Cyber Threat Intelligence Report: Water & Wastewater Systems
Securin Research Team
Securin Team


March 27, 2026
The United States operates roughly 150,000 public water systems serving over 300 million people — and the sector is under siege. From Iranian IRGC-affiliated hackers defacing PLC screens in Pennsylvania to Russian GRU-linked operators overflowing water tanks in Texas, the Water & Wastewater Systems sector has moved from a soft target to an active battlefield. Securin's analysis of 1,807 vulnerabilities impacting products deployed across this sector reveals a threat landscape that is growing faster than the industry can defend against it — and an adversary ecosystem that has learned to exploit the sector's structural weaknesses with precision.
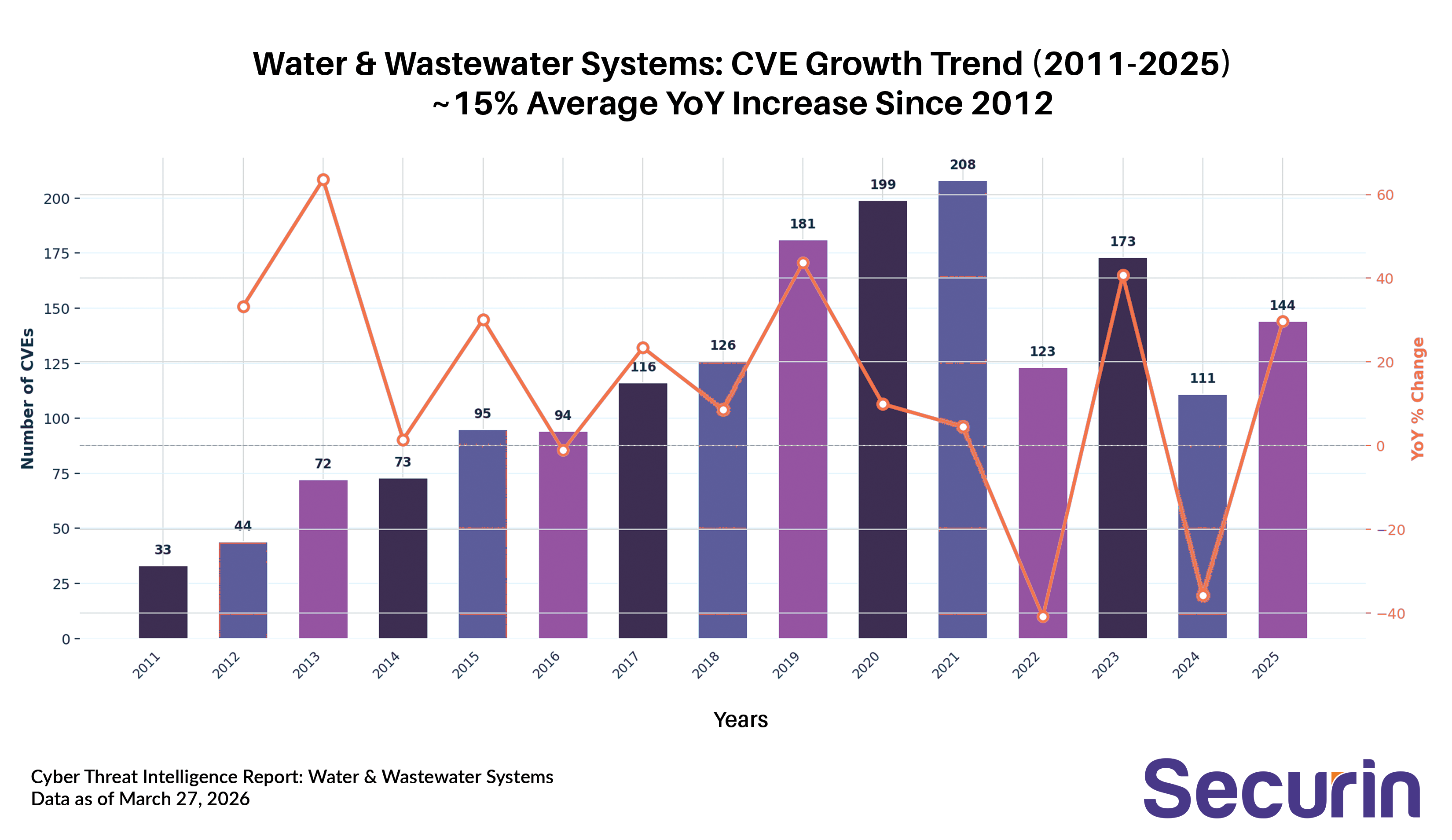
The Vulnerability Landscape: A Widening Attack Surface
Since 2012, the volume of new CVEs affecting Water & Wastewater Systems products has grown at an average rate of ~15% year over year. What began as a trickle — just 33 CVEs in 2011 — has become a flood: 181 in 2019, peaking at 208 in 2021. Even after a dip in 2022 (likely due to shifting researcher focus rather than improved security), the count rebounded to 173 in 2023, and 2025 is already tracking at 144 with the year still underway. The trajectory is clear: the attack surface is expanding faster than the sector can shrink it.
