
All About AvosLocker Ransomware
Surojoy Gupta
Securin Team


Feb 11, 2023
Originally Published: March 28, 2023
All About AvosLocker Ransomware
While not as prominent as REvil, LockBit or Conti, AvosLocker slowly made a name for itself by targeting critical infrastructure in different sectors of the US, Canada, UK and Spain in 2021. Since then, their clever use of conventional tactics and intermittent widespread attacks have made the ransomware variant still worth monitoring today.
AvosLocker ransomware affects a large number of users worldwide and usually targets computers of home, corporate and large organizational users running Microsoft Windows operating systems, including Windows XP, Windows 7, Windows 8, Windows 8.1, Windows 10, Windows Server 2003, and Windows Server 2008. It has been reported to have infected over 100,000 computers since mid-2021, making it one of the most dangerous ransomware strains currently in circulation.
Amongst the various techniques AvosLocker has been reported to use to spread itself, the use of email attachments, malicious links, malicious files, and exploiting known vulnerabilities in software, and even linking malicious advertisements on websites, expands their outreach tremendously.
The slow but steady activities of the group, and their capability to exploit across different OS environments prompted a warning from CISA under the #StopRansomware campaign in October 2023.
Interesting Trends
Let us look at some of the unique mannerisms of the group that make it a formidable threat.
- Choice of software: The AvosLocker group uses legitimate remote access tools to connect to victim machines. As the actors weaponize widely used software like AnyDesk, a remote desktop administration tool, antivirus software may not detect these implementations as malicious, allowing the group to easily circumnavigate defense measures. Operators can even manually operate and infect machines using such tools.
- Runs on Safe Mode: A key element of AvosLocker is being able to run itself on safe mode as part of its evasion tactics. This technique was previously employed by the now defunct REvil ransomware group. The attacker is able to restart the victim’s machines, disable specific drivers and run on safe mode, since most security measures cannot run on this mode. Often, the operators set up drivers to ensure AnyDesk can be run on safe mode as well.
- Auctioning Stolen Data: AvosLocker operators use another tactic borrowed from the REvil playbook in order to monetize a single successful attack or salvage a failed one–auctioning stolen data on its website on top of its double extortion scheme.
- Launching multiple versions of the same ransomware: The group released several versions of their ransomware, with the latest one being a Linux variant, launched in October 2021, that is capable of attacking ESXi virtual machines (VMs).
How does AvosLocker Attack
- The victim opens a malicious email that contains an infected file.
- When the user opens the attachment, a malicious script is run on the computer. This script downloads and executes the ransomware onto the computer. Once the ransomware is installed, it will begin to encrypt the user’s files and folders.
- AvosLocker ransomware uses polymorphic techniques to change its code to evade detection by antivirus software that may be installed on the victim’s computer. It also uses anti-debugging techniques to make it harder for researchers to analyze its code. Often, the ransomware group uses legitimate anti-debugging services to hide its malicious activities.
- Once the files are encrypted, a ransom note is displayed on the user’s computer, which demands a ransom payment in order to decrypt the files. The ransom note typically provides instructions on how to pay the ransom and may include links to a payment website. The ransom note may also contain threats to delete the user’s files if the ransom is not paid.
- In addition to encrypting files, the AvosLocker ransomware also attempts to delete system restore points, shadow copies, and any backups that the user may have. This prevents the user from recovering their files without paying the ransom.
AvosLocker Vulnerabilities
Securin experts identified a set of 15 vulnerabilities associated with AvosLocker. Let us take a closer look at the vulnerabilities.
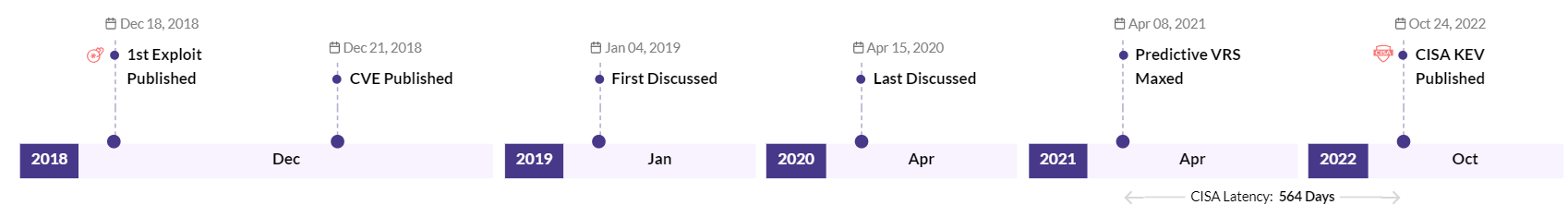
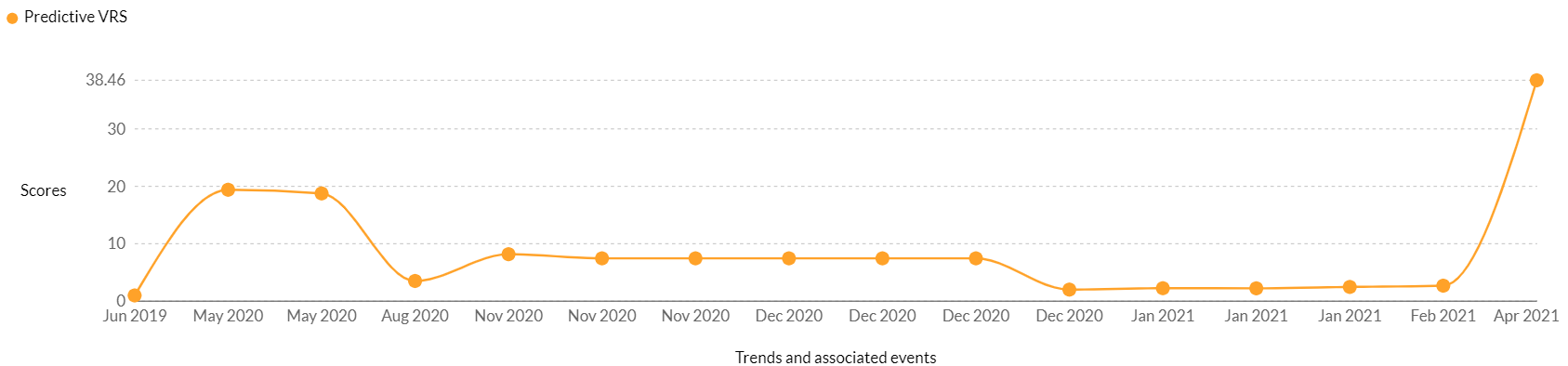
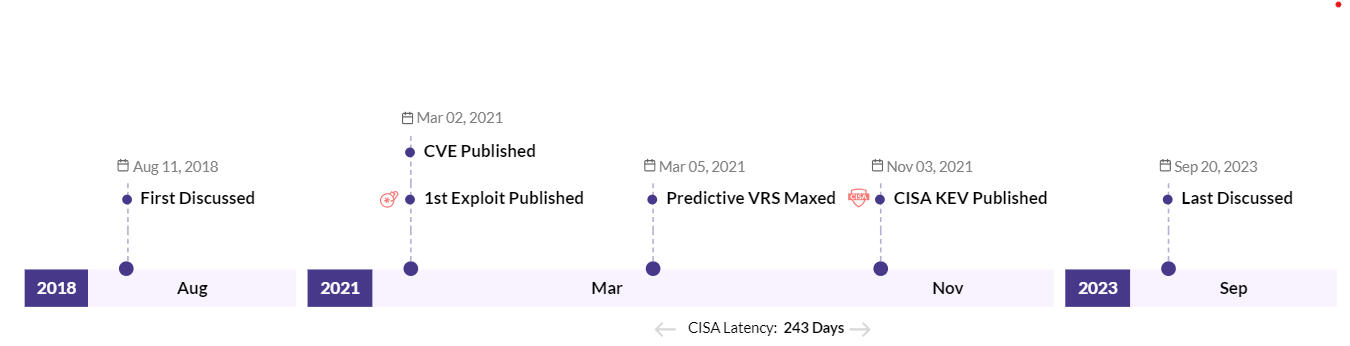
1. CVE-2018-19320 – The GDrv low-level driver in GIGABYTE APP Center v1.05.21 and earlier, AORUS GRAPHICS ENGINE before 1.57, XTREME GAMING ENGINE before 1.26, and OC GURU II v2.08; could allow a local attacker to take complete control of the affected system.
