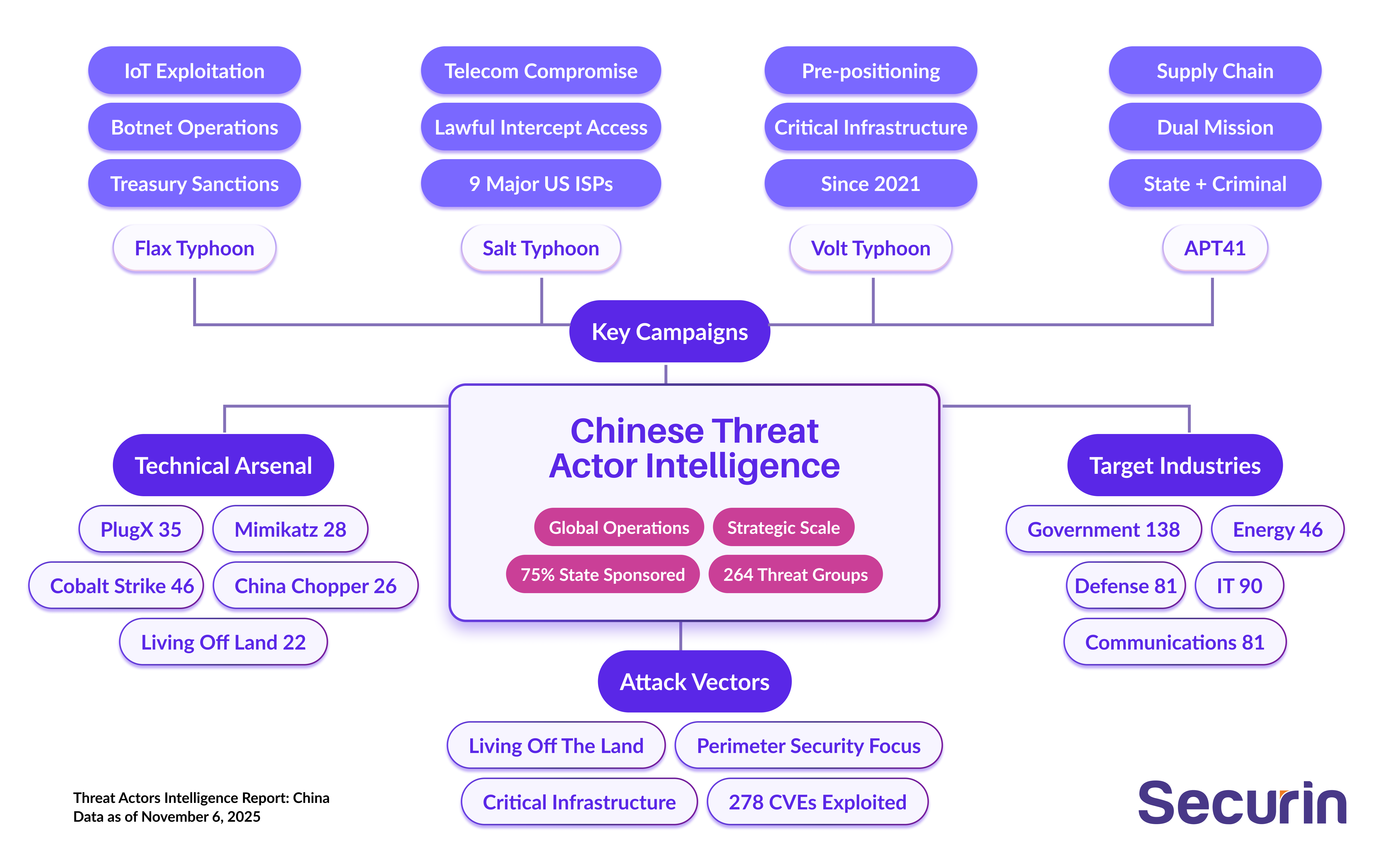
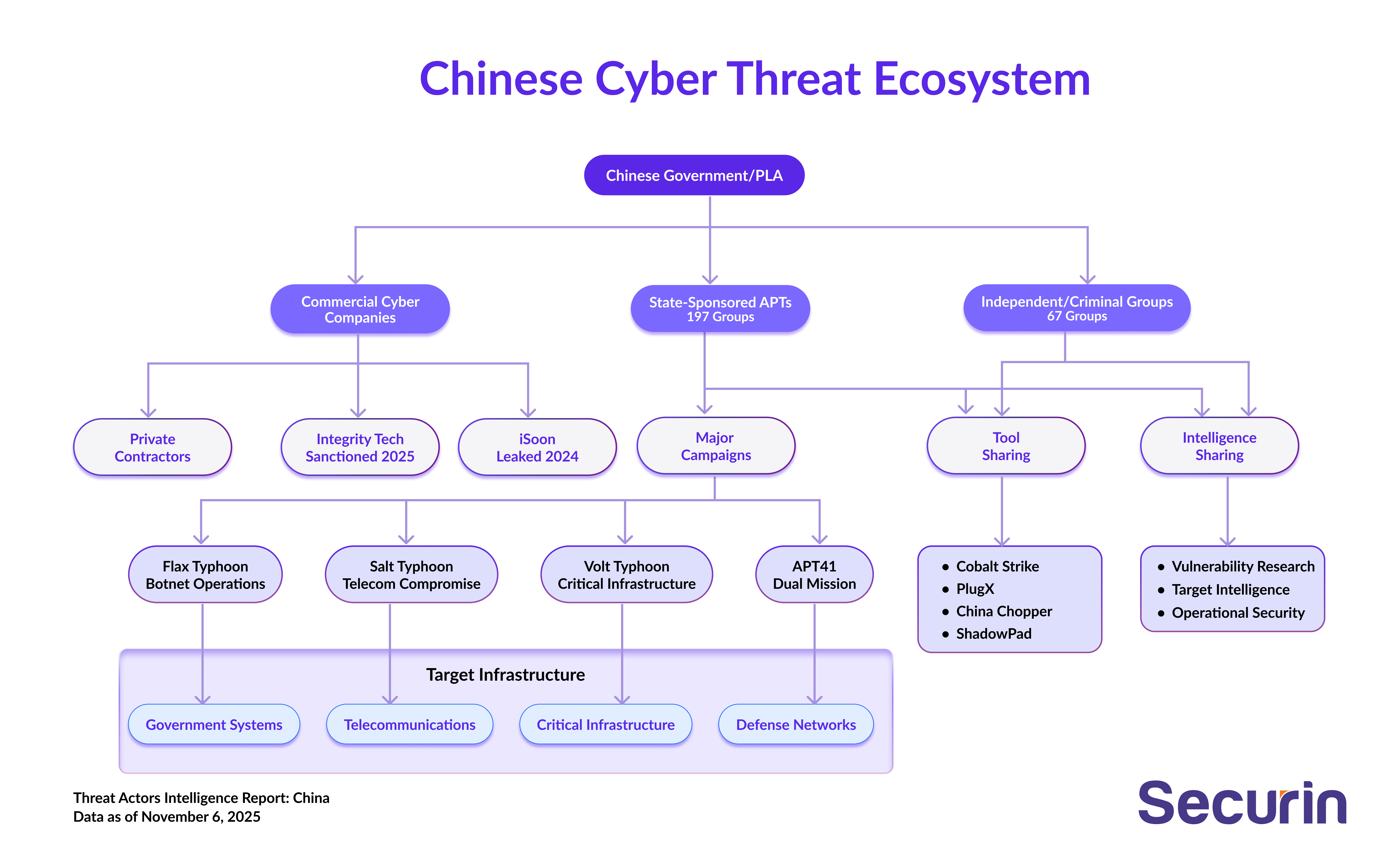
China operates the most expansive and strategically coordinated state cyber ecosystem in the world. With 264 identified groups - 75% of them directly state-sponsored - Beijing has created a distributed-but-synchronized operation spanning espionage, infrastructure compromise and economic warfare. Unlike North Korea’s revenue-first model, China’s campaigns are all about preparing the battleground: embedding into telecoms, government systems and supply chains to create enduring persistence and strategic leverage in any future conflict.
Campaigns like Salt Typhoon, Volt Typhoon and Flax Typhoon reveal a pattern of deep, long-term positioning. Salt Typhoon’s compromise of U.S. lawful intercept platforms saw surveillance systems flipped against their owners, while Volt Typhoon’s persistence inside critical infrastructure since 2021 underlines China’s methodical preparation of “cyber kill switches”. These aren’t one-off instructions, they’re structural footholds: gain silent control over chokepoints, use living-off-the-land to evade controls, and standardize tradecraft so capabilities scale across regions and sectors.
The scale and intent are clear: China is building pre-positioned access across critical systems in 60+ countries, with the USA, Europe and Asia-Pacific in the crosshairs. The posture is less about ‘collect and exfiltrate’, and more about shape and hold, gaining options to disrupt military mobility, emergency response, energy distribution and government communications before a crisis – then exercising that access during it.
As the data distribution below shows, this is state-saturation – a top-heavy system in which almost every operation ladders up to Beijing’s strategic command, leaving minimal space for rogue activity.
What's in This Report
Securin’s analysts mapped the scale and posture of China’s cyber ecosystem: 264 groups, 319 high-impact CVEs exploited, 2,800+ technique implementations, and prioritized targeting of government, communications, defense and critical infrastructure worldwide.
The consequences go beyond single breaches. By embedding in telecoms, government systems and supply chains, China is building structural leverage that can be activated during political tension.
Bottom line: This is pre-war shaping, not opportunistic hacking - and it poses systemic risk to national security and critical services.
Operational Profile: Pre-Positioning at Scale
China optimizes for strategic, quiet persistence over fast payoff. The MO:
- Breach perimeter gateways: VPNs, mail, collaboration tools, Application Delivery Controllers (ADCs) such as Citrix NetScaler ADC, F5 BIG-IP and FortiADC. These widely used vendors have been targeted by Volt Typhoon and APT41.
- Blend with admin behavior to live off the land.
- Masquerade names and locations
- Maintain multi-year dwell across critical operators.
