
All About Ryuk Ransomware
Pavithra Shankar
Securin Team


Apr 16, 2021
Did you know that in 2020 Ryuk ransomware targeted 67.3 million targets?
What is Ryuk?
Ryuk is a crypto-ransomware strain that encrypts access to a system, device or a file and demands ransom to release it. Ryuk is unleashed on target assets through malware, notably TrickBot and is used to gain access to a system through remote desktop services.
Ryuk typically targets vulnerable organizations or critical entities like hospitals where the probability of ransom payout is high. And since the ransom is their primary motive they demand more than any other ransomware threat group. The ransom amount oscillates between $100,00 to $500,00 in bitcoins and they are very successful in their campaigns because they select high-profile targets for whom data and information is sacrosanct and hence the chance of the payout is high.
Ryuk debuted in mid-August 2018 and was being operated by Wizard Spider, a sophisticated group that targeted large organizations with critical and sensitive data for high ransom payouts.
The creation of Ryuk is generally attributed to a cybercriminal group known as CryptoTech who were selling Hermes 2.1 in underground forums but there are researchers who believe that it was created by the Russian cyber criminal cartel.
New Variant
Researchers noted that since July 2020, a new variant called Conti has been making the rounds. The consensus among security experts is that Ryuk threat actors have rebranded themselves as Conti ransomware.
Conti is a private Ransomware as a Service (RaaS) that encrypts files and delivers the ransom note.
The converging similarities in Ryuk and Conti can be seen through features –
- Encrypts files stored on network
- Disables backup and OS services
- Can be manually deployed
- Infects local disks
- Linked to same developer group based on the malware code
- AES-256 encryption key being used
- Same ransom text template is observed
- Both use TrickBot framework
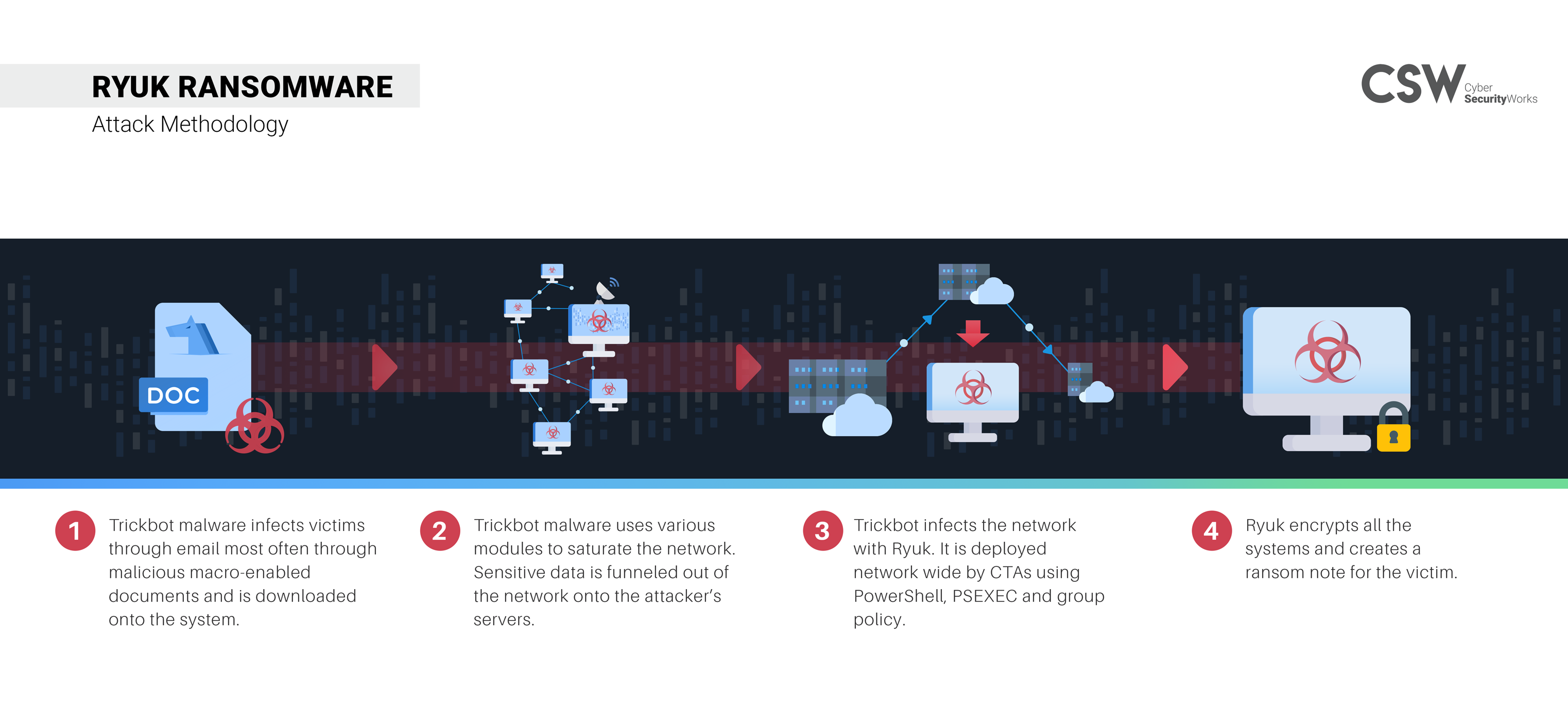
How does Ryuk attack?