But raw volume only tells part of the story. The real risk lies in the attack funnel — how many of those vulnerabilities have been weaponized and are actively exploited. Of the 1,807 total CVEs, 222 have been weaponized with publicly available exploit code or proof-of-concept. 43 are actively exploited in the wild, including 24 listed in CISA's Known Exploited Vulnerabilities (KEV) catalog. Most critically, 10 are directly linked to nation-state threat actors from Iran, Russia, and China, and 6 are associated with ransomware operations. These are not theoretical risks — they are CVEs with confirmed adversary tradecraft behind them.
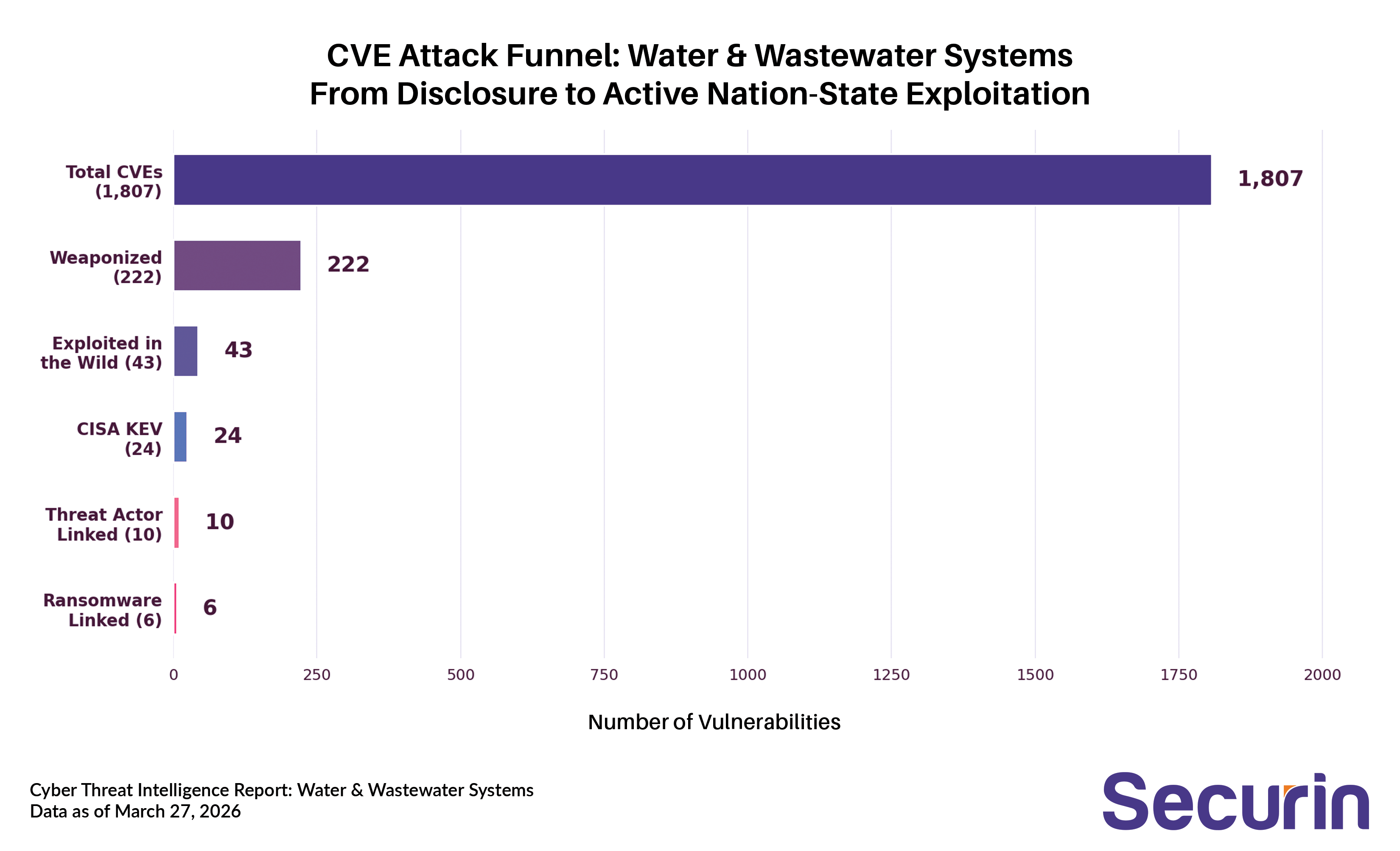
The math is sobering: for every 100 vulnerabilities disclosed in the water sector, roughly 12 get weaponized, and 2 end up actively exploited in the wild — often by adversaries with the resources and intent to cause real-world physical harm.
