
Enrichment Was the Smaller Gap: How Securin Closed Both Halves of the NVD Problem
Securin Research Team
Securin Team


May 8, 2026
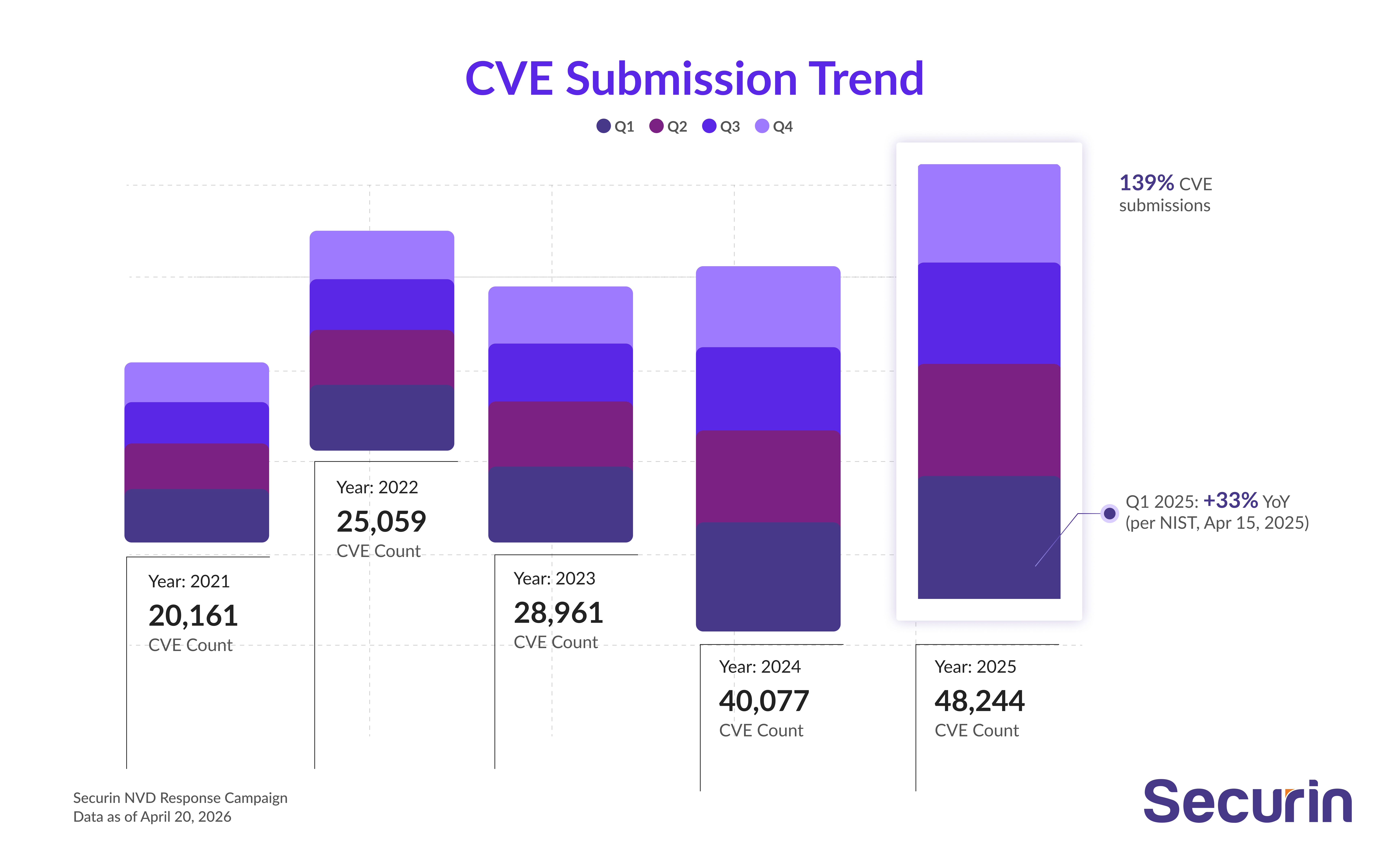
NIST's April 15 announcement formalizes a data gap we've been tracking since 2024. Here's what 448,484 CVEs - 43,374 of them weaponized - taught us about what defenders actually need.
