
AI & Ransomware VS. The Financial Sector
Shireen Pereira
Securin Team


Dec 4, 2025
As we move into 2026, ransomware remains one of the most dangerous cyber threats and the focus of defenses. Naturally, ransomware is now supercharged by AI on both sides of the fight. While enterprises leverage AI for faster detection and response, attackers are using it to create polymorphic malware, more effective phishing campaigns, and more lethal exploit chains. The net impact is that attacks are scaling faster than defenses can adapt.
Securin has tracked and studied trends in ransomware activity over the past twenty years. Securin’s research indicates that all major groups have become increasingly sophisticated since 2024, with LockBit remaining the most dominant. Further, we have seen the emergence of RansomAI—a new category of ransomware powered by AI that adapts in real time. RansomAI is an AI agent or framework that uses reinforcement learning to evade detection and become more effective. In controlled tests, it evaded detection in approximately 90% of cases by encrypting data, using shifting encryption methods, automating attack sequences, and intelligently evading security checks.
Amid this shift, financial services have become a prime target because they hold vast repositories of sensitive personal and transactional data, offer high liquidity for quick monetization of breaches, and yield high ransoms due to regulations and disruption risks. According to Securin’s 2024 Ransomware Index Report, the sector suffered 5.2% of all ransomware incidents—a small slice with massive consequences: $5.68 million in average direct losses (IBM). Combined with tightening scrutiny from the Securities and Exchange Commission (SEC) and the velocity of AI-driven attacks, finance now sits at the epicenter of an accelerating cyber risk storm.
How Ransomware Gets Into Financial Organizations
In the report, Securin observed that ransomware actors gained initial access to financial institutions primarily through exploiting public-facing applications, stolen credentials, and remote management tools. The ConnectWise ScreenConnect vulnerability became a near-universal entry point. It was exploited by LockBit, Black Basta, and BlackCat, three of the most notorious ransomware gangs in the world, within 72 hours of disclosure. This entry point granted attackers domain-level access through a single unpatched help desk instance.
Today, AI has made it easier for ransomware to get into financial organizations, enabling even inexperienced actors to deploy advanced payloads. FunkSec—an emerging group using AI to accelerate its operations—illustrates how rapidly this shift is unfolding. Despite having little prior experience, the group claimed more than 100 victims within months by combining double-extortion tactics with AI-generated malware. This allowed FunkSec to achieve an operational efficiency previously associated only with top-tier ransomware syndicates, such as LockBit and Cl0p.
At the core of this evolution was EGAN (Evolutional Generative Adversarial Network;)an adaptive AI model that allowed malware to learn, evolve, and evade defenses in real time.
As Dr. Srinivas Mukkamala, Securin’s CEO, noted:
With these new adversarial tools that both lowered the need for expertise in adversaries and increased their sophistication, it’s no wonder that financial institutions are seeing increasing rates of ransomware. This trend is likely to increase over time.