Weakness Analysis: Where the Code Breaks
Mapping these 1,807 CVEs to their underlying software weaknesses (CWEs) reveals systemic patterns rooted in how water sector technology is built — and how long it stays in service. Improper Input Validation (CWE-20, 229 CVEs) dominates the landscape. This class of flaw, where systems fail to properly validate data before processing it, is a gateway to everything from remote code execution to denial of service. In SCADA environments where PLCs and HMIs accept commands from networked sources, unvalidated input can translate directly to manipulated physical processes.
Memory corruption vulnerabilities represent the second major cluster: buffer overflows (CWE-119, 162 CVEs), out-of-bounds writes (CWE-787, 142), stack-based overflows (CWE-121, 92), and heap overflows (CWE-122, 63) collectively account for over 500 CVEs. This reflects the heavy reliance on legacy C/C++ codebases in industrial control systems — firmware that was written for reliability, not security, and often runs for decades without updates. SQL Injection (CWE-89, 128 CVEs) and OS Command Injection (CWE-78, 44) represent direct remote exploitation vectors into web-based management interfaces and SCADA gateways.
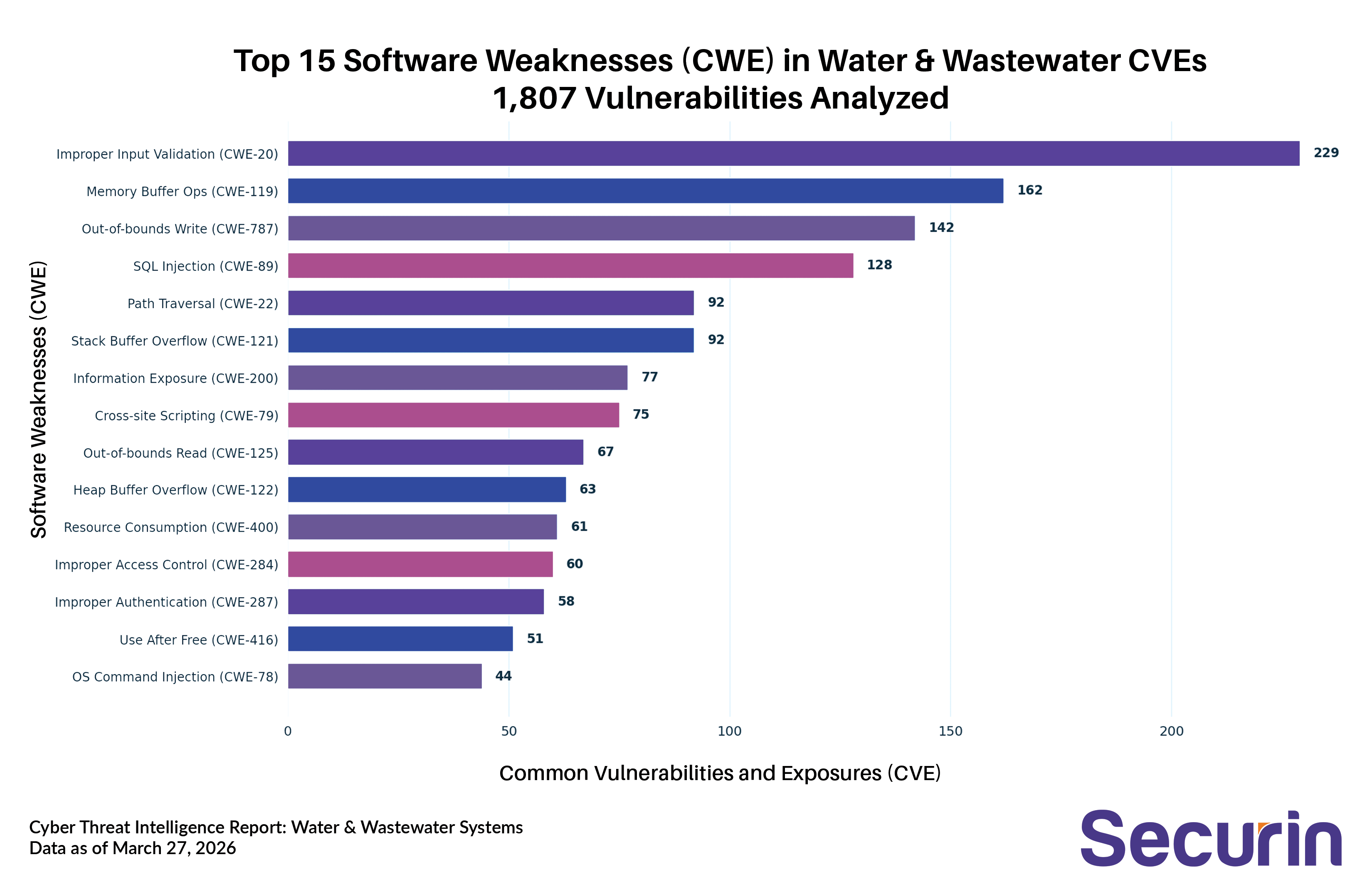
Perhaps most telling for the water sector specifically: Hard-coded Credentials (CWE-798, 38 CVEs) and Missing Authentication for Critical Functions (CWE-306, 36 CVEs) rank in the top 20. These are the exact categories of weakness that enabled Iran's CyberAv3ngers to breach the Aliquippa water authority — Unitronics PLCs