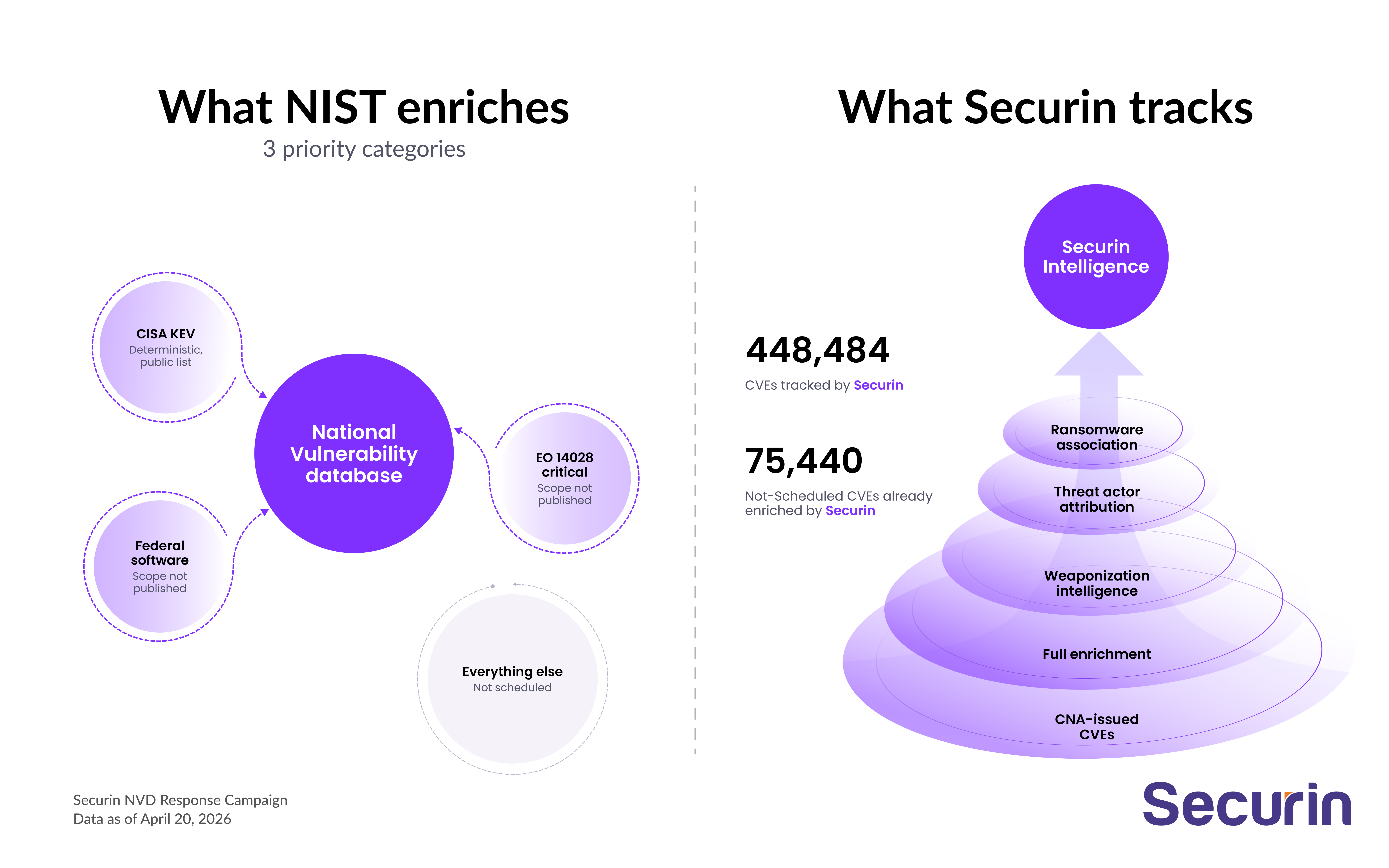
On April 15, 2026, the National Institute of Standards and Technology (NIST) announced that the National Vulnerability Database (NVD) will move to a risk-based enrichment model. NIST will prioritize three categories: Common Vulnerabilities and Exposures (CVEs) in the Cybersecurity and Infrastructure Security Agency's (CISA) Known Exploited Vulnerabilities (KEV) catalog, CVEs affecting software used by the federal government, and CVEs tied to critical software defined under Executive Order 14028. Everything else will be published but flagged as "Not Scheduled."