What cyber leaders often miss: This isn’t a thousand different campaigns, it’s a productized access model with common playbooks and tooling. It’s deployed by many teams, against the same strategic surfaces, until coverage looks like a grid. This approach mirrors a military forward deployment, the digital equivalents of bases, fuel lines, listening posts – all waiting for the political signal to act.
Inside the World’s Largest State Cyber Operations
China’s operational ecosystem is vast, disciplined and layered. The below campaigns give insight into the core architecture of its strategy: Moving from traditional espionage to active infrastructure positioning designed to function as coercive leverage in future crises or conflicts.
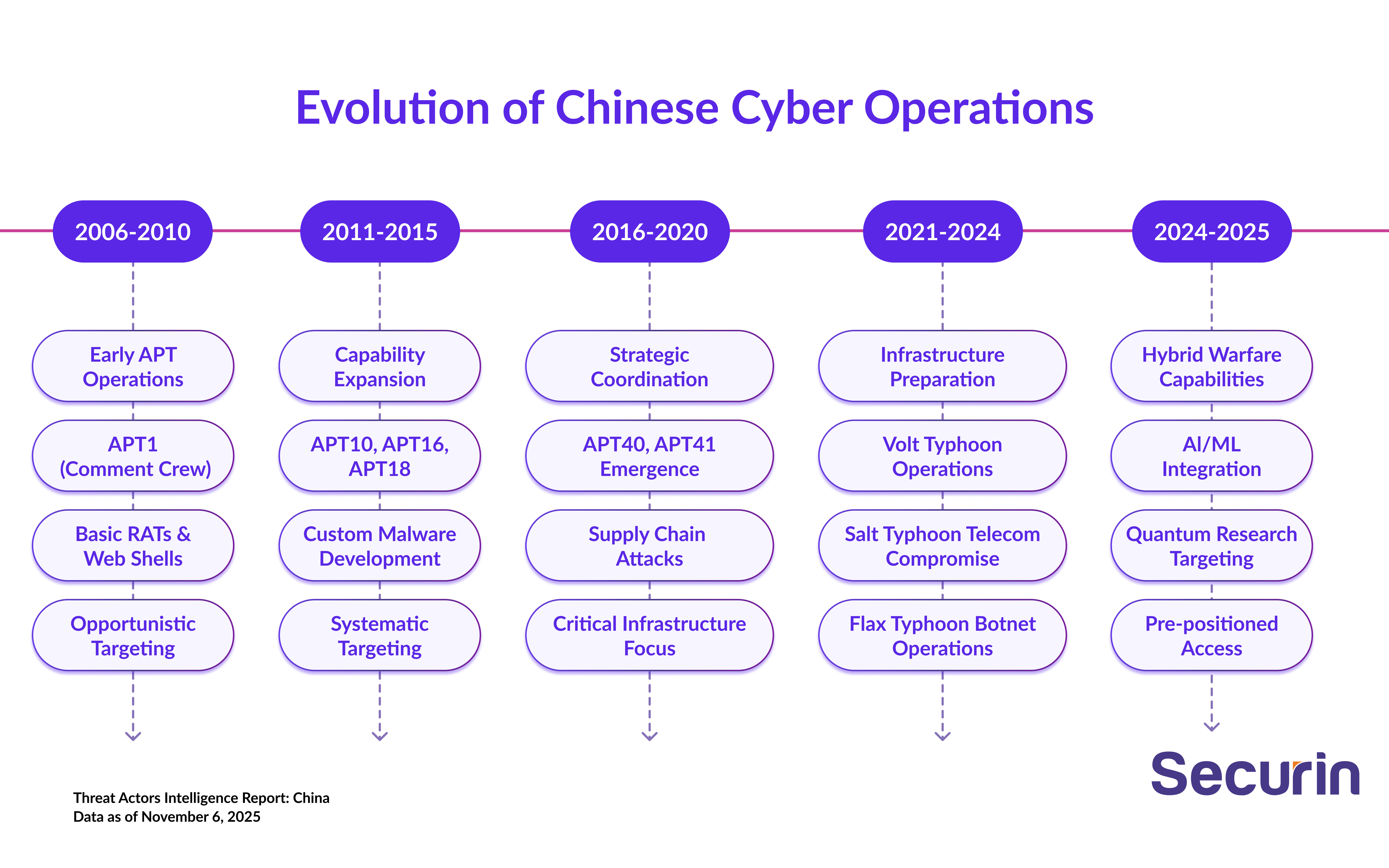
Salt Typhoon compromised lawful-intercept and monitoring systems used by Western law enforcement, effectively weaponizing surveillance frameworks against their operators. The breach exposed how China now targets the very trust layers built for national security, converting oversight into vulnerability.
Volt Typhoon – Persistence Without Payloads
Volt Typhoon’s infiltration of U.S. critical infrastructure—energy, telecom, and transportation—demonstrated a new doctrine: gain access, blend in and wait. By using living-off-the-land techniques, operators achieved multi-year dwell time without triggering alerts, establishing a latent disruption capability across key sectors.
Flax Typhoon – Domestic Networks as Global Launchpads
Flax Typhoon leveraged China Unicom infrastructure to conduct reconnaissance worldwide, disguising state operations as benign commercial traffic. This blurred the boundary between national telecom assets and offensive infrastructure, signaling that civilian systems are now instruments of state power.