shipped with default passwords that were never changed. Among the 43 CVEs actively exploited in the wild, Improper Input Validation remains the top weakness (12 CVEs), followed by Memory Buffer Operations (8) and Hard-coded Credentials (2), confirming that attackers are targeting the same fundamental flaws that have plagued ICS/SCADA systems for years.
MITRE ATT&CK Analysis: How Attackers Operate
Mapping all 1,807 CVEs to the MITRE ATT&CK framework reveals the full tactical playbook adversaries can leverage against water infrastructure. The mapping spans all 13 ATT&CK tactics, indicating that the sector's vulnerability portfolio provides attackers with options at every stage of the kill chain — from initial reconnaissance through to physical impact.
Defense Evasion (976 CVEs) leads overwhelmingly. This means nearly half of all water sector CVEs can be exploited to help attackers hide their presence — through techniques like obfuscating files, masquerading as legitimate processes, disabling event logging, and impeding command history. In environments where security monitoring is already minimal, this is especially dangerous: attackers can dwell undetected for extended periods. Privilege Escalation (768) and Execution (767) follow closely, providing the capability to escalate from an initial foothold — often a compromised web interface or exposed PLC — to full system control. Credential Access (737 CVEs) rounds out the top four, which is particularly dangerous in water environments where shared credentials, legacy NTLM authentication, and unencrypted protocols remain common.