This is being treated as breaking news. It shouldn't be. With funding reductions forcing triage, NVD's priority was never going to be enrichment. The pipeline began reflecting that reality in early 2024, and the backlog has been visible to anyone paying attention for over two years. What April 15 changed is not the state of the data. It's the state of the conversation. Every security leader in America now has board-level awareness of a gap that the industry has been quietly routing around since 2024.
We want to share what we've learned during those two years, and why we think the current framing of this problem misses the point.
Enrichment was the smaller gap. Exploitation intelligence was the bigger one. We closed both.
The industry has been optimizing the wrong layer of the problem.
Enrichment is metadata. Common Platform Enumeration (CPE) strings, Common Weakness Enumeration (CWE) classifications, Common Vulnerability Scoring System (CVSS) scores. Useful, necessary, but fundamentally descriptive and non-contextual. It tells you what a vulnerability is, not what it means for your environment.
Exploitation intelligence is different. It tells you whether a working exploit exists. Whether it's being used in the wild. Which threat actors are using it. Which ransomware families have adopted it. How long you have before your environment becomes a target.
NIST was never in the exploitation intelligence business. Neither were most enrichment providers. And the enrichment NIST was in the business of — CWEs, affected products, adversary mapping — has been eroding for years, regardless of what the April 15 announcement says about it now. Defenders need both halves: the descriptive one and the predictive one. We'll come back to what we've done on each.
What we've seen tracking the full vulnerability lifecycle
As a CVE Numbering Authority (CNA) operating an in-house vulnerability research and red team program, Securin has been producing exploitation intelligence at the source for years. Before sharing the data, one distinction is worth making explicit because it shapes everything that follows.
Securin differentiates between vulnerabilities that are weaponized, meaning a working exploit exists, and those that are exploited in the wild, meaning observed in active attacks. These are not interchangeable. A weaponized CVE is a loaded weapon; an in-the-wild CVE is one already being fired. Of the 448,484 CVEs we track, 43,374 are weaponized. Of those, 4,303 have been confirmed as exploited in active attacks. The numbers serve different decisions, and conflating them understates the precision defenders actually have access to.