Trending | CISA KEV | 3 Ransomware AssociationsCVSS v2 – 7.20, CVSS v3- 7.80, Securin VRS – 8.66
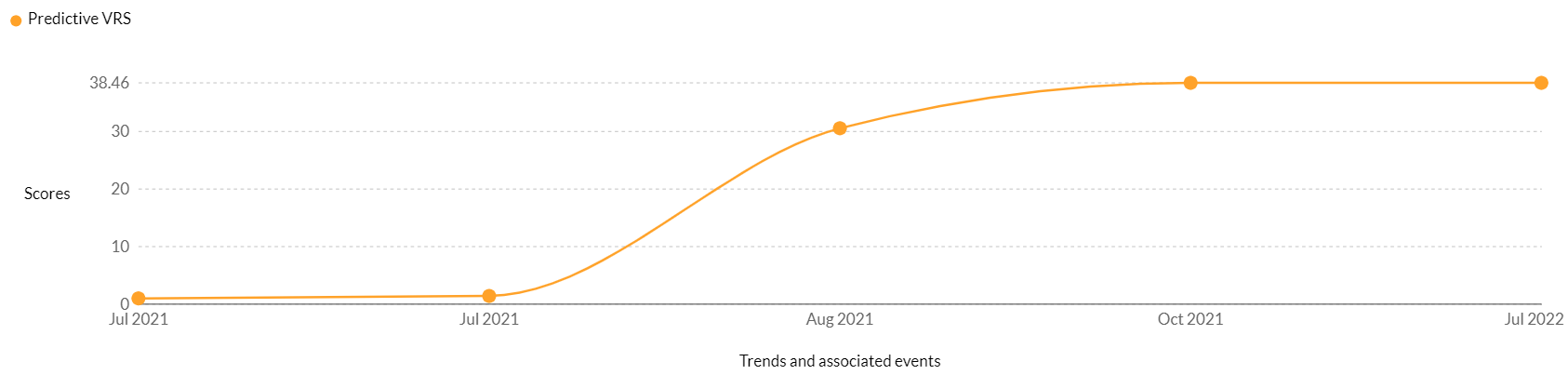
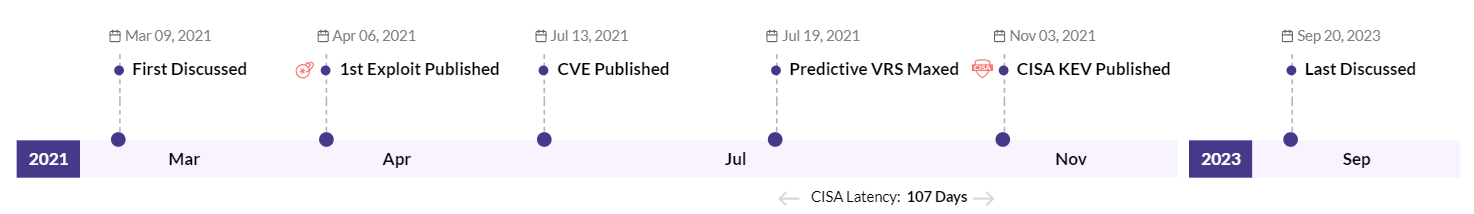
Trending | CISA KEV| 10 Ransomware Associations | 14 APT AssociationsCVSS v2 – 9.30, CVSS v3 – 10.00, Securin VRS – 10
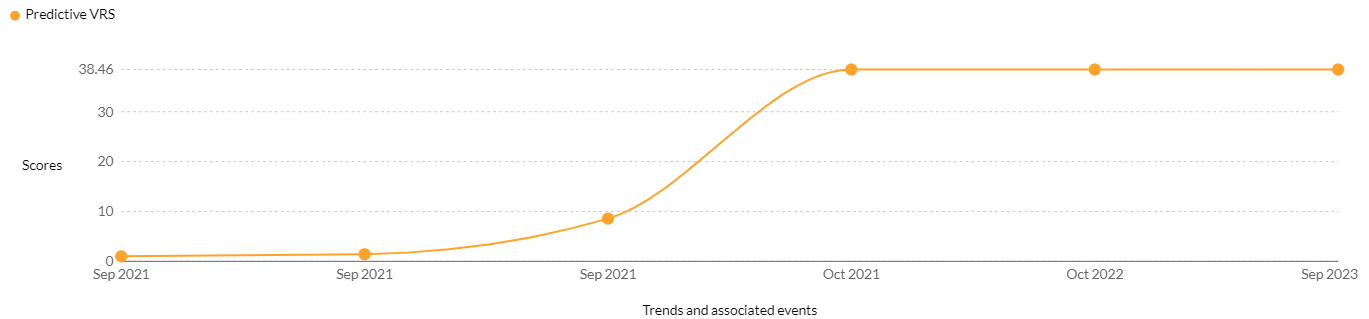
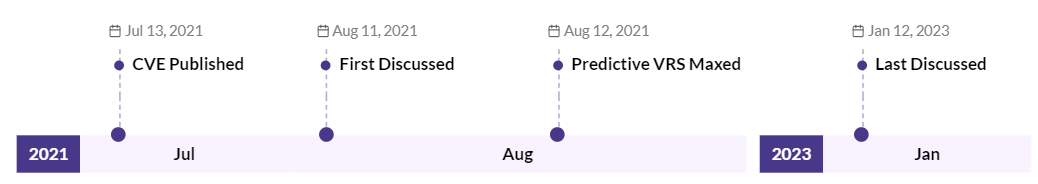
Trending | 1 Ransomware Association | 1 APT AssociationCVSS v2 – 4.30, CVSS v3 – 5.90, Securin VRS – 7.86

Trending | CISA KEV | 1 Ransomware Association | 3 APT AssociationsCVSS v2 -5.10, CVSS v3 – 9.00, VRS – 8.19
Trending | 1 Ransomware Association | 2 APT AssociationsCVSS v2 – 8.50, CVSS v3 – 6.60, Securin VRS – 7.45

Trending | CISA KEV | 9 Ransomware Associations | 17 APT AssociationsCVSS v2 – 7.50, CVSS v3 – 9.1. VRS – 9.91
Trending | CISA KEV | 14 Ransomware Associations | 9 APT AssociationsCVSS v2 – 6.5, CVSS v3 – 6.6, Securin VRS – 8.44