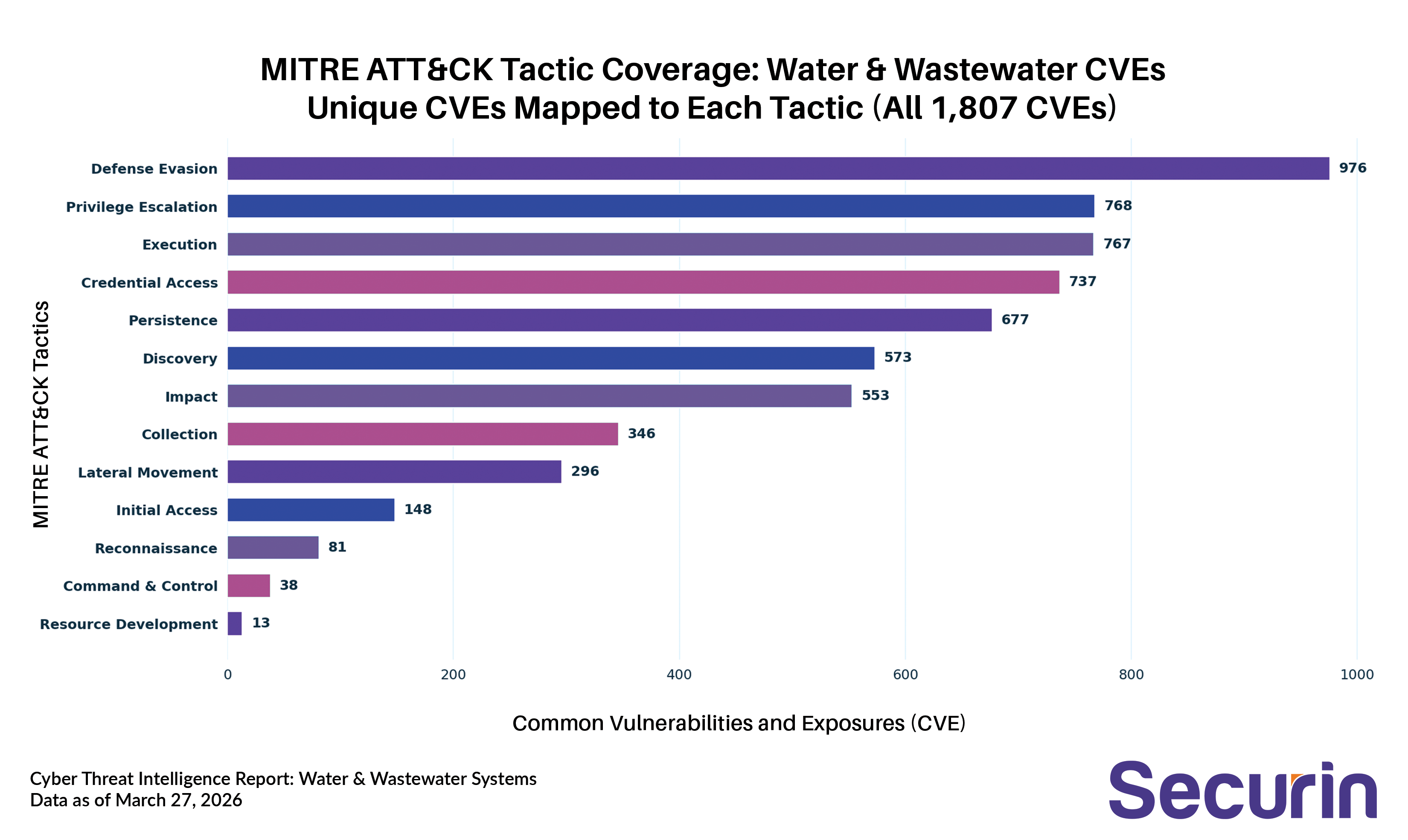
The lower end of the spectrum is equally instructive. Initial Access (148 CVEs) and Lateral Movement (296) — while smaller in count — represent the most operationally critical stages. These are the CVEs that let attackers get in the door and move from IT to OT networks. Every one of them warrants priority patching. Focusing on the 43 CVEs exploited in the wild narrows the picture further: the top techniques include Exploitation for Client Execution (16), Obfuscated Files or Information (16), Hijack Execution Flow (15), and Abuse Elevation Control Mechanism (15) — a pattern consistent with adversaries seeking persistent, stealthy access to operational technology environments before executing their objectives.
Threat Actors: Who Is Targeting Water Infrastructure
Securin's threat intelligence identifies four threat actor groups and one ransomware family with direct, confirmed targeting relationships to the Water & Wastewater Systems sector. Each represents a distinct threat profile.