Here's what our data shows across three dimensions:
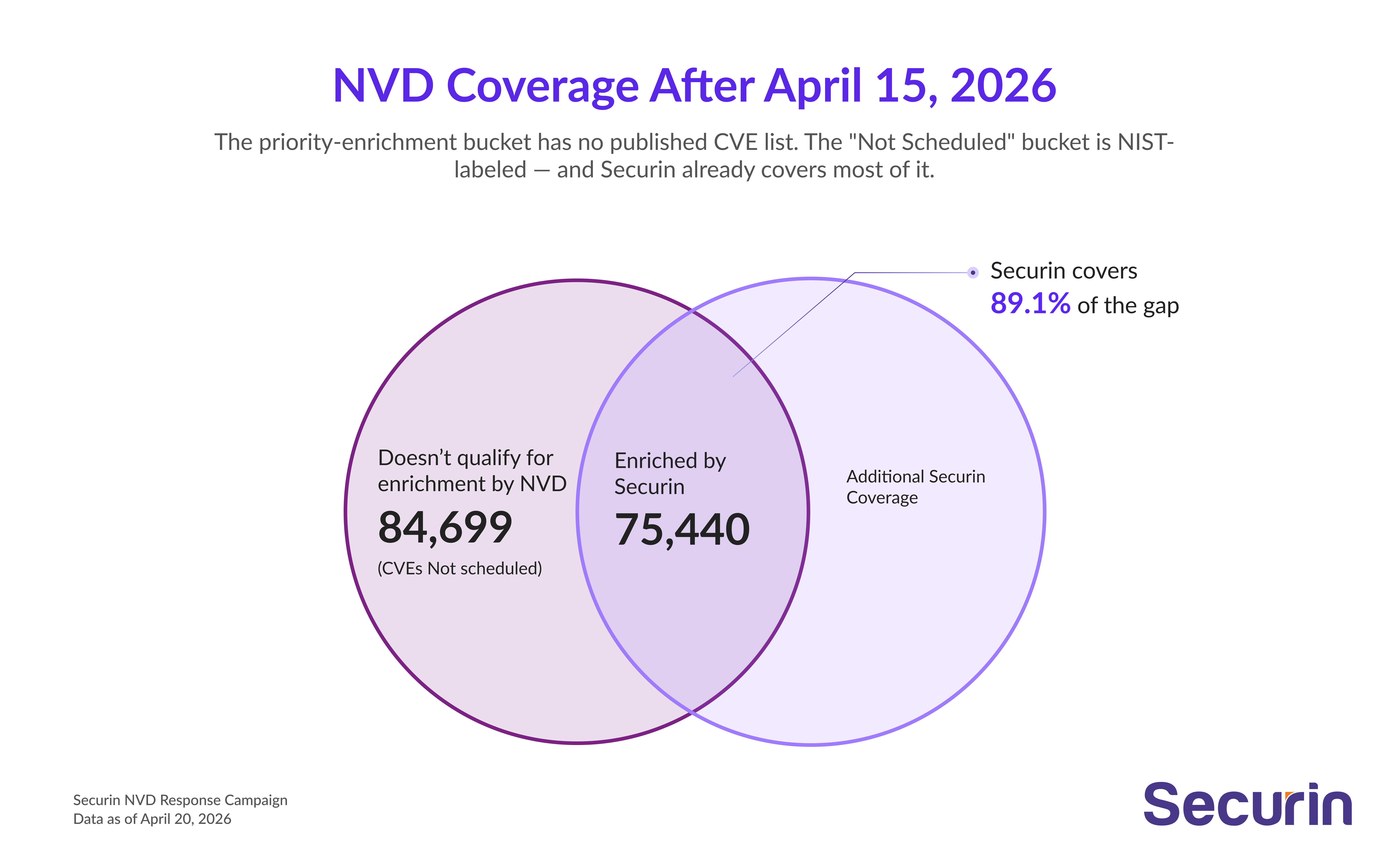
Coverage. Securin currently tracks 448,484 CVEs, including 84,699 CVEs that now fall outside NIST's three priority categories and will no longer receive NVD enrichment. Of those, 2,458 CVEs impact operational technology and industrial control systems (OT/ICS) that do not hit the new priority lanes. What NIST has not published is which future CVEs will land in that bucket. The federal-software and EO-14028 "critical software" categories are defined by policy, not by a CVE list, meaning defenders cannot audit or predict what will fall into scope. Six months out, you're planning against a definition you can't validate.
Timeliness. Our mean time from public disclosure to weaponization determination is 82 days. Across the trailing 12 months, Securin flagged in-the-wild exploitation an average of 3.5 days before the associated CVE appeared in the CISA KEV catalog. That gap is the difference between fixing what matters and reacting to what's already happened.
