CISA Launches Known Exploited Vulnerabilities (KEV) Catalog
Surojoy Gupta
Securin Team


Sep 12, 2022
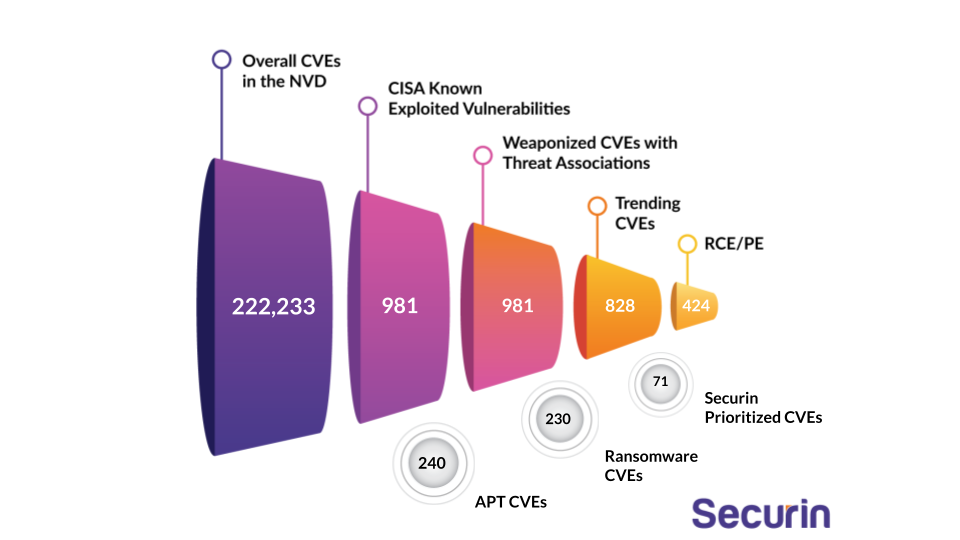
The Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA) released a Binding Directive mandating organizations to patch a list of Known Exploited Vulnerabilities (KEV) on November 03, 2021, with specified deadlines. This catalog started with 287 vulnerabilities, and the count stands at 981 today.
This blog performs risk-based scrutiny of the vulnerabilities included in the catalog and provides additional threat context for each vulnerability.
Our researchers deep-dived into these vulnerabilities to understand the criticality of these CVEs and why they need to be addressed within the deadlines specified by CISA.
Firstly, let us look at how many vulnerabilities ought to be patched immediately.
CVEs to be Patched by August 2023
We have already crossed the patching deadline for 963 of the CISA KEVs. There are a further 22 vulnerabilities that need to be patched by the end of August 2023.
We are fast running out of time to patch the CISA KEVs, with the last due date currently on the list being Augest 28, 2023. If your organization still has a long way to go, Securin can help you prioritize the ones that pose the most danger to you.
Patching Deadlines
DHS CISA’s initiative of reducing risk through the Known Exploited Vulnerabilities (KEV) catalog is a remediation drive with strict timelines. Below, we look at the stipulated deadlines by which sets of vulnerabilities need to be patched.
Patching Deadlines | Number of CVEs |
Aug-23 | 16 |
Jul-23 | 15 |
Jun-23 | 22 |
May-23 | 15 |
Apr-23 | 19 |
Mar-23 | 17 |
Feb-23 | 5 |
Jan-23 | 10 |
Dec-22 | 8 |
Nov-22 | 15 |
Oct-22 | 13 |
Sep-22 | 40 |
Aug-22 | 29 |
Jul-22 | 35 |
Jun-22 | 128 |
May-22 | 218 |
Apr-22 | 127 |
Mar-22 | 103 |
Feb-22 | 15 |
Jan-22 | 3 |
Dec-21 | 126 |
Securin Publicly Called Out KEVs
Securin’s researchers have called out 203 of the 812 vulnerabilities in the past through detailed blogs, exhaustive coverage of patch watch news items, and comprehensive reports. Below, we look at some of the vulnerabilities that were added to the KEVs post our call out.