APT41 – Dual-Use Operations, Perfected
APT41 bridged espionage, supply chain compromise, and financial theft, proving China’s capacity for toolchain diversification and deniable operations. Its concurrent work for intelligence services and profit underscores the hybridization of state and criminal ecosystems — a model later mirrored by other Chinese clusters.
Bottom line: These four campaigns form a ladder of escalation, from espionage to infrastructure compromise, and on to latent disruption. Between them, they mark a transition from intelligence gathering to building coercive power capability.
Threat Actor Distribution and Capabilities
Securin’s data and analysis underscores China’s institutionalization of cyber operations — a networked state apparatus combining intelligence services, private firms, and proxy collectives. This distributed-but-coordinated approach allows China to scale operations beyond what centralized structures could achieve while maintaining strategic coherence and avoiding single points of failure.
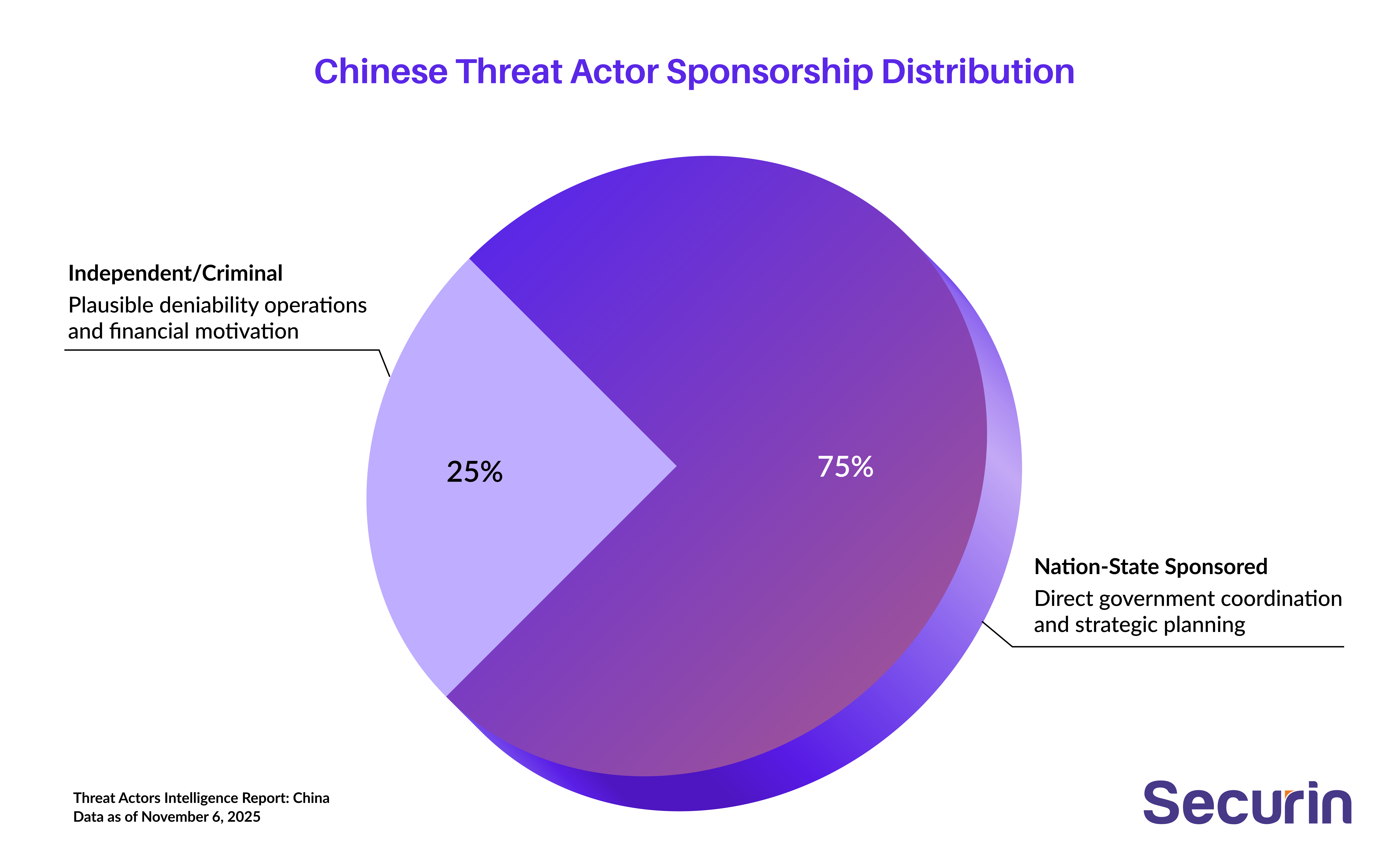
Category | Count | Percentage | Strategic Significance |
|---|---|---|---|
Nation-State Sponsored | 197 | 75% | Direct government coordination and strategic planning |
Independent/Criminal | 67 | 25% | Plausible deniability operations and financial motivation |
Multi-Regional Operations | 230+ | 87% | Global reach and strategic influence |
Critical Infrastructure Focus | 210+ | 80% | Strategic targeting for maximum operational impact |
What it means: The data reveals an unprecedented scale of state-sponsored cyber operations, with three-quarters of Chinese groups operating under direct government coordination. This represents the highest concentration of state-sponsored cyber capabilities globally, indicating centralized strategic planning, resource allocation, and operational
Engineered for Leverage: Top Vulnerabilities Exploited
The vulnerabilities exploited show that China’s cyber operators don’t chase novelty; they chase leverage. They repeatedly target the connective tissue of of global enterprise – collaboration platforms, VPN gateways, email systems – where a single unpatched service can expose hundreds of downstream networks.