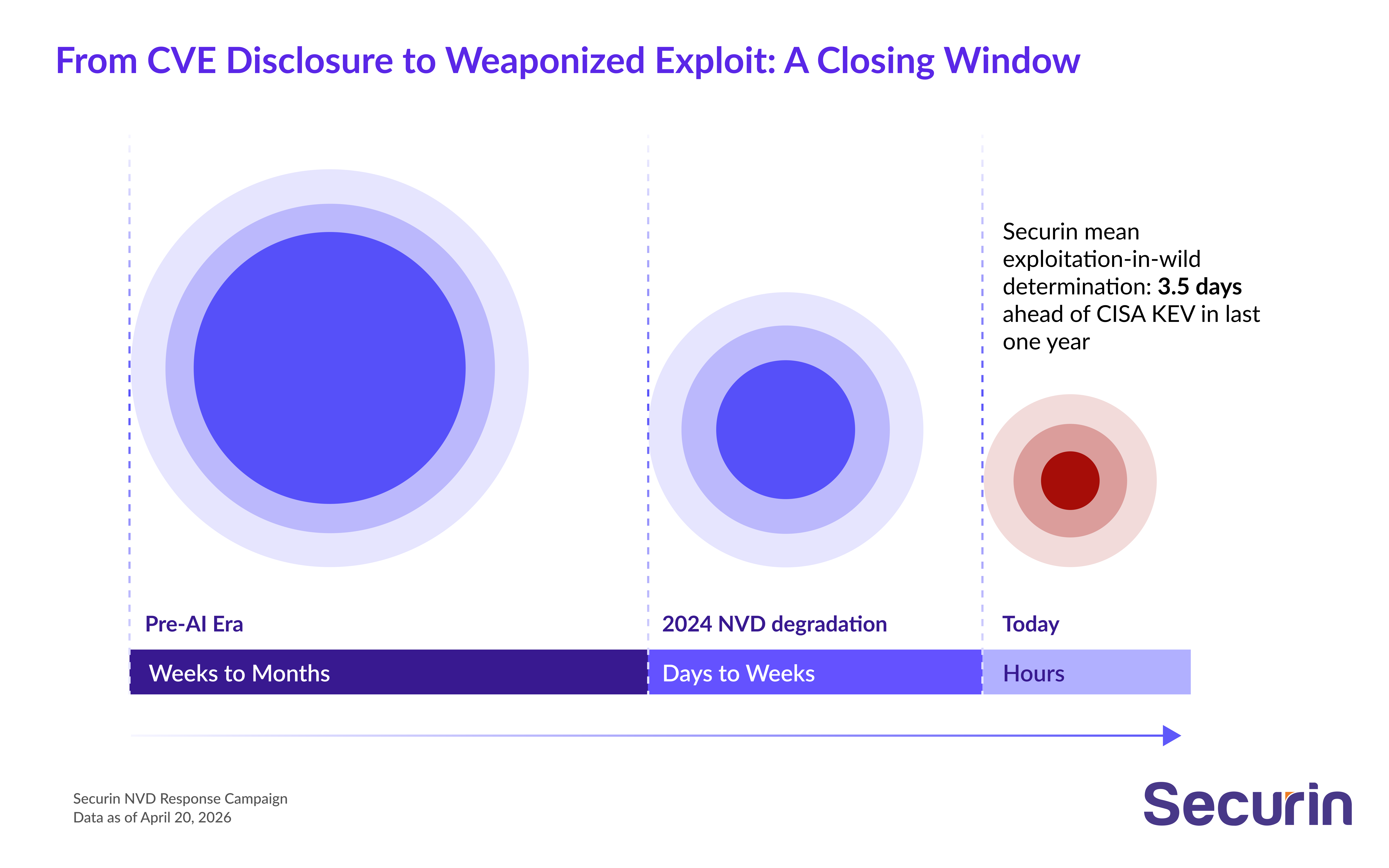
Frontier AI models have collapsed the time from CVE disclosure to weaponized exploit from weeks to hours. Nation-state actors are combining human expertise, custom tooling, and AI-driven reconnaissance against critical infrastructure. In this environment, "do I have enrichment data" and "do I have exposure intelligence fast enough to matter" aren't alternative questions. They're the same question, asked at two different layers. Defenders need both answers, and they need them faster than NIST's prioritization model is built to deliver.