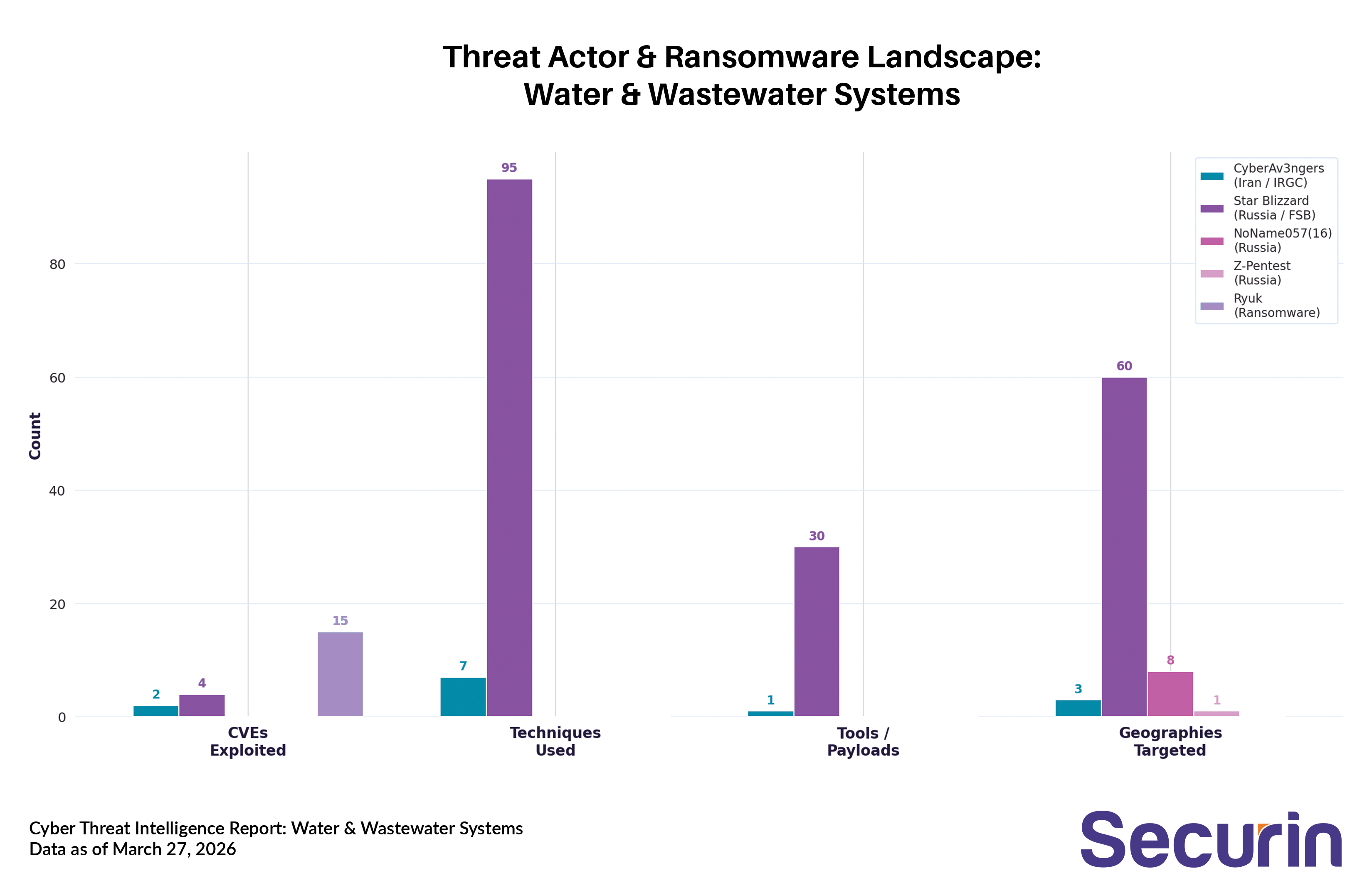
CyberAv3ngers (Iran, IRGC-Affiliated): Motivated by destruction and sabotage, this IRGC-linked group exploited CVE-2023-6448 (Unitronics Vision PLC, CISA KEV) to breach multiple U.S. water facilities in late 2023. Their playbook is ICS-specific and devastatingly simple: scan for internet-accessible devices, authenticate using default credentials, then achieve loss of view, loss of availability, and denial of service across the OT environment. They targeted Unitronics PLC firmware across 15+ product variants spanning Industrial Control Systems, Remote Management, and Security Tools categories. The U.S. Treasury sanctioned specific IRGC cyber actors in response. Their geographic footprint spans the United States, Israel, and Ireland.
