
DarkSide Ransomware: Further Threat Associations Unearthed
Sumeetha Manikandan
Securin Team


Jun 30, 2021
Last month, DarkSide ransomware went down in history for causing the single largest disruption in gasoline supply in the United States. The attack was so crippling that fuel prices peaked, panic buying was induced, and almost 45% of the East Coast’s fuel supply was cut off. It took a week of reconstruction, alongside the FBI’s interference and a $5M ransom payment, to bring the supply back online. Subsequently, the FBI recovered about half of the ransom paid after gaining access to the bitcoin account that was used in the transaction.
More CVE Findings
In our previous blog, we observed how the DarkSide ransomware group utilized two vulnerabilities, CVE-2019-5544 and CVE-2020-3992, to launch its attacks on the Colonial Pipeline. Since then, we have come across more interesting findings about this ransomware.
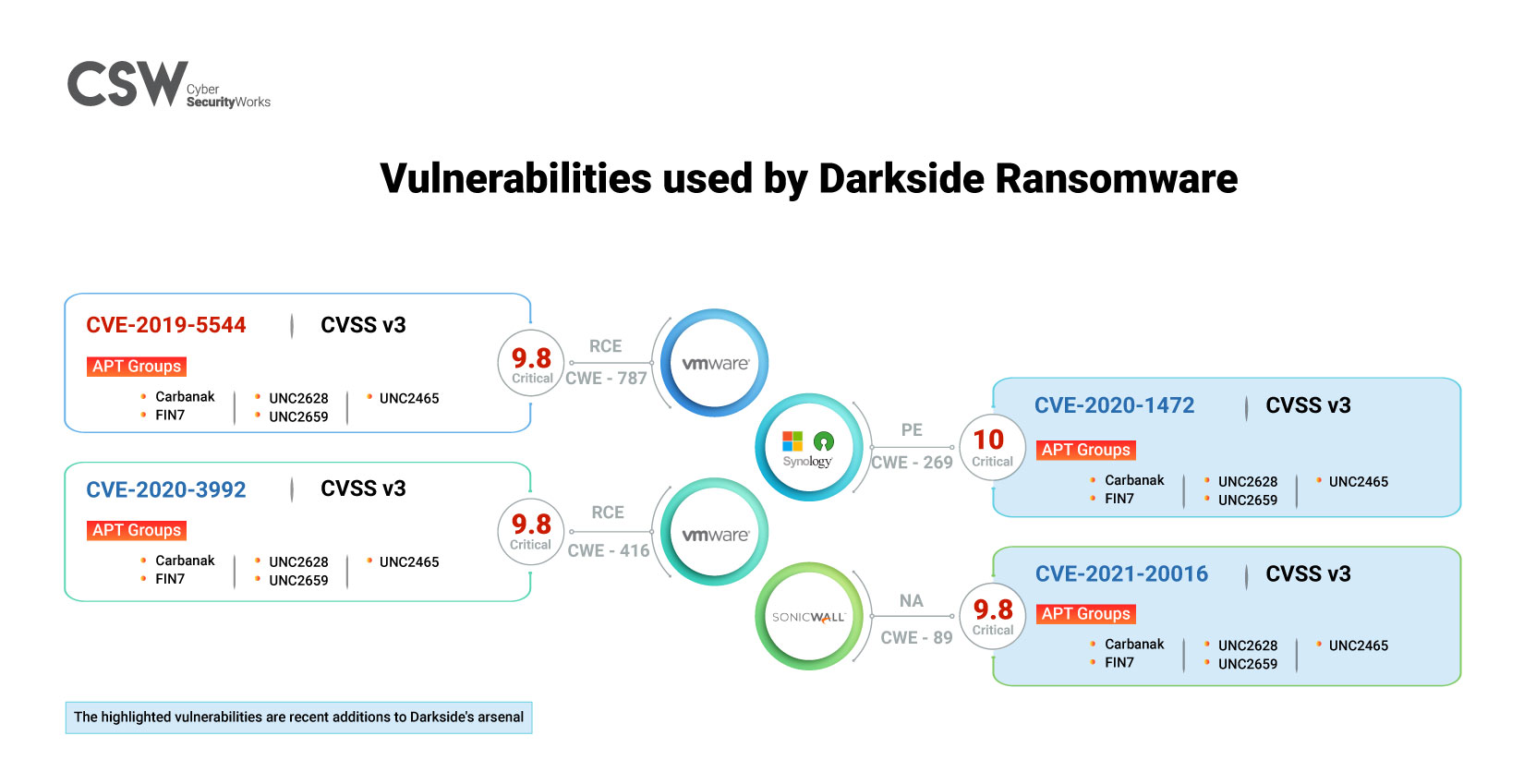
- CVE-2021-20016 is a new vulnerability identified earlier this year. It is assigned a CVSS V3 score of 9.8 and tagged as a critical flaw.
- The vulnerability exists across six SonicWall Secure Mobile Access (SMA) products, which act as an access gateway for organizations to provide remote access to resources hosted on-prem, in cloud, and in hybrid data centers.