Weaponization. Of the 4,303 CVEs Securin has flagged as exploited in the wild, 2,730 (roughly 63%) are not currently in the CISA KEV catalog. 406 CVEs have confirmed nation-state attribution across 209 distinct threat actor groups, including APT28, Equation Group, Kimsuky, Winnti Group, and OilRig, all actively targeting US public and private infrastructure. 433 CVEs are associated with active ransomware campaigns.
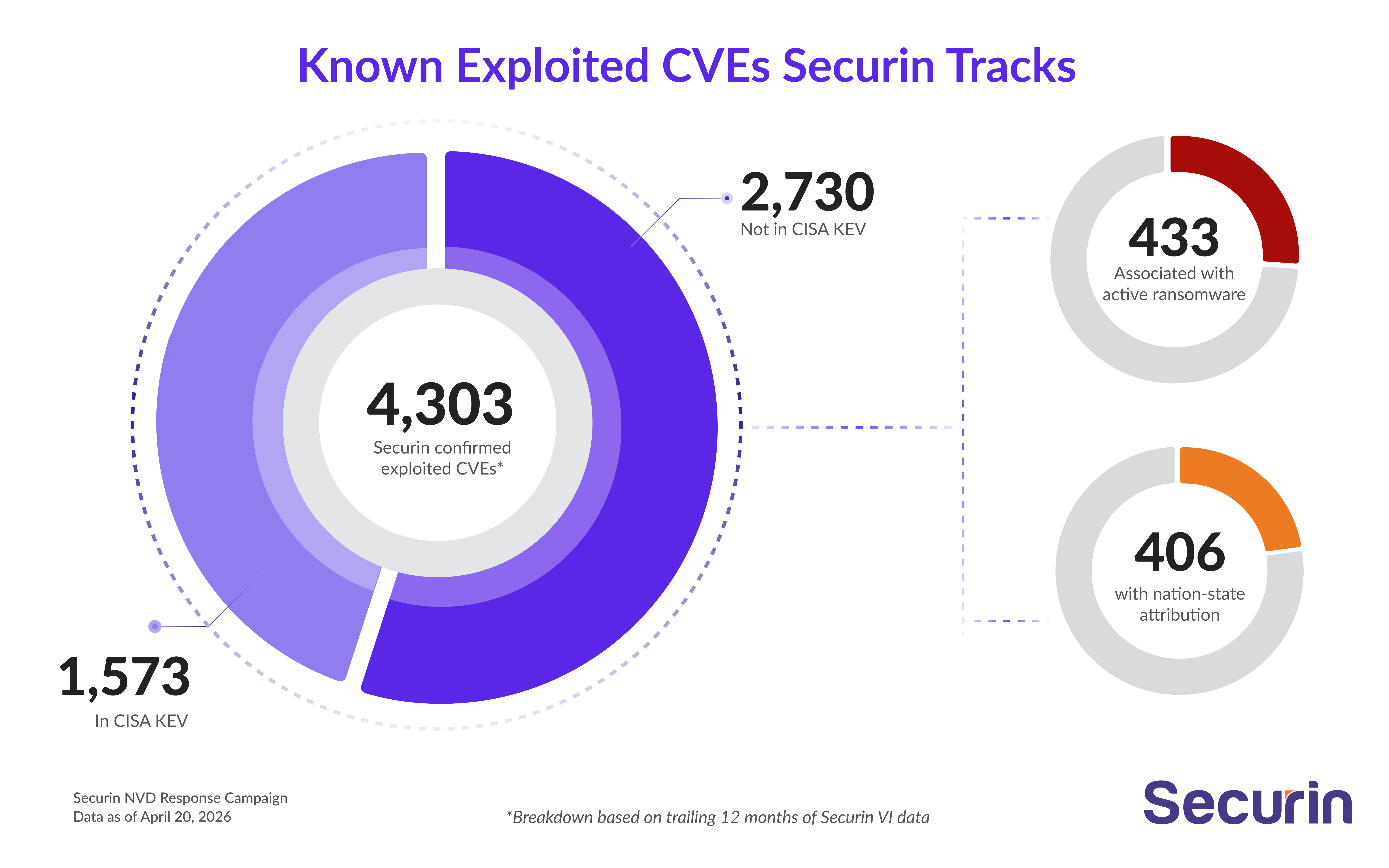
The most consequential overlap in our dataset sits at the intersection of two lists: CVEs adversaries are actively weaponizing, and CVEs NIST has deprioritized for enrichment. That number is 10,605. These are not hypothetical risks or theoretical exposures. They are vulnerabilities with working exploits, being used by threat actors right now, that defenders cannot rely on the NVD to characterize, score, or contextualize. This is the gap the April 15 announcement does not fully reckon with.