Top Vulnerabilities Exploited (by Risk Index Score)
CVE ID | Risk Score | CVSS v3 | Product/Vendor | CISA KEV | Exploitation Impact |
|---|---|---|---|---|---|
CVE-2022-26134 | 9.97 | 9.8 | Atlassian Confluence | ✓ | Remote Code Execution |
CVE-2023-22515 | 9.97 | 10.0 | Atlassian Confluence | ✓ | Privilege Escalation |
CVE-2020-8515 | 9.97 | 9.8 | DrayTek Router | ✓ | Remote Command Execution |
CVE-2021-26855 | 9.91 | 9.1 | Microsoft Exchange | ✓ | Server-Side Request Forgery |
CVE-2021-22893 | 9.91 | 10.0 | Pulse Connect Secure | ✓ | Authentication Bypass |
CVE-2023-3519 | 9.88 | 9.8 | Citrix NetScaler | ✓ | Code Injection |
CVE-2024-21893 | 9.88 | 8.2 | Ivanti Connect Secure | ✓ | Server-Side Request Forgery |
CVE-2023-46805 | 9.85 | 8.2 | Ivanti Connect Secure | ✓ | Authentication Bypass |
CVE-2020-12271 | 9.85 | 9.8 | SQL Injection | ✓ | Remote Code Execution |
CVE-2021-40539 | 9.85 | 9.8 | Zoho ManageEngine | ✓ | Authentication Bypass |
Bottom line: By attacking the tools every organization depends on to connect and collaborate, China’s state-sponsored attackers turn shared infrastructure into shared vulnerability. This is industrialized access management: compromise once, persist everywhere.
Industry Targeting Distribution
The key pattern here is: surround the state, then the suppliers that keep it running. By spanning both command systems and civilian infrastructure, Chinese operators blur the line between intelligence collection and pre-positioning for coercive leverage.

What we see here is coverage saturation: China’s objective isn’t random theft — it’s to own the connective tissue of national resilience: energy, communication, and command systems.
Industry Sector | Groups Targeting | Strategic Rationale |
|---|---|---|
Government Facilities & Public Sector | 138 | Strategic intelligence and policy influence |
Information Technology | 90 | Technology theft and supply chain access |
Communications | 81 | Infrastructure control and surveillance |
Defense | 81 | Military intelligence and operational disruption |
Education | 55 | Academic espionage and intellectual property |
Manufacturing | 51 | Industrial espionage and economic intelligence |
Financial Services | 50 | Economic warfare and financial intelligence |
Energy | 46 | Critical infrastructure targeting |
Transportation & Logistics | 40 | Infrastructure disruption capabilities |
Healthcare & Public Health | 29 | Sensitive data and biological intelligence |
Bottom line: China’s industry targeting is not about isolated gains—it’s about building systemic leverage. Each compromise, from telecom networks to manufacturing IP, contributes to a long-term strategic posture designed to control, not just observe, global infrastructure.
Top Attack Techniques (MITRE ATT&CK)
When it comes to attack techniques, the pattern reveals a shift from malware reliance to identity abuse. Chinese actors now “live off trust” more than code. Their hallmark: activity that looks normal – until it’s too late.
The consequence: defenders looking only for malware noise will miss China. The signal is admin-like behavior, not novel binaries.
China’s chain is: Edge exploit → Identity abuse → LOTL persistence.
Technique ID | Technique Name | Groups Using | Operational Purpose |
|---|---|---|---|
T1190 | Exploit Public-Facing Application | 72 | Initial access through perimeter systems |
T1078 | Valid Accounts | 36 | Persistent access and lateral movement |
T1566.001 | Phishing: Spearphishing Attachment | 32 | Social engineering and credential theft |
T1133 | External Remote Services | 30 | Persistent remote access establishment |
T1105 | Ingress Tool Transfer | 24 | Malware deployment and staging |
T1059.003 | Windows Command Shell | 22 | Living-off-the-land execution |
T1059.001 | PowerShell | 21 | Fileless malware execution |
T1036.005 | Match Legitimate Name/Location | 21 | Defense evasion and persistence |
T1588.002 | Obtain Capabilities: Tool | 21 | Capability development and acquisition |
T1083 | File and Directory Discovery | 20 | Reconnaissance and data discovery |
Bottom line: China’s playbook privileges persistent, covert access over flashy disruption. By combining perimeter exploits with identity abuse and living-off-the-land tradecraft, operators turn normal admin activity into a persistent foothold that is hard to detect and harder to eject.
Top Tools and Payloads
China’s tooling ecosystem reflects industrialized capability development rather than ad hoc selection.