Ryuk is primarily spread through malware that drops the ransomware on the existing infected system. Here is how it attacks –
Ryuk MITRE ATT&CK Mapping
ATT&CK Tactic Category | Techniques |
|---|---|
Privilege Escalation | T1134 – Access Token Manipulation |
Persistence | T1547 – Boot or Logon Autostart T1059 – Command and Scripting |
Impact | T1486 – Data Encrypted for Impact T1490 – Inhibit System Recovery T1489 – Service Stop |
Discovery | T1083 – File and Directory Discovery T1057 – Process Discovery |
Defense Evasion | T1055 – Process Injection |
Execution | T1106 – Native API |
Ryuk – A Cheat Sheet
- Ryuk has within its arsenal 17 CVEs that it exploits to mount attacks on its victims.
- The year of discovery of these CVEs range from 2013 to 2020.
- Six CVEs are Remote Code Execution Exploits (RCE) and one CVE is a Privilege Execution.
- 57% of CVEs that are in Ryuk’s arsenal are rated critical, 5 are medium and 1 of low severity.
- Five CVEs in numerical order (CVE-2017-0143, CVE-2017-0144, CVE-2017-0145, CVE-2017-0146, CVE-2017-0147) are tied to five APT groups.
- Seven CVEs exist in Microsoft products such as Windows Vista, Windows Server (2007, 2008, 20012, 2010, 2016, 2019 ) Internet explorer, Microsoft Edge etc.
- Five CVEs are weaknesses that exist in multiple products such as Novell, Fedoraproject, Debian, Canonical, Huawei, Gentoo, Oracle, Amazon, IBM, Openbsd, Winscp, Netapp, redhat, VMware, synology, samba etc.
- External Blue kit is used to exploit vulnerabilities – CVE-2017-0143 and CVE-2017-0144.
- All 17 CVEs have patches and it is recommended that they be prioritized for remediation immediately.
- CWE – 20 is the most exploited weakness among the Ryuk associated CVEs which topped third in the Top 25 Common Weakness Enumeration.
- CVE-2020-1472 is a recent CVE added in Ryuk’s arsenal while the rest are old. This brings the focus back to cyber hygiene that needs to be practiced diligently.
- CVE-2018-1156 and CVE-2018-14847 are RCE bugs where Ryuk comprises an unpatched Mikrotik router and turns it into a command and control server that infects with rootkits.
Threat Groups & APT Groups
Ryuk is associated with the following threat and APT groups, which use Ryuk to launch complex cybersecurity attacks on vulnerable organizations with critical information and data.
Threat Groups | APT Groups | |
|---|---|---|
|
|
|
How to detect Ryuk in your environment
Here are some types of IoCs that will alert you about malicious objects on endpoints:
Ryuk payload | SHA256: BDDAF6020F8DF169E1901C709701240F1A810D0E0FCEC7D4479D5354360E1795 Registry: HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run MD5: 795db7bdad1befdd3ad942be79715f6b0c5083d859901b81657b590c9628790f 501e925e5de6c824b5eeccb3ccc5111cf6e312258c0877634935df06b9d0f8b9 Fe909d18cf0fde089594689f9a69fbc6d57b69291a09f3b9df1e9b1fb724222b c0202cf6aeab8437c638533d14563d35 d348f536e214a47655af387408b4fca5 958c594909933d4c82e93c22850194aa 86c314bc2dc37ba84f7364acd5108c2b 29340643ca2e6677c19e1d3bf351d654 cb0c1248d3899358a375888bb4e8f3fe 1354ac0d5be0c8d03f4e3aba78d2223e cb0c1248d3899358a375888bb4e8f3fe d4a7c85f23438de8ebb5f8d6e04e55fc 3895a370b0c69c7e23ebb5ca1598525d 567407d941d99abeff20a1b836570d30 c0d6a263181a04e9039df3372afb8016 |
Ryuk-related IPs | 200[.]107[.]59[.]130:449 5[.]196[.]154[.]93 94[.]103[.]94[.]154 186[.]42[.]186[.]202:449 177[.]52[.]79[.]29:449 187[.]8[.]169[.]10:449 187[.]65[.]49[.]88:449 200[.]83[.]49[.]141:449 200[.]35[.]56[.]81:449 177[.]183[.]194[.]194:449 200[.]110[.]72[.]134:449 186[.]248[.]163[.]198:449 191[.]241[.]233[.]195:449 187[.]95[.]32[.]18:449 187[.]95[.]123[.]179:449 177[.]52[.]28[.]238:449 |
Ryuk-related file paths | c:\Windows\System32\setup.exe c:\Users\Default\AppData\Roaming\msnet\uetur.exe c:\Users\*\AppData\Roaming\msnet\uetur.exe c:\Users\*\AppData\Roaming\msnet c:\Windows\System32\config\systemprofile\AppData\Roaming\msnet\uetut.exe c:\Windows\System32\config\systemprofile\AppData\Roaming\msnet c:\Windows\System32\Tasks\Ms net |
Ryuk-related web files | /login/process.php /admin/get.php /news.php |
Today, Ryuk is being sold on the dark web in a ransomware as a service affiliate model business and it is empowering threat actors to go after vulnerable and critical entities like hospitals. Organizations need to recognize the threat, understand the risks, and prioritize preventions and measures that will protect them against Ryuk. Our researchers have spotlighted the threats that are influencing the growth of ransomware.