Exploiting the Weakest Links
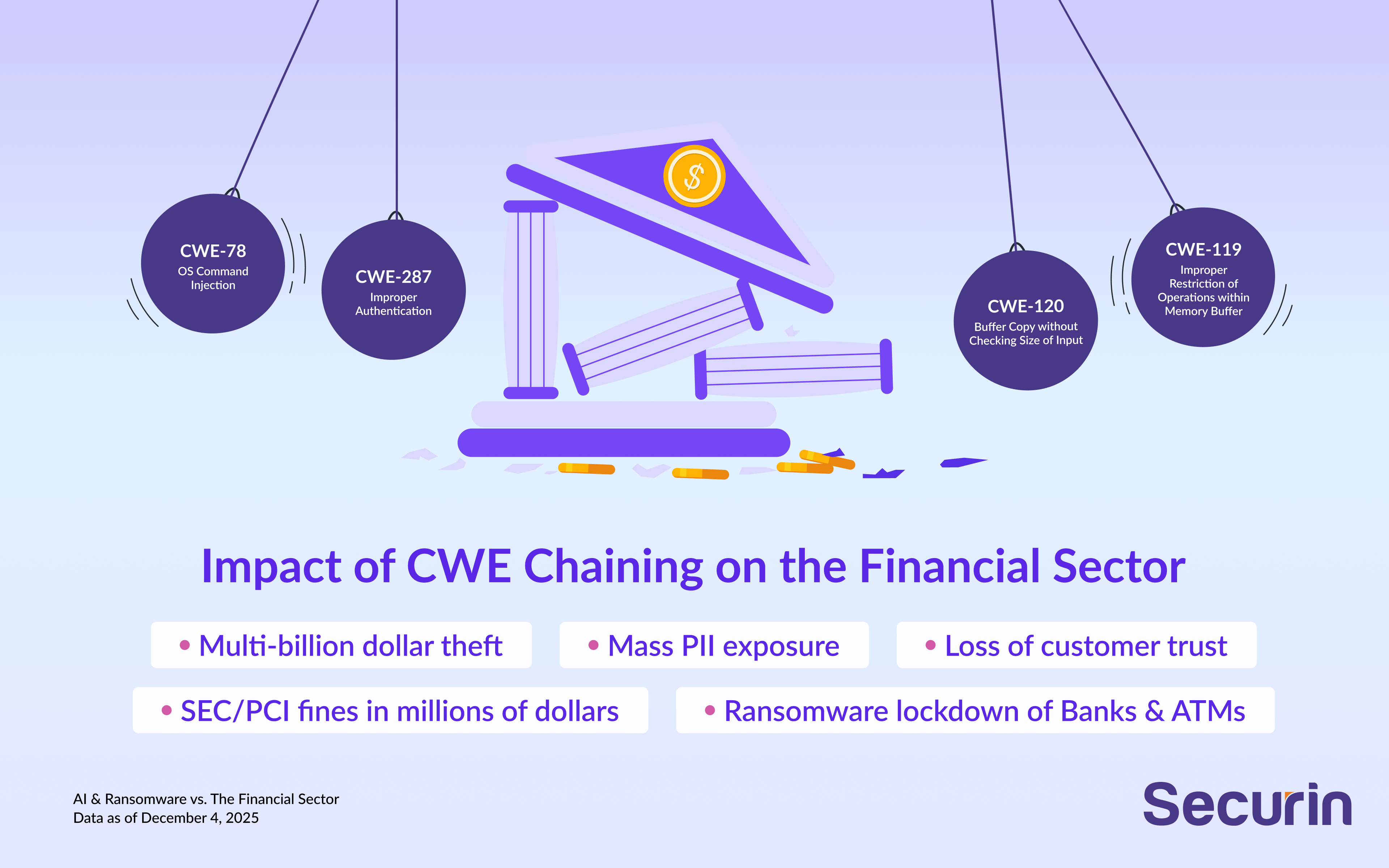
In January 2024, the BlackCat (ALPHV) ransomware attack on LoanDepot—a major U.S. mortgage lender—exposed the severe consequences of exploited weaknesses in financial services. The attack encrypted critical systems, disrupted payment operations, and compromised the sensitive data of 16.6 million customers. It resulted in approximately $41 million in recovery costs, a $70 million quarterly loss, and an estimated $25 million class-action lawsuit. This incident underscores why Known Exploited Vulnerabilities (KEVs) demand focused attention, as they have already been successfully leveraged in real-world attacks. However, “weakness chaining” of just two to four weaknesses often enables an exploit that flies under the radar of most cybersecurity tools. Securin’s analysis of 2024’s most exploited weaknesses reveals that Improper Authentication (CWE-287) and Authentication Bypass (CWE-288) remain the soft underbelly of enterprise defense. Memory errors like Buffer Overflows (CWE-119, CWE-787) and design flaws such as Incorrect Default Permissions (CWE-276) also continue to fuel attacks.