A mix of commercial post-exploitation frameworks and bespoke modular implants allows operators to scale quickly, maintain consistency across campaigns, and obscure attribution through shared toolchains.
Tool/Malware | Groups Using | Primary Function | Sophistication Level |
|---|---|---|---|
Cobalt Strike | 46 | Command & Control, Post-Exploitation | Advanced |
PlugX | 35 | Remote Access Trojan | Advanced |
Mimikatz | 28 | Credential Harvesting | Advanced |
Gh0st RAT | 26 | Remote Access Trojan | Advanced |
China Chopper | 26 | Web Shell, Persistence | Intermediate |
Living Off The Land | 22 | Defense Evasion | Advanced |
PsExec | 19 | Lateral Movement | Intermediate |
Poison Ivy | 16 | Remote Access Trojan | Intermediate |
Impacket | 16 | Network Protocol Exploitation | Advanced |
ShadowPad | 15 | Modular Backdoor | Advanced |
Bottom line: The tool selection reflects a sophisticated understanding of enterprise environments and defense capabilities. The widespread use of Cobalt Strike indicates professionalization of operations, while the prevalence of living-off-the-land techniques demonstrates advanced operational security awareness. The combination of custom malware (PlugX, Gh0st RAT) with commercial tools (Cobalt Strike) shows operational flexibility and resource availability.
Top Vendors Targeted
China’s vendor targeting shows a clear hierarchy of leverage. Rather than chase volume, operators pursue the vendors that anchor enterprise and government ecosystems.

Each compromise becomes a multiplier, offering access not just to one target, but to every organization built on that vendor’s stack.
Vendor | Strategic Significance |
|---|---|
Google | Browser and cloud infrastructure compromise |
Microsoft | Enterprise and government system targeting |
Cisco | Network infrastructure and routing systems |
Atlassian | Enterprise collaboration and development tools |
F5 | Application delivery and security appliances |
RedHat | Enterprise Linux and open-source infrastructure |
Adobe | Content creation and document systems |
Oracle | Database and enterprise application systems |
Ivanti | IT service management and security |
Fortinet | Network security and firewall systems |
Bottom line:The vendor targeting pattern demonstrates strategic focus on critical infrastructure and enterprise technology providers. The disproportionate targeting of Google reflects the global ubiquity of Chrome and cloud services, while Microsoft targeting aligns with enterprise and government system prevalence. Network infrastructure vendors (Cisco, F5, Fortinet) represent strategic chokepoints for communications and security systems.
Top Targeted Weaknesses
China’s exploitation pattern centers on precision, not breadth. By repeatedly targeting a narrow set of code execution and authentication flaws, operators turn common software weaknesses into predictable, scalable control paths across global systems.