Trending | CISA KEV | 13 Ransomware Associations | 12 APT AssociationsCVSS v2 – 10, CVSS v3 – 9.1, Securin VRS – 9.91
Trending | CISA KEV | 13 Ransomware Associations | 10 APT AssociationsCVSS v2 – 7.5, CVSS v3 – 9, VRS – 9.51
Trending | CISA KEV | 2 Ransomware Associations | 2 APT AssociationsCVSS V2 – 7.5, CVSS v3 – 9.8, Securin VRS – 9.98
Trending | 1 Ransomware AssociationCVSS V2 – 7.9, CVSS v3 – 7.6, Securin VRS – 8.47
Trending | CISA KEV | 2 Ransomware Associations | 6 APT AssociationsCVSS V2 – 7.5, CVSS v3 – 9.8, Securin VRS – 9.96
Trending | CISA KEV | 2 Ransomware AssociationsCVSS V2 – 7.5, CVSS v3 – 8.1, Securin VRS – 9.52
Trending | CISA KEV | 2 Ransomware AssociationsCVSS V2 – 7.5, CVSS v3 – 9.8, Securin VRS – 9.98
Trending | CISA KEV | 2 Ransomware AssociationsCVSS V2 – 9, CVSS v3 – 8.8, Securin VRS – 9.6
Trending | CISA KEV | 2 Ransomware AssociationsCVSS V2 – 10, CVSS v3 – 9.8, Securin VRS – 9.96
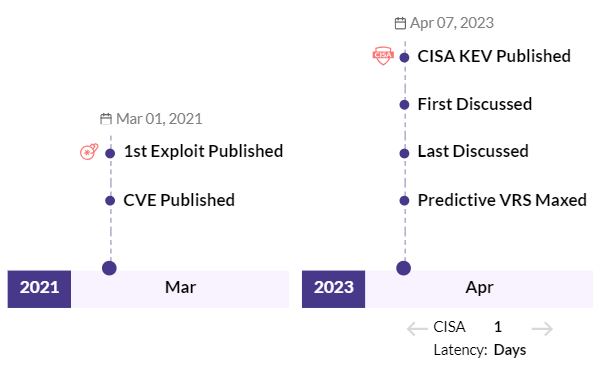
Trending | CISA KEV | 2 Ransomware AssociationsCVSS V2 – 6.5, CVSS v3 – 8.8, Securin VRS – 8.46