- The SonicWall advisory has published workarounds for this vulnerability.
CVE-2020-1472
- CVE-2020-1472, popularly known as the Zerologon vulnerability, is a critical 2020 CVE that has a CVSS V3 score of 10. It can be exploited to gain elevated access to resources.
- CVE-2020-1472 is seen in 11 products spread across vendors Microsoft, Fedora project, openSUSE, Canonical, Synology, and Samba.
- Security updates are available for patching the vulnerability.
- In our Ransomware Report 2020, we noted that CVE-2020-1472 was also weaponized by the CryptoMix ransomware family, which is associated with five other ransomware groups.
Exposure
- From our exposure analysis using Shodan, we can see that 2,911 deployments of SonicWall SMA 200 firmware and 688 products with CVE-2020-1472 are currently in use, making them vulnerable to attacks.
The DarkSide Attack Methodology
The threat actors have been identified using the Tor browser, which creates a multi-hop proxy network. Messages are encrypted at multiple levels using onion routing, allowing for increased anonymity on the internet. The DarkSide ransomware group has also been observed deploying Cobalt Strike as its command and control weapon. Cobalt Strike is a collection of threat emulation tools that is seeing more and more adoption by malicious groups.
According to the latest news reports, the Colonial Pipeline attack happened because of leaked credentials of a virtual private network (VPN) account, through which employees remotely accessed the company’s network. While we may not exactly know what VPN vulnerability led to the breach, a lesson learned is that it is important to ensure the safety of VPNs and other applications we use. Securin has always emphasized and even warned about this in our Cyber Risk Series.
DarkSide Ransomware MITRE ATT&CK Mapping
The following tactics and techniques are in addition to the previously published MITRE ATT&CK mapping details.
MITRE ATT&CK | IOC |
T1087 – Account Discovery T1098 – Account Manipulation T1027.004 – Compile After Discovery T1555 – Credentials From Password Stores T1555.002 – Credentials From Registry T1486 – Data Encrypted For Impact T1140 – Deobfuscate/Decode Files or Information T1055.001 – Dynamic-Link Library Injection T1190 – Exploit Public-Facing Application T1133 – External Remote Services T1083 – File and Directory Discovery T1105 – Ingress Tool Transfer T1490 – Ingress System Recovery T1036 – Masquerading T1090.003 – Multi-hop Proxy T1027 – Obfuscated Files or Information T1566 – Phishing T1059.001 – Powershell T1057 – Process Discovery T1113 – Screen Capture T1569.002 – Service Execution T1489 – Service Stop T1129 – Shared Modules T1082 – System Information Discovery T1080 – Taint Shared Content T1047 – Windows Management Instrumentation | MD5: 978754BAA3A4D39802CDC8AA34DCA578 71367B599A8AB75BA64EC40FD138D650 D79793DD17A85C4F7BB9347D43DC5924 84F97E8028530A90827B6C92E0C083CA A4064976B08133C11C15FC6DC0FB6F10 B38278344CCF7FFC3818947AE41ECD3C 952C0F33EDE5AFBF8AA58FBDA7AA5A70 AC20EAAC8992F4F7E835BD583DC1F6C5 DB511D27139D193C865A0C5DB192E0CF 417E4F1E69AED14DE8F4A3B4DF3BD0BA 52C91A73CFB979A07697CFECA9150774 71B888DEA662F49F0B0945BBB4DDE5E6 748D28BBBB37DFC2DD0D6D14E8C06FCE A6F0F346AE042E129D56094E66965256 FB8678BB3F0F33D686145575C75AB304 2D7333BDDD899BAC2C667E913F5E5C0C 60A22A01C8A1DDF5B31FA9A879786761 6C6BA57BE4B7B2FB661A99FEA872F6B8 2BB5D5AA07FA2C8E9874C117C8FA51D6 |
Has DarkSide Truly Retired? The Question Remains…
Recent research highlights a new DarkSide ransomware variant that projects a behavior unseen to date. Found to affect Windows platforms, the new find seeks out partition information on hard disks to identify hidden data and can even compromise multi-boot systems.
Fraudsters have also been observed impersonating the DarkSide ransomware group in more recent activities, trying to capitalize on the impact of the increase in ransomware affairs. The fact is that remediation following a ransomware attack is a cumbersome process. Organizations need to take proactive measures to ensure they do not become a victim of such attacks.
{Updated on July 13, 2021}: As recently as July 2021, the popular fashion brand, Guess, announced that it had fallen victim to an attack by DarkSide back in February and warned of customer data leaks on the dark web. The information released included classified information like the company’s financial details, customers’ Social Security Numbers, driver’s license numbers, passport numbers, and financial account numbers.
{Updated on August 19, 2021}: Three months after the Colonial Pipeline incident, the repercussions are still being felt. The company recently identified that the DarkSide operators got their hands on documents containing the personal data of over 5,000 people and has started sending out notification letters to affected individuals.
We can help you analyze your assets and prioritize the vulnerabilities that need to be patched.