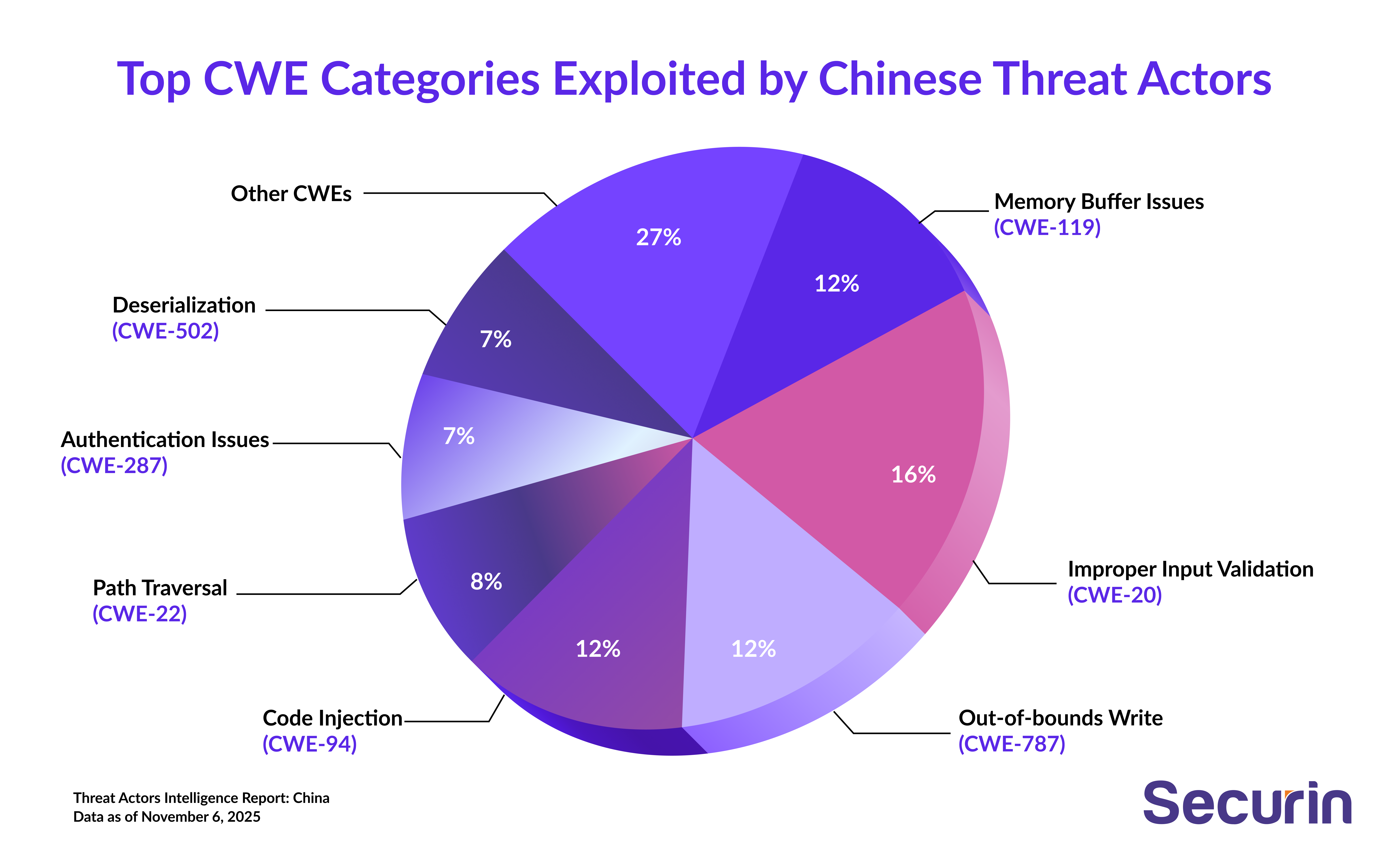
CWE clustering shows a two-tier strategy: exploit code executing for entry, followed by authentication weaknesses for control. China isn’t chasing variety – it’s building repeatable dominance.
CWE ID | Weakness Name | Vulnerability Count | Exploitation Impact |
|---|---|---|---|
CWE-20 | Improper Input Validation | 98 | Remote code execution, data manipulation |
CWE-94 | Code Injection | 70 | Arbitrary code execution |
CWE-787 | Out-of-bounds Write | 70 | Memory corruption, system compromise |
CWE-119 | Memory Buffer Boundary | 69 | Buffer overflow, privilege escalation |
CWE-22 | Path Traversal | 50 | Unauthorized file access |
CWE-287 | Improper Authentication | 43 | Authentication bypass |
CWE-502 | Deserialization of Untrusted Data | 41 | Remote code execution |
CWE-78 | OS Command Injection | 36 | System command execution |
CWE-121 | Stack-based Buffer Overflow | 29 | Memory corruption, code execution |
CWE-77 | Command Injection | 28 | Arbitrary command execution |
Bottom line: The weakness targeting pattern reveals sophisticated understanding of fundamental software vulnerabilities. The focus on input validation and injection flaws demonstrates systematic exploitation of common programming errors, while memory corruption vulnerabilities indicate capability to exploit complex system-level flaws. This pattern suggests both automated vulnerability scanning capabilities and manual exploitation expertise.
Scanner Coverage Analysis
Commercial scanners deliver a strong baseline for known vulnerabilities. But percentage figures hide critical blind spots—newly disclosed CVEs, unmanaged assets and shadow IT—that adversaries deliberately exploit as primary ingress points.
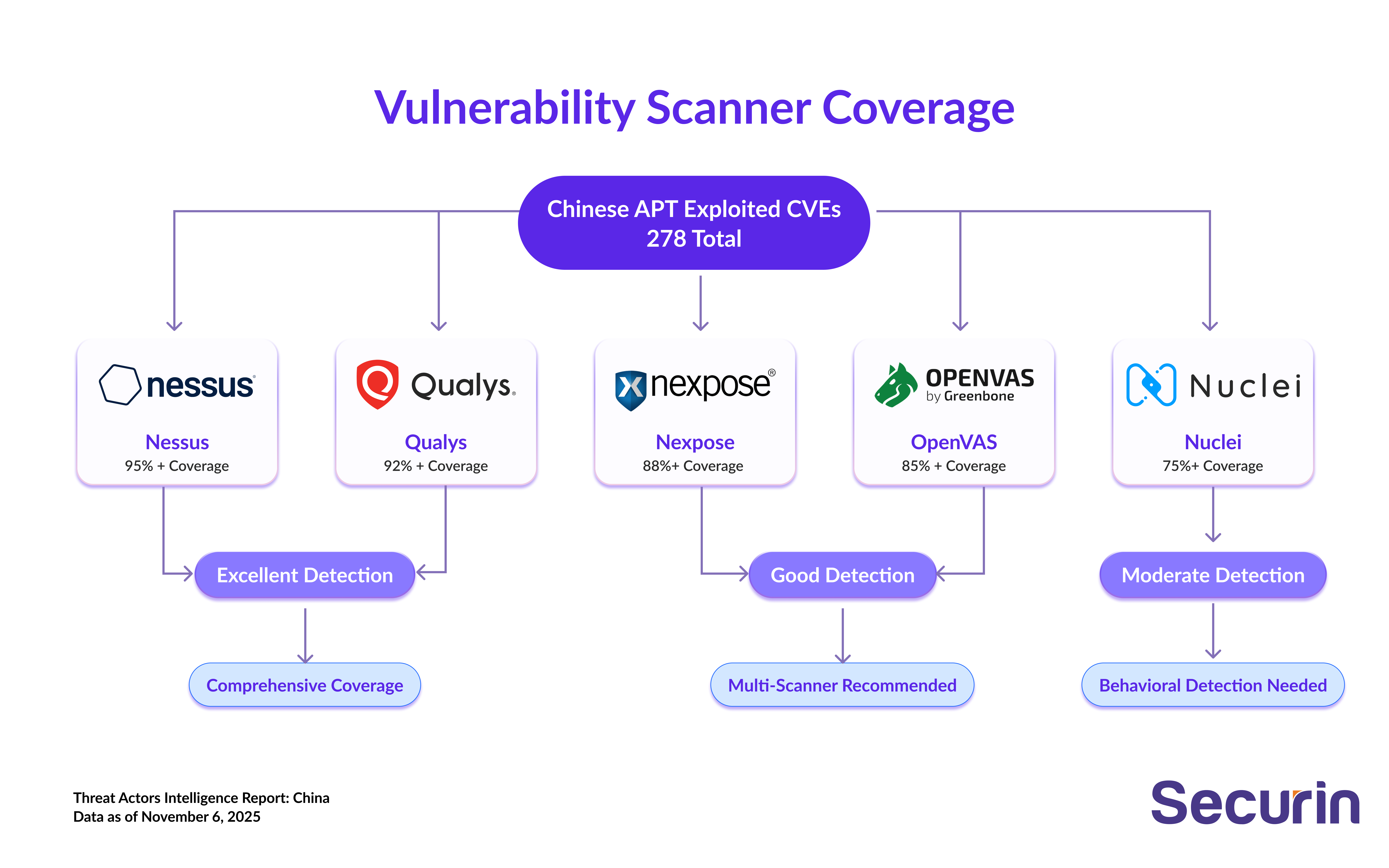
Scanner Provider | Coverage Distribution | Effectiveness Rating |
|---|---|---|
Nessus | 95%+ coverage | Excellent detection capability |
Qualys | 92%+ coverage | Excellent detection capability |
Nexpose | 88%+ coverage | Good detection capability |
OpenVAS | 85%+ coverage | Good detection capability |
Nuclei | 75%+ coverage | Moderate detection capability |
Bottom line: : Approximately 5-15% of exploited vulnerabilities may lack comprehensive scanner coverage, particularly for zero-day and recently disclosed vulnerabilities. Organizations should implement multi-scanner approaches and behavioral detection to address coverage gaps.
Risk Mitigation Recommendations
China’s campaigns exploit speed, scale, and persistence - and defense must do the same. Securin’s analysts recommend focusing on tightening the patch-to-detection window, hardening the trust layer, and aligning long-term architecture to withstand sustained state-level intrusion.
Some immediate and strategic actions:
Immediate Actions:
• Prioritize patching of vulnerabilities most frequently exploited by Chinese actors, particularly Atlassian Confluence, Microsoft Exchange, and Ivanti Connect Secure systems