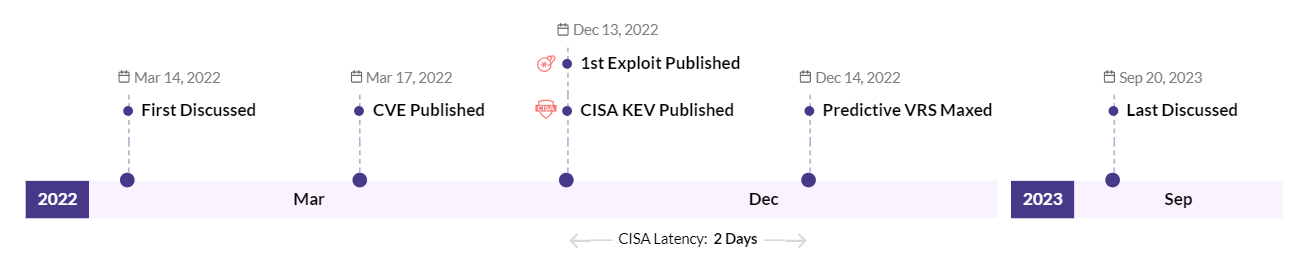
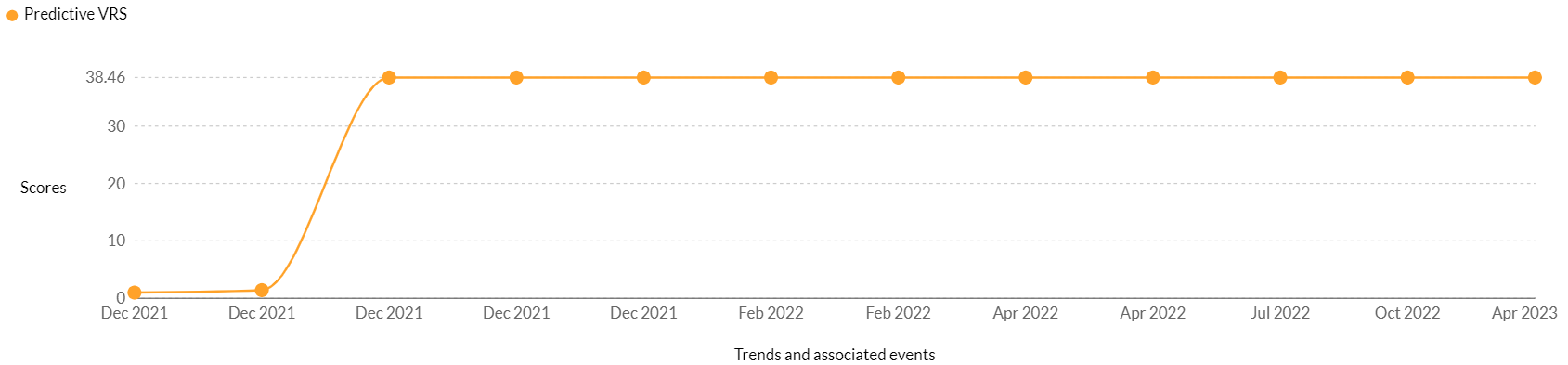
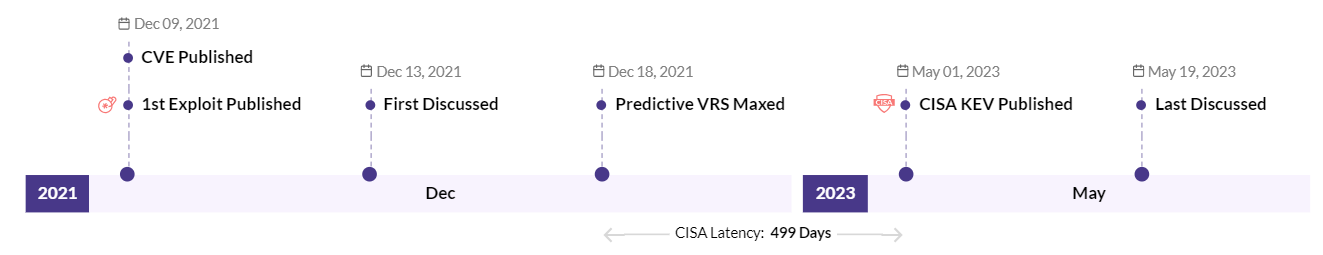
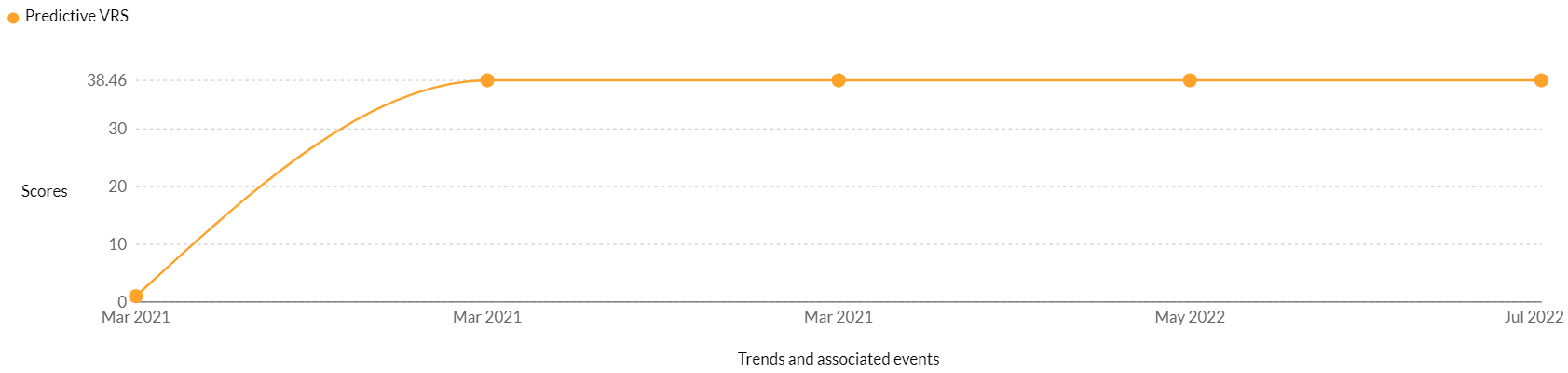
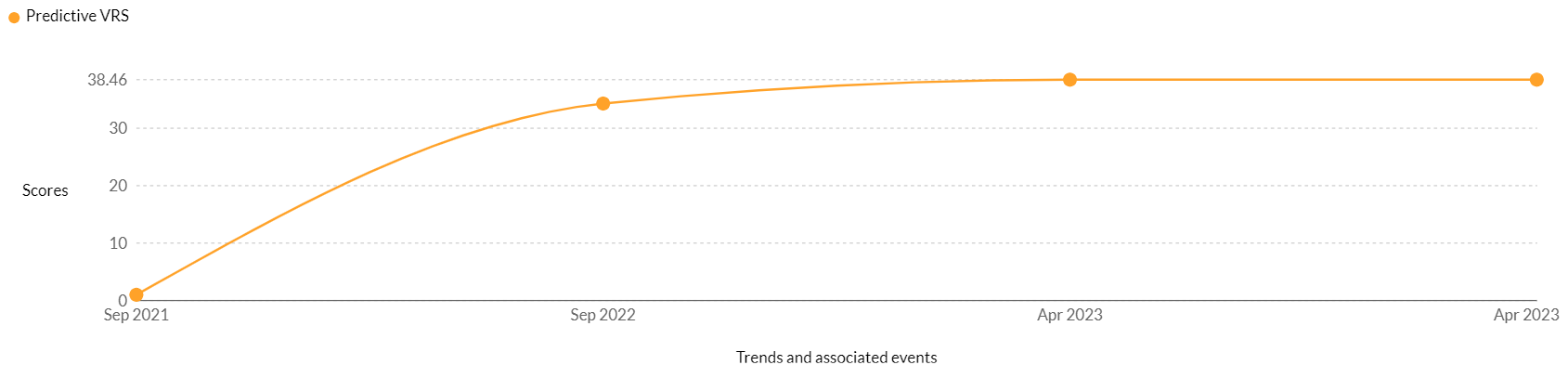
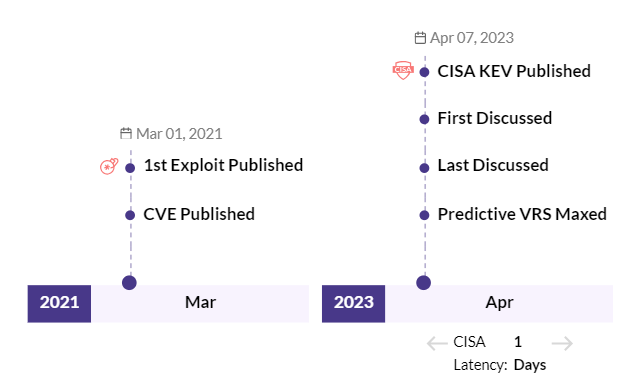
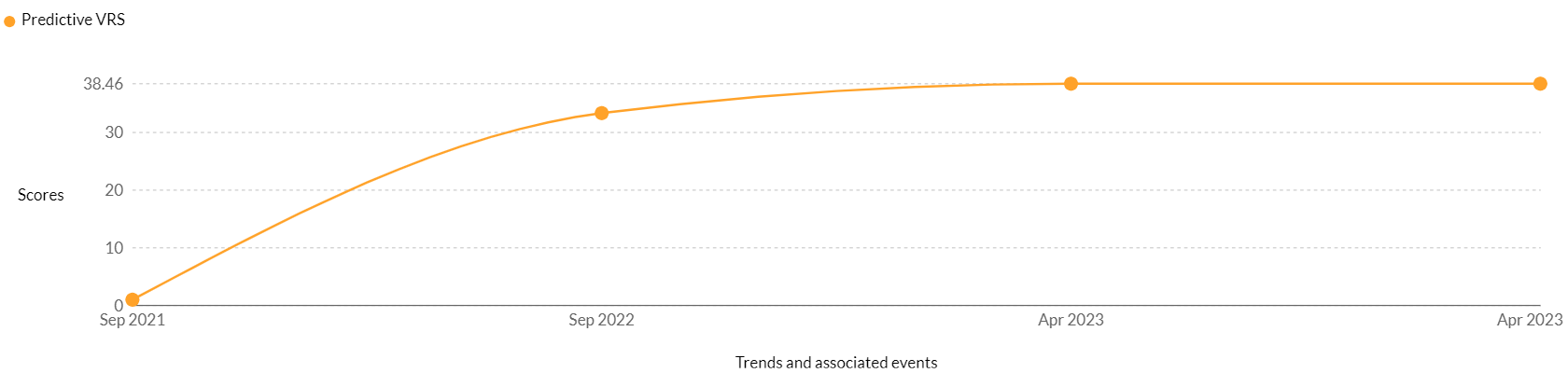
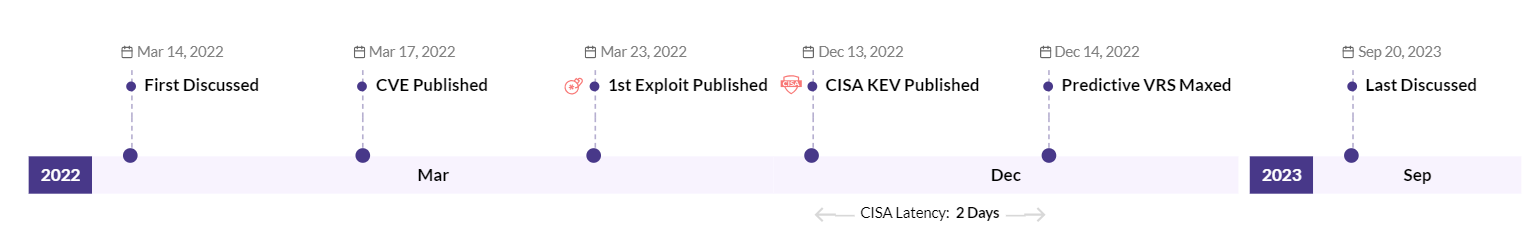
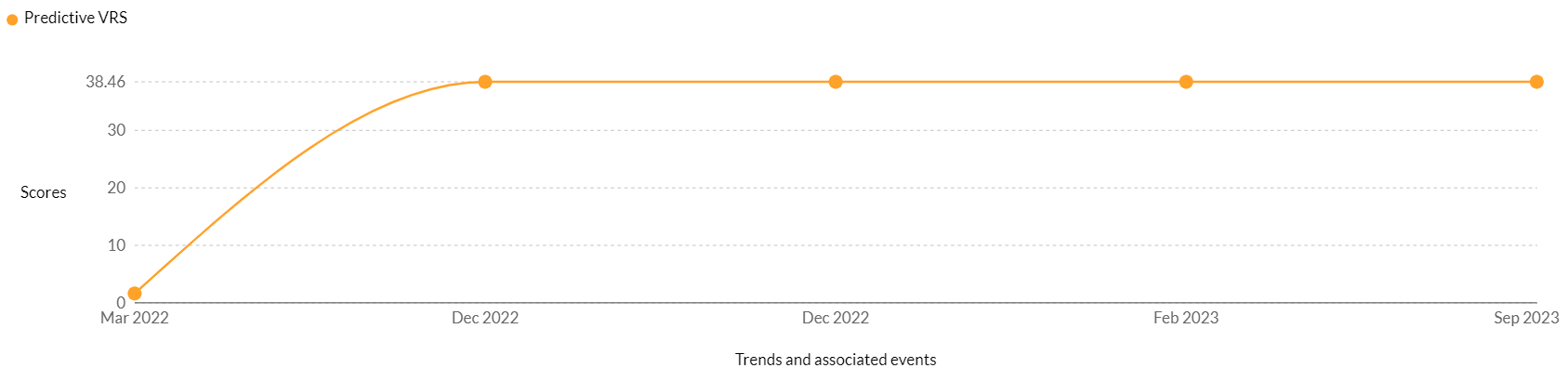
CVE-2021-44228: A high-risk vulnerability rated critical in CVSS V3 (10) exists in Apache Log4j. This vulnerability exists in 176 products from 21 vendors. Notable among them are vendors such as Oracle, Red Hat, Apache, Novell, Amazon, Cisco, SonicWall, and others. This RCE vulnerability is exploited by six ransomware gangs: AvosLocker, Conti, Khonsari, Night Sky, Cheerscrypt, and TellYouThePass. This vulnerability, too, is a point of interest for hackers and has been trending since December 2022, which is probably why CISA has included it as part of the CISA KEV catalog.