CVE | Called Out by Securin Experts | Reference Link | Added to CISA | Securin Warning Ahead of CISA (Days) |
CVE-2019-1130 | May 18, 2022 | May 23, 2022 | 5 | |
CVE-2019-1385 | May 19, 2022 | May 23, 2022 | 4 | |
CVE-2020-0638 | May 20, 2022 | May 23, 2022 | 3 | |
CVE-2022-30333 | July 08, 2022 | Aug 09, 2022 | 32 | |
CVE-2022-26923 | July 25, 2022 | Aug 18,2022 | 24 | |
CVE-2022-2856 | Aug 16, 2022 | Aug 18,2022 | 2 | |
CVE-2022-0028 | Aug 09, 2022 | Aug 22, 2022 | 13 | |
CVE-2022-26352 | Aug 8, 2022 | Aug 25, 2022 | 17 | |
CVE-2022-2294 | Aug 8, 2022 | Aug 25, 2022 | 17 | |
CVE-2020–9934 | July 18, 2022 | Sep 08, 2022 | 52 | |
CVE-2022-40684 | Oct 10, 2022 | Oct 11, 2022 | 1 | |
CVE-2021-3493 | Sep 9, 2022 | Oct 20, 2022 | 41 | |
CVE-2022-41352 | Oct 3, 2022 | Oct 20, 2022 | 17 | |
CVE-2018-19320 | February 13, 2021 | Oct 24, 2022 | 618 | |
CVE-2022-42827 | Oct 25, 2022 | Oct 25, 2022 | 0 | |
CVE-2022-26500 | Oct 25, 2022 | Dec 13, 2022 | 49 | |
CVE-2022-26501 | Oct 25, 2022 | Dec 13, 2022 | 49 | |
CVE-2023-0669 | Feb 6, 2023 | Feb 10, 2023 | 4 | |
CVE-2022-24990 | Feb 6, 2023 | Feb 10, 2023 | 4 | |
CVE-2015-2291 | Jan 9, 2023 | Feb 10, 2023 | 32 | |
CVE-2023-23529 | Jan 9, 2023 | Feb 14, 2023 | 36 | |
CVE-2022-46169 | Jan 9, 2023 | Feb 16, 2023 | 38 | |
CVE-2022-47986 | Feb 13, 2023 | Feb 21, 2023 | 8 | |
cve-2022-36537 | Feb 20, 2023 | Feb 27, 2023 | 7 | |
CVE-2022-41328 | Mar 14, 2023 | Mar 14, 2023 | Same Day | |
CVE-2021-30900 | Mar 27, 2023 | Mar 30, 2023 | 3 | |
CVE-2022-38181 | Mar 27, 2023 | Mar 30, 2023 | 3 | |
CVE-2023-0266 | Mar 27, 2023 | Mar 30, 2023 | 3 | |
CVE-2022-3038 | Mar 27, 2023 | Mar 30, 2023 | 3 | |
CVE-2022-22706 | Mar 27, 2023 | Mar 30, 2023 | 3 | |
CVE-2017-7494 | Feb 13, 2021 | Mar 30, 2023 | 775 | |
CVE-2022-27926 | Mar 27, 2023 | Apr 03, 2023 | 7 | |
CVE-2021-27876 | Apr 03, 2023 | Apr 07, 2023 | 4 | |
CVE-2021-27877 | Apr 03, 2023 | Apr 07, 2023 | 4 | |
CVE-2021-27878 | Apr 03, 2023 | Apr 07, 2023 | 4 | |
CVE-2019-1388 | May 14, 2021 | Apr 07, 2023 | 693 | |
CVE-2023-28206 | Apr 03, 2023 | Apr 10, 2023 | 7 | |
CVE-2023-28205 | Apr 03, 2023 | Apr 10, 2023 | 7 | |
CVE-2019-8526 | Jan 02, 2023 | Apr 17, 2023 | 105 | |
CVE-2023-1389 | Apr 24, 2023 | May 01, 2023 | 7 | |
CVE-2023-21839 | Mar 06, 2023 | May 01, 2023 | 56 | |
CVE-2021-45046 | Aug 30, 2022 | May 01, 2023 | 244 | |
CVE-2023-25717 | May 08, 2023 | May 12, 2023 | 4 |
Threat Analysis
A major part of our vulnerability research is the analysis of threat groups, including Advanced Persistent (APT) Groups and ransomware groups that are exploiting the vulnerabilities. In this section, we discuss the threat groups associated with the Known Exploited vulnerabilities warned about by CISA.
Advanced Persistent Threat (APT) Groups
240 of CISA KEVs have APT associations, with over 50% of the CVEs linked to multiple groups. A huge majority of these APT groups have links to China, followed by Russian state-sponsored groups.
CVE-2012-0158 and CVE-2017-11882 have over 20 APT groups associated with each of them, making them pet favorites of threat actors.
- CVE-2012-0158 is a remote code execution vulnerability in Microsoft’s Windows Common Controls (MSCOMCTL.OCX). With a critical CVSS severity of 9.3, the vulnerability belongs to the weakness CWE-94, leading to code injection issues.
- CVE-2017-11882 is a remote code execution vulnerability that exists in Microsoft Office versions 2007 to 2016. Its weakness CWE-119, leads to Improper Restriction of Operations within the Bounds of a Memory Buffer, one of the Top 20 Most Dangerous Software Weaknesses as listed by MITRE
APT29 or the Nobelium group is the single most prolific APT amongst this group, with links to 53 of the APT vulnerabilities. This is the threat group behind the infamous SolarWinds supply chain attack back in December 2021.
Ransomware
230 of CISA KEVs have ransomware associations, with over 50% linked to multiple groups. Eight vulnerabilities have been identified as exploited by more than 10 ransomware groups each.
CVE-2015-0359 has more than 50 ransomware associations with the likes of Cerber, Reveton, Cryptomix and Magniber on the list. CVE-2013-7331 and CVE-2013-3896 have more than 35 groups associated with each of them, including the infamous Sodinokibi and Cerber families.