We didn’t wait for NIST on enrichment either
Exploitation intelligence is the gap that decides whether you patch tonight. But the descriptive layer underneath it has been quietly eroding for years too. Many CVEs ship without a CWE classification. Affected-product strings arrive late, partial, or not at all. The threat-actor mapping defenders actually need was never there to begin with. We rebuilt all three.
Every CVE we track gets a defined weakness. A CWE classification is the difference between "something's broken" and "here's the class of bug your engineers need to look for." Half the catalog doesn't come with one. Securin classifies every CVE we track, and when sources disagree we resolve it down the CWE tree to the most specific weakness that fits, not the generic parent. Defenders get a real category, not a placeholder.
Affected products, sourced from the people who actually know. A CPE string is a downstream lookup. The upstream truth lives with the CNAs, the vendors, and the third-party advisories shipping the patch. We pull from there. The result is the canonical "what's affected" signal CPE was always meant to represent, populated whether the NVD ever publishes it or not.
Adversary techniques, mapped per CVE. Knowing a vulnerability exists is one thing. Knowing how an adversary will use it is another. Securin maps MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) techniques to vulnerabilities the way an analyst would, with agentic AI reading the weakness, the exploit path, and the impact, and corroborating against the actors and campaigns we already track. Defenders get a per-CVE tactics, techniques, and procedures (TTP) profile that drops straight into detection content.
None of this replaces exploitation intelligence. It's the floor underneath it.
Why this matters more now, not less
There is a tendency in moments like this to treat the NIST announcement as a problem to be solved with more data feeds. It isn't. The average enterprise vulnerability management program is tracking well over a million findings at any given time. When you account for instances across assets, hosts, and environments, a single CVE can generate hundreds of exposures. Defenders working through millions of findings don't need another spreadsheet. They need to know which fraction of those findings represent actual exploitable risk, and which of those are being actively exploited by adversaries already moving faster than quarterly patch cycles.
More data without more signal is just more noise. The defenders who will be best positioned six months from now are not the ones who found a replacement enrichment feed. They're the ones who already know which of those 10,605 weaponized, un-enriched CVEs are in their environment today.

Where we go from here
Securin is committed to expanding our coverage, improving our timeliness, and sharing our findings. Over the coming weeks we'll publish a methodology document on how our vulnerability intelligence pipeline tracks, enriches, and validates weaponization, and a threat actor landscape report covering the 209 groups actively exploiting CVEs in enterprise environments today.
The NVD will continue to serve a vital function, and we appreciate NIST's transparency about the resourcing constraints driving these changes. But the gap defenders face is bigger than the April 15 announcement describes, and it was always bigger than enrichment.
The question that matters isn't whether you have metadata. It's whether you know what's being weaponized, who's wielding it, and whether you can act on that before it reaches your environment. That's what we've been building. That's what we intend to keep doing.
Prioritize cyber risk. Secure it first.