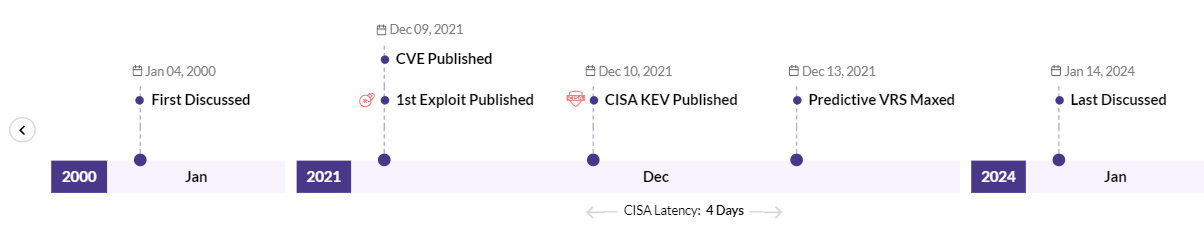
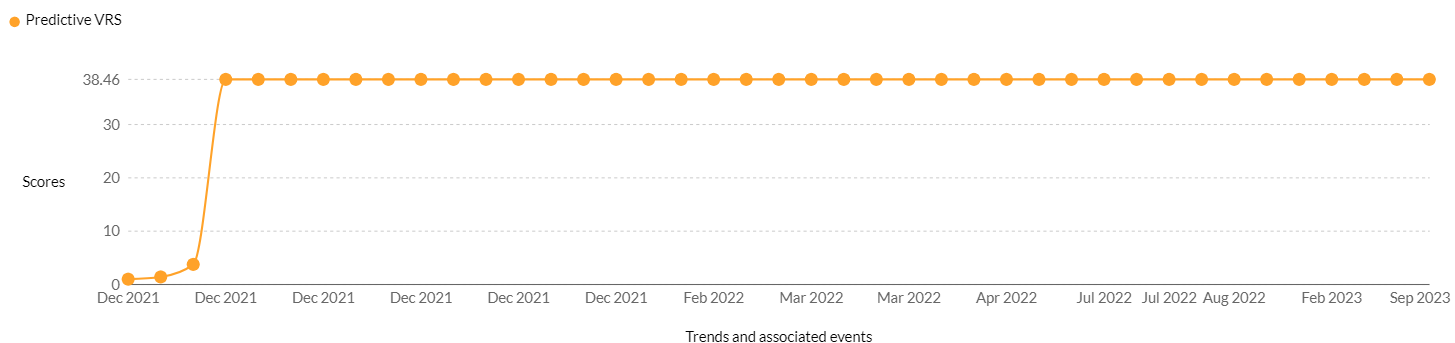
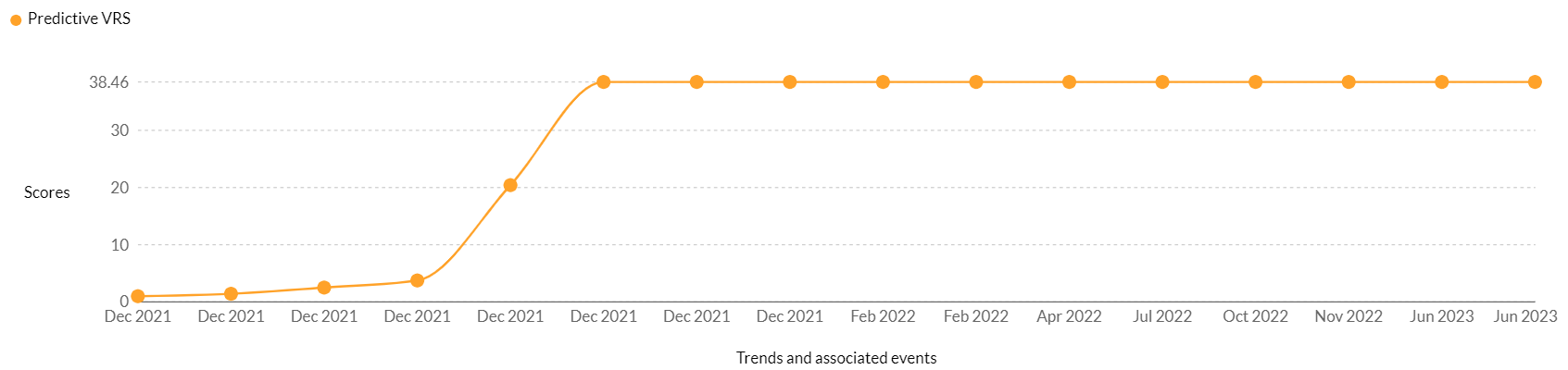
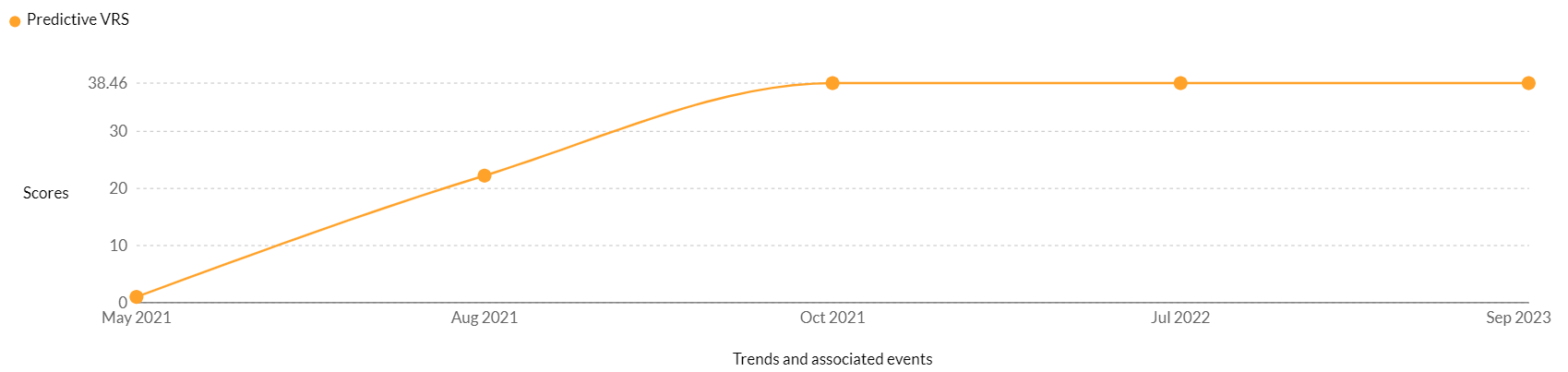
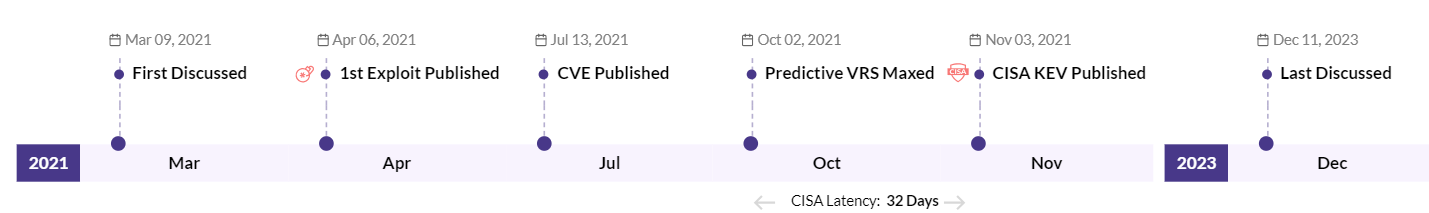
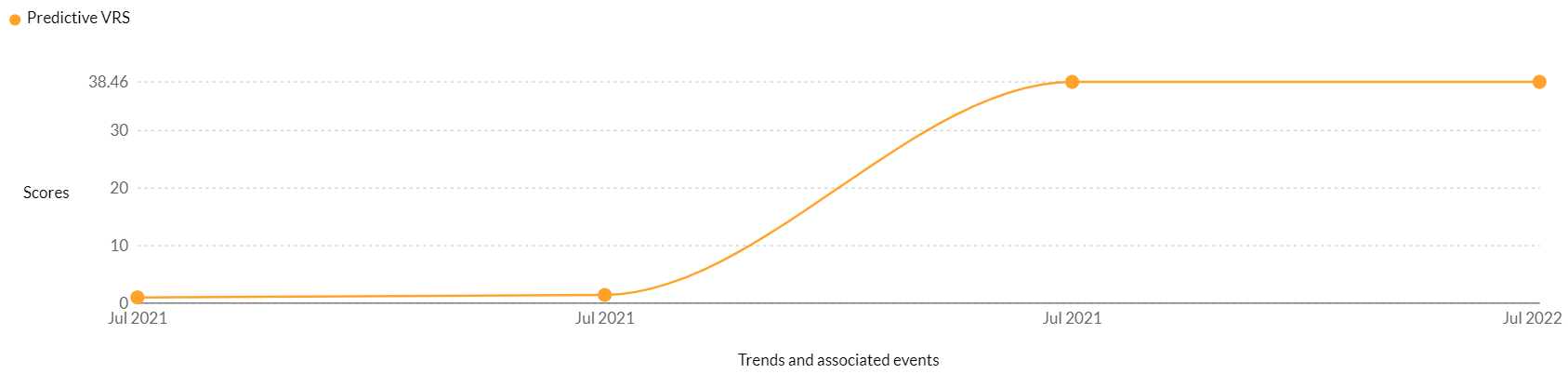
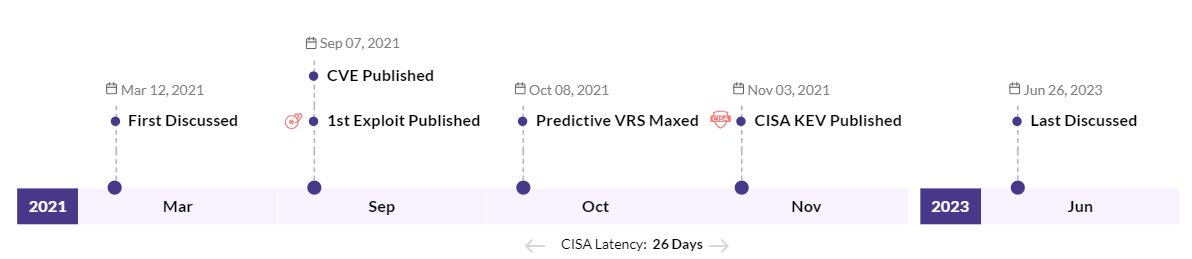
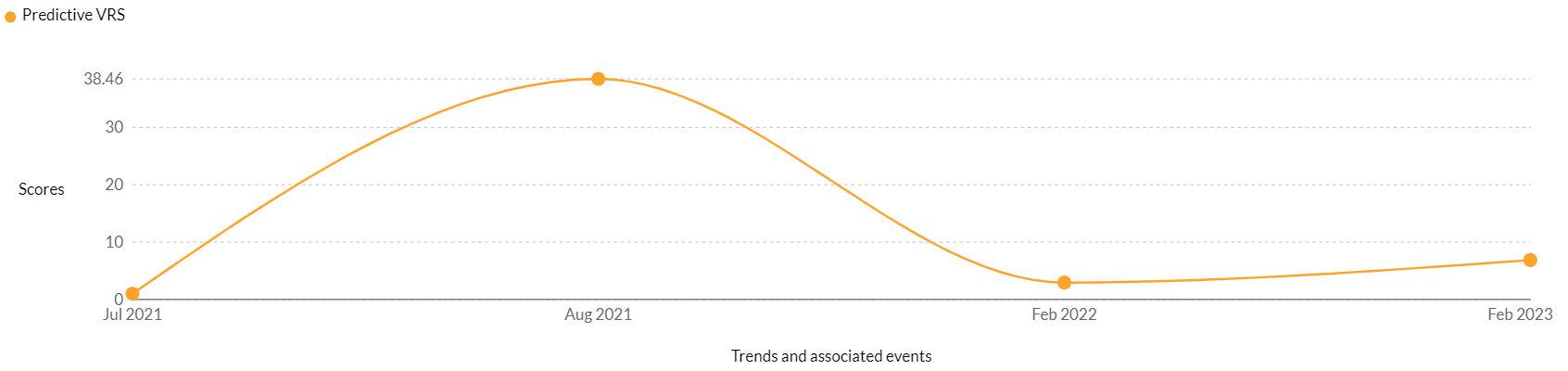
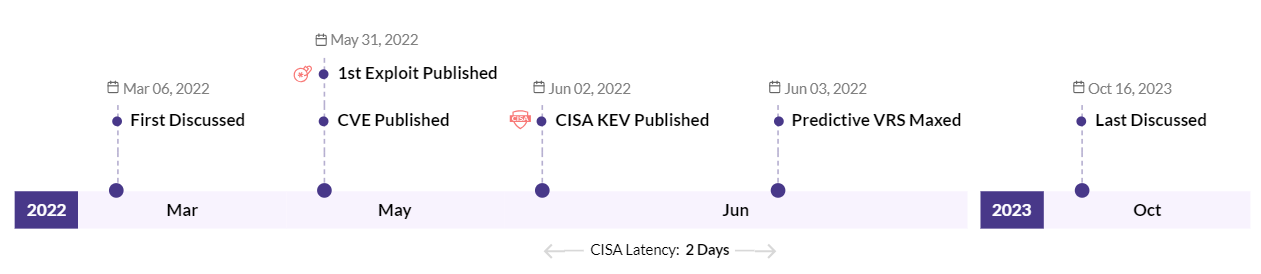
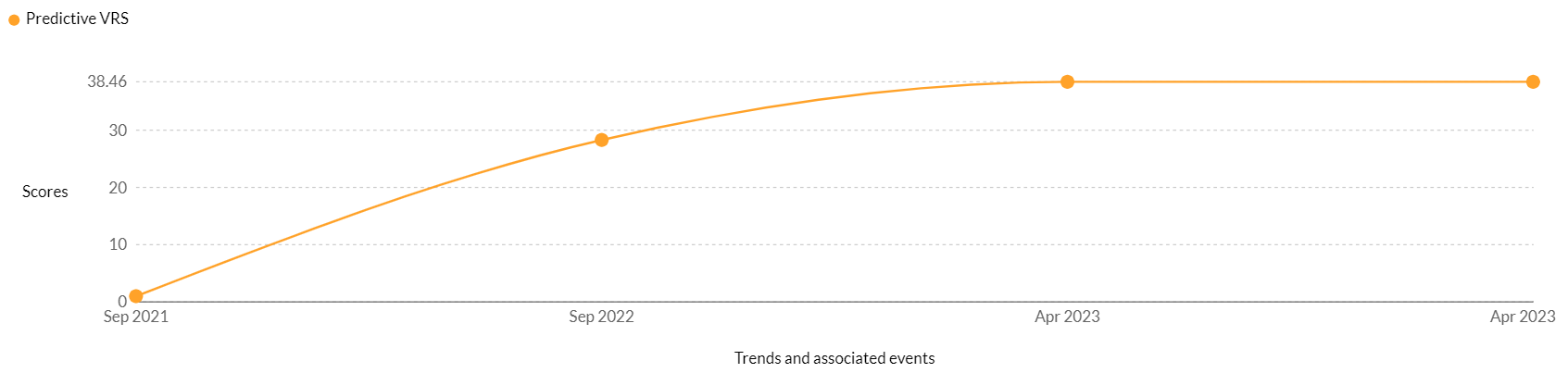
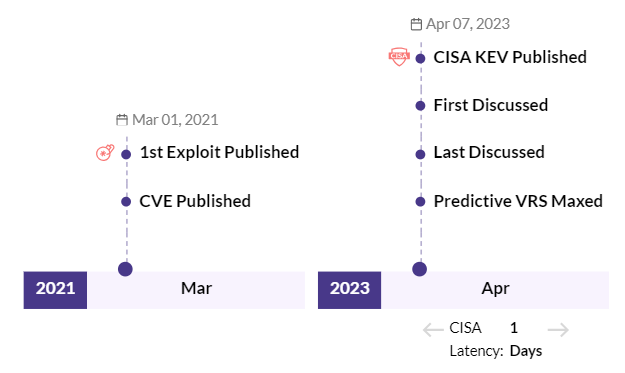
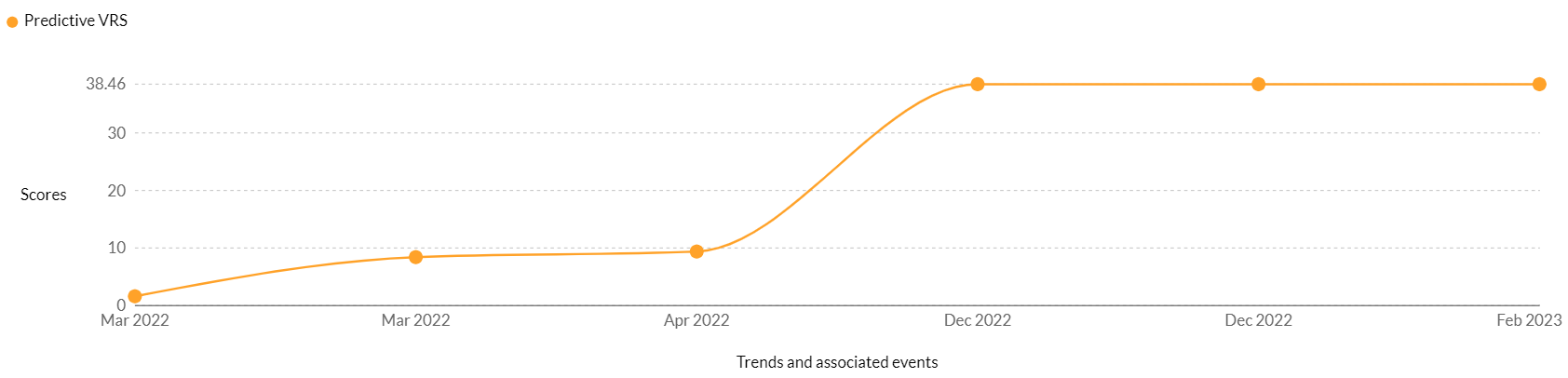
CVE-2021-45046: This high-risk vulnerability is rated critical in CVSS V3 (9), and it exists in 16 vendors and 93 products. Notable among the vendors that are vulnerable to this CVE are Intel, Apache, NetApp, Red Hat, and many others. This vulnerability was newly associated with the AvosLocker ransomware in 2022 and has been trending since December 12, 2022. While our researchers have been tracking this vulnerability as a threat since December 2021, it was added to the CISA KEVs more than a year later, in March 2023.
Attack Methodology
- The victim opens a malicious email that contains an infected file.
- When the user opens the attachment, a malicious script is run on the computer. This script downloads and executes the ransomware onto the computer. Once the ransomware is installed, it will begin to encrypt the user’s files and folders.
- AvosLocker ransomware uses polymorphic techniques to change its code to evade detection by antivirus software that may be installed on the victim’s computer. It also uses anti-debugging techniques to make it harder for researchers to analyze its code. Often, the ransomware group uses legitimate anti-debugging services to hide its malicious activities.
- Once the files are encrypted, a ransom note is displayed on the user’s computer, which demands a ransom payment in order to decrypt the files. The ransom note typically provides instructions on how to pay the ransom and may include links to a payment website. The ransom note may also contain threats to delete the user’s files if the ransom is not paid.
- In addition to encrypting files, the AvosLocker ransomware also attempts to delete system restore points, shadow copies, and any backups that the user may have. This prevents the user from recovering their files without paying the ransom.