Star Blizzard (Russia, FSB-Linked): The most technically sophisticated actor in this sector. Active since 2013 with 38 known aliases (including Gamaredon, Cold River, Callisto Group, Seaborgium, and Primitive Bear), Star Blizzard operates across all 14 MITRE ATT&CK tactics with 95 documented techniques and 30+ tools including Spica malware, Pteranodon, Remcos RAT, GammaSteel, GammaLoad, and PowerPunch. Their exploited CVEs include CVE-2017-0199 (Microsoft Office RCE, CISA KEV), CVE-2025-8088 , CVE-2025-6218, and CVE-2018-20250 (WinRAR ACE). They target Collaboration Platforms, Operating Systems, and Remote Management tools — the same IT infrastructure water utilities rely on for day-to-day operations. With a geographic footprint spanning 60+ countries, they represent a persistent espionage and pre-positioning threat.
NoName057(16) (Russia, Hacktivist): A DDoS-focused group targeting NATO-aligned nations including Ukraine, Poland, Norway, Denmark, and Czechia. While less sophisticated, their volume-based attacks add operational pressure to an already strained sector.
Z-Pentest (Russia, Hacktivist): An emerging group targeting OT/ICS systems, with documented operations against water infrastructure in Denmark.
Ryuk (Ransomware): The only ransomware family with a confirmed attack on this sector, Ryuk exploits 15 CVEs — 11 of which are CISA KEVs. Its arsenal leverages some of the most dangerous legacy vulnerabilities in existence: EternalBlue (CVE-2017-0144, Risk Index 9.82), Zerologon (CVE-2020-1472), and MikroTik RouterOS (CVE-2018-14847, Risk Index 9.97). These are vulnerabilities that have been patched for years — yet persist in the water sector's under-resourced, legacy-heavy environments.
Real-World Impact: A Pattern of Escalation
The past three years have seen cyber attacks on water systems escalate from digital nuisance to physical consequence — a trajectory that tracks directly with the vulnerability and threat actor data above.
In November 2023, CyberAv3ngers hit the Municipal Water Authority of Aliquippa, Pennsylvania — the first publicly confirmed ICS compromise of a U.S. water facility by a nation-state actor. They exploited CVE-2023-6448, a critical flaw in Unitronics Vision PLCs shipped with default passwords. In January 2024, Russian-linked hackers (Cyber Army of Russia Reborn, tied to GRU's Sandworm unit) breached a water facility in Muleshoe, Texas and caused a water tank to overflow for 30–45 minutes before operators could switch to manual control. In Denmark, hackers manipulated pressure controls at a treatment plant and burst three pipes. In October 2024, American Water — the largest regulated U.S. water utility, serving 14 million people across 14 states — suffered a cyber attack that shut down customer-facing systems for a week. Since 2006, Dragos has documented at least 27 publicly confirmed cyber events targeting U.S. water and wastewater systems, though the real number is almost certainly higher: the EPA's Inspector General has flagged weaknesses with incident reporting that leave many attacks undisclosed.
The systemic picture is equally alarming. A 2024 GAO audit of just 1,062 drinking water systems found 97 with critical or high-risk vulnerabilities serving 26.6 million Americans — and another 211 systems serving 82.7 million people had externally visible open portals. The EPA reported that over 70% of water systems inspected since September 2023 violated basic cybersecurity requirements under the Safe Drinking Water Act.
Conclusion
With 1,807 vulnerabilities, 222 weaponized, nation-state actors from Iran and Russia actively in the network, and physical consequences already demonstrated — the water sector's cybersecurity crisis is not approaching; it has arrived. The average 15% year-over-year growth in CVEs, combined with an industry where the majority of 150,000 systems lack dedicated cybersecurity staff, means the gap between threat capability and defensive capacity is widening with each disclosure cycle. The weaknesses are known — input validation, memory corruption, default credentials. The attackers are named — CyberAv3ngers, Star Blizzard, Sandworm proxies, Ryuk. The question is no longer whether the sector will be hit again, but whether it will have fixed the default passwords before it is.
Data sourced from Securin's threat intelligence platform, CISA KEV catalog, MITRE ATT&CK framework, NVD, GAO (GAO-24-106744), EPA OIG, and Dragos. Analysis current as of March 2026.