Impact of CWE Chaining on the Financial Sector
When attackers chain major exploits, the financial sector can face catastrophic, sector-wide consequences in minutes.
• Instant multi-billion $ theft - unauthorized access to customer accounts
• Mass PII exposure → identity theft epidemic
• Ransomware lockdown of banks/ATMs
• Trading platform takeover → market manipulation
• Permanent loss of customer trust/reputation
• SEC/PCI fines in millions of dollars
Emerging vectors such as cross-prompt injection attacks allow adversaries to manipulate model inputs for unauthorized actions. Microsoft’s red team proved that large language models can be coerced into generating malicious output or automating scams when paired with speech technologies. Meanwhile, legacy flaws like Server-Side Request Forgery (SSRF) persist, amplified by complex AI architectures.
Securin’s analysis also revealed a critical disconnect between theoretical and real-world risk. When comparing MITRE’s 2024 Top 25 CWE list with active exploitation data, major discrepancies emerged. Vulnerabilities that ranked low—or were entirely missing from MITRE’s framework—such as Memory Buffer Operations and Improper Input Validation, were among the most weaponized in active ransomware. Organizations that fail to recognize this gap could prioritize the wrong weaknesses, creating blind spots attackers can easily exploit. . To overcome this disconnect, organizations should pair traditional frameworks with real-time exploitation intelligence to focus on the weaknesses ransomware gangs actually use.
AI Defense For the Financial Sector
Traditional patching and perimeter models cannot keep pace with AI-driven, financially motivated attacks. Financial security leaders must now integrate AI-aware, intelligence-led resilience into their risk frameworks.
Securin recommends seven defense priorities for financial institutions:
- Enforce Strong Authentication: Implement Multi-Factor Authentication (MFA) and Privileged Access Management (PAM) across all systems and apply Zero Trust to vendor access.
- Enhance Memory & Endpoint Protection:Strengthen your systems by using Endpoint Detection and Response (EDR) to spot suspicious behavior and block attacks before it spreads..
- Prioritize Real-World Exploits: Move beyond Common Vulnerability Scoring System (CVSS)—use threat intelligence and Common Vulnerabilities and Exposures (CVE) chaining data to focus on what attackers actually use.
- Adopt APT-Focused Detection: Deploy threat hunting, deception tools, and continuous monitoring to detect lateral movement.
- Harden Recovery Systems: Maintain immutable backups and test ransomware drills under financial continuity scenarios.
- Secure AI Pipelines: Protect model data, restrict access, and monitor for prompt injection risks in AI-driven operations.
- Align with Regulatory Readiness: Integrate cybersecurity metrics into risk reporting for compliance with the SEC, Federal Financial Institutions Examination Council, and the Office of the Comptroller of the Currency.
Ransomware in the Financial Future
Ransomware groups are increasingly targeting and exploiting financial institutions on account of their critical data holdings and high ransom payment potential. As Securin’s research shows, these attacks have evolved into AI-enhanced, multi-stage operations that combine automation, intelligence, and timing with precision. Emerging frameworks like RansomAI can now learn and adapt in real time, turning ransomware into an autonomous, self-optimizing threat.
These patterns reflect a sobering reality: ransomware groups now operate with APT discipline—performing reconnaissance, mapping transaction flows, and timing attacks to coincide with high-value financial events.
To stay ahead, financial organizations must follow the best practices outlined above and ensure complete attack surface visibility, including third-party systems and AI integrations.Securin has helped numerous organizations in this sector by continuously mapping and securing both traditional assets and AI-driven ecosystems, reducing their exposure and strengthening resilience.
Contact Securin to gain a clear understanding of how AI affects your attack surface. We will assess your environment to identify and close gaps, evaluate AI-related risks across your systems, prioritize remediations based on business impact, and implement controls that strengthen your defenses and reduce exposure to AI-enabled threats.