A notable call out is CVE-2017-0143 which has 11 ransomware associations and 9 APT associations, marking it as a formidable threat to organizations using Microsoft Server Message Block servers. The Citrix vulnerability, CVE-2019-19781, is another worthy mention with 12 ransomware and 7 APT associations.
Exploit Analysis
All the CISA KEVs have faced heavy exploitation at one point of time or the other. Exploits available for these KEVs include exploits falling into four different categories:
- Remote Code Execution (RCE) that can allow attackers to execute custom code from anywhere
- Privilege Escalation (PE) providing attackers with elevated privileges once they gain entry into a network
- Denial of Service (DoS) that can lead to network takeovers or complete shutdown
- Web Application (WebApp) Exploit codes capable of compromising web applications.
Let’s look into an exploit breakdown for the CISA vulnerabilities.
Exploit Type | No. of CVEs |
|---|---|
RCE/PE | 424 |
RCE | 363 |
PE | 230 |
DoS | 98 |
WebApp | 287 |
Note: Some CVEs have multiple exploits associated with them.
With over 40% of the vulnerabilities having dangerous RCE/PE exploit codes, it is of utmost importance that organizations address these vulnerabilities at the earliest. If exploited, the consequences could be grave.
Latency Analysis
As part of our exploit analysis, we studied the latencies in the National Vulnerability Database (NVD) disclosure that magnified the impact of the exploited vulnerabilities.
Latency Metrics | Overall | Critical | High | Medium | Low |
Exploit before patch | 188 | 98 | 76 | 14 | – |
Same day | 121 | 44 | 65 | 12 | – |
Exploit after patch | 548 | 178 | 292 | 76 | 2 |
Further, we also compared latencies with respect to patches released for the vulnerabilities to understand the trends behind attacks waged by hackers and threat actors alike.
Latency Metrics | Overall | Critical | High | Medium | NA |
Same day | 373 | 108 | 91 | 15 | 1 |
Patch after CVE disclosure | 223 | 98 | 72 | 17 | – |
Patch before CVE disclosure | 276 | 123 | 225 | 56 | 2 |
Note: The vulnerability disclosure date is considered as the earliest date on which the CVE is released to the public, either by its vendor or the NVD.
We identified some interesting observations from our latency analysis of the CISA KEVs.
- Attackers are going after vulnerabilities even if they have existing patches or workarounds. Interestingly, most of the exploit codes were made publicly available after a patch was released for the vulnerability. This makes a strong case for organizations to revisit their patching cadence and address the vulnerabilities with a higher probability of exploitation.
- Vulnerabilities are often identified and patched before they are added to the NVD. Thus, while the NVD is a reliable source, organizations need a more accurate threat intelligence platform to remediate potential threats proactively.
Weakness Analysis
The CISA KEVs are manifestations of over 70 different weaknesses in software. Almost 70% of these common weakness enumerations (CWEs) are part of MITRE’s Top 41 CWEs, and 57% are categorized under OWASP’s Top 10 error categories. This highlights the serious implications of these vulnerabilities that are present across hundreds of products currently being used by thousands of users.
Here is a look into the top five weaknesses paving the way for the CISA KEVs:
Weakness | Description | Number of vulnerabilities | OWASP Ranking | MITRE Ranking |
|---|---|---|---|---|
CWE-20 | Improper input validation | 109 | A3 (Sensitive Data Exposure) | 4 |
CWE-119 | Improper Restriction of Operations within the Bounds of a Memory Buffer | 82 | – | 17 |
CWE-787 | Out-of-bounds Write | 76 | – | 1 |
CWE-78 | Improper Neutralization of Special Elements used in an OS Command (‘OS Command Injection’) | 54 | A3 (Sensitive Data Exposure) | 5 |
CWE-416 | Use after free | 47 | – | 7 |
All developers need to be aware of the weaknesses they are introducing during the design stage and take steps to avoid such errors at the source.
Patch Analysis
About 47% of the CISA KEVs have direct patches available. For the rest, mitigations such as upgrades or workarounds are available. Overall, 50% of the CISA KEVs have workarounds. We strongly recommend organizations to immediately apply the workarounds in the event that they are unable to patch the vulnerabilities immediately.
The Way Forward
A meticulous remediation drive is definitely the need of the hour, as it forces the hand of federal entities and critical organizations to take immediate action to improve their cyber hygiene.
However, with the CISA KEV list now expanding to include 900+ vulnerabilities, organizations that haven’t managed to keep up are at a loss. With no threat context available, security teams are struggling to prioritize from amongst these KEVs.
Securin researchers have been closely monitoring the developments, and we can help organizations understand why a certain KEV needs to be prioritized. Our definitive threat intelligence can provide the much needed threat context to connect the dots and close the gaps in your security strategy!
Note: This story is continuously evolving, so please follow our blogs to keep abreast of the updates to the CISA KEV, and their detailed analysis.