AvosLocker MITRE Map and IoCs
Initial Access | T1190 Exploit public-facing application T1078 Valid accounts |
Execution | T1059 Command and scripting interpreter T1072 Software deployment tools |
Persistence | T1136 Create account T1547 Boot or logon autostart execution |
Defense Evasion | T1112 Modify registry T1562 Impair defenses T1140 Deobfuscate/Decode files or information T1070 Indicator removal on host |
Credential Access | T1003 OS credential dumping T1552 Unsecured credentials T1555 Credentials from password stores |
Discovery | T1083 File and directory discovery T1135 Network share discovery T1057 Process discovery T1018 Remote system discovery |
Lateral Movement | T1021 Remote services T1072 Software deployment tools |
Command and Control | T1219 Remote access software |
Impact | T1436 Data encrypted for impact T1489 Service stop T1490 Inhibit system recovery T1491 Defacement |
Indicators of Compromise
Key | Value |
Platform | WindowsLinuxEXSi |
Language | C++ |
Encrypting Algo’s | RSAAES-256(Toencryptfiles)ChaCha20Algofencry ptencrypteddata |
Mutex Name | ievah8eVki3Ho4oo |
API’s | WebshellMoveFileWRMStartSessionRmRegisterResourcesRmGetList(toaccessthefilesfencryption)WNetOpenEnumAWNetEnumResourceA WNetAddConnection2A(toenumerateencryptthenetwkresources) |
DLL’s | api-ms-win-ce-datetime-l1-1-1api-ms-win-ce-file-l1-2-2api-ms-win-ce-localization-l1-2-1api-ms-win-ce-localization-obsolete-l1-2-0api-ms-win-ce-processthreads-l1-1-2api-ms-win-ce-string-l1-1-0api-ms-win-ce-sysinfo-l1-2-1api-ms-win-ce-winrt-l1-1-0api-ms-win-ce-xstate-l2-1-0api-ms-win-security-systemfunctions-l1-1-0ext-ms-win-ntuser-dialogbox-l1-1-0ext-ms-win-ntuser-windowstation-l1-1-0api-ms-win-appmodel-runtime-l1-1-2 |
AvosLocker Using Tools to Access Device/Host | CobaltStrikeEncodedPowerShellscripts(publiclyavailabletool)PuTTYSecureCopyclienttool“pscp.exe”RcloneAnydeskScannerAdvancedIPscannerWinListerChiselPDQDeploy(PDQDeploytopushoutWindowsbatchscriptstomachinestheyplannedtotarget.) |
Affected File Extensions | ndoc, docx, xls, xlsx, ppt, pptx, pst, ost, msg, eml, vsd, vsdx, txt, csv, rtf, wks, wk1, pdf, dwg, onetoc2, snt, jpeg, jpg, docb, docm, dot, dotm, dotx, xlsm, xlsb, xlw, xlt, xlm, xlc, xltx, xltm, pptm, pot, pps, ppsm, ppsx, ppam, potx, potm, edb, hwp, 602, sxi, sti, sldx, sldm, sldm, vdi, vmdk, vmx, gpg, aes, ARC, PAQ, bz2, tbk, bak, tar, tgz, gz, 7z, rar, zip, backup, iso, vcd, bmp, png, gif, raw, cgm, tif, tiff, nef, psd, ai, svg, djvu, m4u, m3u, mid, wma, flv, 3g2, mkv, 3gp, mp4, mov, avi, asf, mpeg, vob, mpg, wmv, fla, swf, wav, mp3, sh, class, jar, java, rb, asp, php, jsp, brd, sch, dch, dip, pl, vb, vbs, ps1, bat, cmd, js, asm, h, pas, cpp, c, cs, suo, sln, ldf, mdf, ibd, myi, myd, frm, odb, dbf, db, mdb, accdb, sql, sqlitedb, sqlite3, asc, lay6, lay, mml, sxm, otg, odg, uop, std, sxd, otp, odp, wb2, slk, dif, stc, sxc, ots, ods, 3dm, max, 3ds, uot, stw, sxw, ott, odt, pem, p12, csr, crt, key, pfx, der, dat |
AvosLocker Encrypted Files Extension | .avos.avos2AvosLinux |
Batch Scripts of AvosLocker | execute.batLove.batUpdate.batlock.bat |
Virus Names to be Used by Avoslocker | Ransom:MSIL/ApisCrypt.PAA!MTBTrojan-Banker.Win32.NeutrinoPOS.bnqMSIL/Filecoder.NR |
Sites | |
Note File after Encryption | GET_YOUR_FILES_BACK.txt(windows)README_F_RESTE.txt(Linux) |
Hash 256 | cdca6936b880ab4559d3d96101e38f0cf58b87d07b0c7bf708d078c2bf2094600cd7b6ea8857ce827180342a1c955e79c3336a6cf2000244e5cfd4279c5fc1b610ab76cd6d6b50d26fde5fe54e8d80fceeb744de8dbafddff470939fac6a98c4e9a7b43acdddc3d2101995a2e2072381449054a7d8d381e6dc6ed64153c9c96ae737c901b80ad9ed2cd800fec7c2554178c8afab196fb55a0df36acda1324721cdca6936b880ab4559d3d96101e38f0cf58b87d07b0c7bf708d078c2bf2094607c935dcd672c4854495f41008120288e8e1c144089f1f06a23bd0a0f52a544b1a0b4e3d7e4cd20d25ad2f92be954b95eea44f8f1944118a3194295c5677db74943b7a60c0ef8b4af001f45a0c57410b7374b1d75a6811e0dfc86e4d60f5038567731a9e1e5fff9d912b1d238dcd92c2ba671a5ea55441bb7f14b05ed40039ce1794f3d25c42d383fad485f9af1d6d7c0508bcfe8ed80a1afea0e0b51bf92bc81a58864dd006f0528f890c9e000e660f65ffe041ebd2bcb45903fb0228321cfb205ba2df0033e3cd5b987d66b6de545df439d338a20165c0ba96cde8a74e463e5C0A42741EEF72991D9D0EE8B6C0531FC19151457A8B59BDCF7B6373D1FE56E026584cd273625ee121e330a981cc04e1f1d312356c9cccdb62932ea7aad53a731da6e60b4e39c6c556836a18a09a52cd83c47f9cf6dc9e3ad298cbcb925a62a96373a791f058539d72983e38ebe68e98132fcf996d04e9a181145f22a96689386fc55f8b61cb79f2b85b8bf35ff1b80f49fc61a860aca7729f35449df4928cd9b0c50992b87ba354a256dfe4356ffa98c8bc5dd231dab0a4dc64413741edb739b5b7bed7349f6b1499b7eac111d7264101b13eeb9684830a4a93bab5f9d79d77ebe19681b21f2a573b477444a788e00eb8dad2d740d11c02f14e878fe5b89fa7033203ecb5c34c45dacf64c42c3a24cd4aeb2ceb26b0c58ba97fc8f33319da91b3b58516758466c8129c4899f07e1e50ca98d913f7c13665aa446c75325b7c5d8 |
Hash SHA 1 | 05c63ce49129f768d31c4bdb62ef5fb53eb41b546f110f251860a7f6757853181417e19c28841eb49c8f5c136590a08a3103ba3e988073cfd5779519e8c26db068914df2083512ff8b24a2cc803ea498dab33aaf01322e88f79ffddcbc95d1ad9ad97374e60ef891027ac1dade9562f8b1de866186338da167f0c8d81aefcfc5943b31d695972194ac15e9f22f3273e5b6739b844fe33f7310476afb971956ddf6f94e2f49cd64a9590963ef3852e135e2b8deba |
Hash MD5 | e09183041930f37a38d0a776a63aa673d3cafcd46dea26c39dec17ca132e5138f659d1d15d2e0f3bd87379f8e88c6b42afed45cd85a191fe3b2543e3ae6aa81131f8eedc2d82f69ccc726e012416ce33a39b4bea47c4d123f8195a3ffb638a1b504bd1695de326bc533fde29b8a69319eb45ff7ea2ccdcceb2e7e14f9cc01397d285f1366d0d4fdae0b558db690497eacf0c2513b6e074267484d204a1653222 |
AvosLocker Service Name | Ransom.Win32.AVOSLOCKER.SMYXBLNTRansom.Win32.AVOSLOCKER.YPBLU |
Prevent Ransomware Attacks by Securing Your Attack Surface
Safeguarding networks against threats such as the AvosLocker ransomware requires a proactive and multi-faceted approach. By implementing robust cybersecurity practices, staying informed about the latest threats, and maintaining a diligent backup strategy, you can significantly reduce the risk of falling victim to this malicious software.
Remember to regularly update your operating system and software, use reliable antivirus programs, and exercise caution when clicking on links or downloading attachments. Additionally, fostering a culture of cybersecurity awareness within your organization or among your peers is crucial for creating a collective defense against ransomware attacks.
Worried about ransomware vulnerabilities in your network?
Talk with our experts to identify weak-points and vulnerabilities.