• Implement enhanced monitoring for living-off-the-land techniques and legitimate tool abuse, focusing on PowerShell, WMI, and command-line utility execution
• Deploy behavioral analytics and anomaly detection capabilities specifically tuned for Chinese threat actor TTPs and tool usage patterns
• Establish strict network segmentation between IT and OT systems, with particular focus on critical infrastructure environments
Strategic Recommendations:
• Implement comprehensive zero-trust architectures with emphasis on continuous verification and least-privilege access principles
• Enhance threat intelligence sharing frameworks specifically focused on Chinese state-sponsored activities and infrastructure targeting
• Develop incident response capabilities specifically designed for advanced persistent threat scenarios and long-term compromise situations
• Establish supply chain security programs with specific focus on software development environments and third-party dependencies
China’s threat posture isn’t episodic—it’s structural. Defensive maturity now depends on treating infrastructure as contested terrain, where patch velocity, verification, and visibility determine resilience far more than any single product or control.
Future Strategic Threat Projections
China’s cyber trajectory points toward full-spectrum capability – where AI, quantum, and hybrid operations converge to give strategic, not just tactical, advantage. The next phase is less about intrusion than activation.
• AI/ML integration → autonomous recon, faster spearphishing, smarter exploits.
• Quantum resistance → encryption testing and cryptographic manipulation.
• Cloud control-plane targeting → new priority for 2026–27.
• Activation risk → latent access in telecom, energy, and logistics systems now at “ready” status.
• Hybridization → deeper convergence between state units and private firms for speed and deniability.
China’s next cyber frontier will not be measured in data stolen, but in systems quietly controlled. As AI, quantum-resistant encryption, and automated exploitation enter the operational mainstream, Chinese threat actors are engineering a future where intrusion is instantaneous and persistence is long-standing. This marks a decisive evolution from surveillance to control, an architecture of access designed to be activated when geopolitical tensions demand it.
What makes this ecosystem formidable is its hybridity. The fusion of state, commercial and criminal resources enables continuous innovation, rapid scaling and built-in deniability. It’s not a campaign, but an operational system, optimized for endurance. From a defense perspective, it’s no longer about containment after compromise, but resilience before it. It’s time to treat digital infrastructure as strategic terrain, not simply technical infrastructure.


